

Blogs 
April 25, 2023
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
Risky Behaviors, Events, and Correlations, Oh My!
In today’s interconnected world, cybersecurity is an ever-increasing concern for businesses and individuals alike. While technology plays a significant role in keeping our data and systems secure, it is important to acknowledge the impact that humans have on cybersecurity and the challenge this brings to security leaders on how to keep employees on the yellow brick road to cyber safety.
Human error is one of the most significant factors that contribute to cybersecurity breaches. Employees may unintentionally expose sensitive information by clicking on a phishing link, leaving their devices unlocked or using weak passwords. In fact, according to the 2022 Verizon Data Breach Investigations Report, 82% of data breaches involve human error. Therefore, it is essential for businesses to invest in regular cybersecurity training for their employees to help them understand the potential risks and how to mitigate them.
Yet is standard cybersecurity training and awareness activities making a dent in changing human behavior? The answer is no and the reason may be surprising. Training can be an effective tool however without understanding who displays the riskiest behavior and what type of behavior they’re engaged in, it is difficult to apply a blanket approach to stop risky actions.
Just like in the Wizard of Oz, Dorothy, or in this case security leaders must rely on wits, courage, and help from friends to outsmart threat actors to protect data. Or in this instance, human risk insights to identify the risky or vigilant state of a user across various security categories, including authentication and access, data security and privacy, device security, phishing and email, security awareness and training, and web security.
Identifying risky behavior, events, and correlations is changing the way heroines, just like you, make informed decisions in an effort to turn your employees into a proactive line of defense.
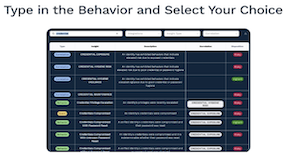
Uncover the hundreds of human risk behaviors, events, and correlations tracked in Living Security’s Unify Human Risk Management platform to reduce the human impact on cybersecurity at your organization.