

Blogs 
January 16, 2023
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
The Human-Centric Guide to Cyber Risk Management
For years, we've focused on building stronger digital walls. But what happens when the biggest risks are already inside? Technical safeguards are essential, but they can't account for human error. This reality calls for a fundamental shift in our cyber risk management strategy. It's time to move beyond just securing systems and start understanding the people who use them. This is where Human Risk Management in cybersecurity becomes so important. To build a truly effective defense, we first need to understand how our approach to risk has changed over time.
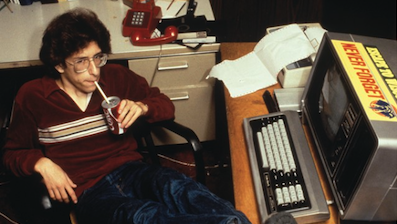
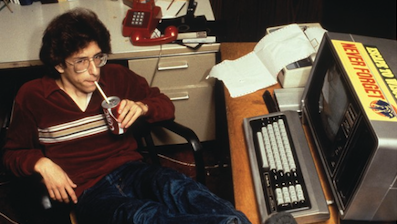 Cybersecurity in the 1960s-1970s
Cybersecurity in the 1960s-1970s
According to Jeff Yost, in his article, A History of Computer Security Standards, the field of cybersecurity got its start alongside the development of the first computers, developed by the US Department of Defense in the late 1960s. Beginning with the Advanced Research Projects Agency Network (ARPANET), a pre-internet network of interconnected computers widely regarded as the first real network as we know it, governmental agencies relying on this network naturally relied on it to be secure.
As computer technology moved from private, governmental usage to public usage, this need for security continued, but it also became more complicated. Like other attacks against communication systems, such as the manipulation of tones used by the telephone system in order to gain access to the network, make free calls, or otherwise exploit telecom networks, the initial attacks waged against the early computer networks were also primarily based on seeking out and exploiting technical weaknesses.
Eventually, telephone companies got wise to this phone hacking, or “phreaking” activity, and changed the way the entire system worked. But computer networks were more complex, and as time went on, and the internet expanded, this ever-increasing complexity led to more and more network vulnerabilities, just waiting to be exploited. In the 1980s, commercial antivirus software began to be developed in response to these growing threats and new viruses. Each antivirus program hoped to stay one step ahead of the exploits as they emerged.
The First Viruses Emerge: Cybersecurity in the 1980s
The 1980s saw the emergence of the first commercially available antivirus software. Companies such as Symantec, McAfee, and Trend Micro led the way in providing reliable protection against malicious programs. This period also saw an increase in computer viruses, as hackers began to target personal computers and business networks. In addition, this decade marked the rise of Internet security and the emergence of the international Computer Emergency Response Team (CERT).
The World Goes Online: Cybersecurity in the 1990s
The 1990s saw further development in cybersecurity, with the launch of firewalls, which act as a barrier to keep unwanted threats out. Companies such as Check Point Software Technologies created firewall systems that help protect against intrusions and malicious attacks. This decade also saw a huge increase in the number of cybercrimes, with hackers increasingly targeting critical infrastructure and corporate systems. As a result, governments around the world began to focus on improving their cybersecurity capabilities by introducing laws and regulations to protect citizens from online threats.
Cybercrime Gets Organized: Security in the 2000s
The start of the 21st century saw the emergence of sophisticated cyber threats. As technology continues to evolve, so too does the sophistication of malware and other malicious software. The 2000s saw a rise in phishing scams, ransomware, and zero-day attacks, prompting governments and companies to increase their investments in cybersecurity solutions. This decade also marked the beginnings of large-scale data breaches as hackers began targeting sensitive data.
The Decade of the Data Breach: Security in the 2010s
The 2010s saw the emergence of cloud computing, which enabled companies to store data remotely on shared networks. However, this also created new risks, as malicious actors were now able to target multiple systems at once. To protect against these threats, businesses began investing heavily in security measures such as multi-factor authentication, encryption, and cyber insurance. This decade also saw an increase in the use of artificial intelligence (AI) and machine learning algorithms to detect potential threats before they can cause any damage.
AI and Remote Work: Redefining Security in the 2020s
The 2020s have brought even more challenges to the world of cybersecurity, including state-sponsored attacks, quantum computing, and the rise of 5G networks. In response, governments and companies are investing heavily in innovative technologies such as blockchain and artificial intelligence to help protect their systems from malicious actors. As cybersecurity continues to evolve, we expect to see further advances in the technology used to protect our data and networks. Cybersecurity is an ever-changing field, but with the right information and resources, we can all stay safe online.
By understanding the history of cybersecurity, businesses, organizations, and individuals can create an informed approach to security. Whether it’s protecting against malicious threats or building a secure infrastructure for data storage, having a knowledge of the past can help us shape the future of cybersecurity.
Where Did the Term "Cybersecurity" Come From?
The use of “cyber”-everything started with “cybernetics,” popularized by mathematician Norbert Wiener in the 1940s. For his book Cybernetics, Wiener borrowed the ancient Greek word “cyber,” which is related to the idea of government or governing. He described a futuristic idea—that one day there would be a self-governing computer system that ran on feedback.
According to the Oxford English Dictionary, there’s evidence of the prefix “cyber-” usage going back to 1961; however, it became popular in the 1990s. The term became prevalent with the invention of the World Wide Web, and the early 1990s saw the predominance of words like cyberbully, cybercommunity, and cyberwar.
What is Cyber Risk Management?
Cyber risk management is the continuous process of identifying, assessing, and mitigating threats to an organization's digital assets and operations. The goal isn't to eliminate every single risk, which is impossible, but to reduce overall risk to an acceptable level that aligns with the company's business objectives. Think of it as the strategic, big-picture thinking that guides your entire security program. It answers critical questions like: What are our most valuable digital assets? What are the most significant threats to those assets? And how much are we willing to invest to protect them? This process provides a structured way for security leaders to make informed, data-driven decisions and communicate the value of their security efforts to the board in clear business terms.
Cyber Risk Management vs. Cybersecurity
It's easy to use "cyber risk management" and "cybersecurity" interchangeably, but they represent two different sides of the same coin. Cyber risk management is the high-level business process that decides where to focus security efforts based on a comprehensive understanding of risk. It’s the strategy. Cybersecurity, on the other hand, is the technical work of protecting networks, systems, and data. It’s the tactical implementation of that strategy through firewalls, endpoint protection, and other security controls. A strong cyber risk management program ensures that your cybersecurity resources are being applied to the most critical areas, giving you the most effective protection for your investment.
The Formal Cyber Risk Management Process
A formal cyber risk management process provides a repeatable and defensible framework for making security decisions. It’s not a one-time project but a continuous cycle that helps organizations adapt to an ever-changing threat landscape. This process typically involves several key stages, from setting the initial context for risk to continuously monitoring the effectiveness of security controls. By following a structured process, you can ensure that your approach to managing risk is consistent, comprehensive, and aligned with your organization's strategic goals, rather than just reacting to the latest threat in the news.
Risk Framing and Identification
The first step in the process is risk framing. This involves setting the rules and goals for how your organization will manage risk. It establishes the context by defining your risk tolerance, identifying key stakeholders, and outlining the scope of the program. This stage ensures that your risk management plan aligns with the company's overall business goals. Once the frame is set, you move to risk identification, where you actively seek out potential threats and vulnerabilities across your digital environment. This includes everything from technical weaknesses in your software to the potential for human error among your employees.
Risk Assessment
After identifying potential risks, the next step is to assess them. This involves analyzing each risk to understand its potential impact on the business and the likelihood of it occurring. A thorough assessment estimates the potential harm a threat could cause and helps prioritize which risks require immediate attention. To be truly effective, this analysis must go beyond a single data source. A modern approach to human risk management, for example, correlates data across employee behavior, identity and access privileges, and external threat intelligence to predict which individuals or agents pose the greatest risk before an incident happens.
Risk Response
Once risks are assessed and prioritized, your organization must decide how to respond to them. This isn't always about implementing a new technical control. The decision is a strategic one based on the risk's potential impact and the cost of addressing it. There are four primary ways to respond to a risk: you can mitigate it, remediate it, transfer it, or simply accept it. Each option has different implications for your budget, resources, and overall security posture, and the right choice depends entirely on the specific context of the risk and your organization's predefined risk tolerance.
Risk Monitoring
Cyber risk management is a dynamic process, not a static one. After you've implemented a risk response, you must continuously monitor its effectiveness. This stage involves regularly checking to see if your security controls are working as intended and keeping a close watch for new and emerging threats. Continuous monitoring provides the feedback loop necessary to adapt your strategy over time. It helps you understand if your investments are paying off and allows you to make adjustments to your security posture as your business evolves and the threat landscape changes.
Incident Response
No matter how robust your defenses are, security incidents can still happen. That's why a critical part of any cyber risk management program is developing a comprehensive incident response plan. This plan outlines the specific strategies and procedures for handling a security breach. The goal is to minimize damage, restore normal operations as quickly as possible, and maintain business continuity. A well-rehearsed incident response plan ensures that when an incident does occur, your team can act swiftly and effectively, reducing the financial and reputational impact on your organization.
Core Strategies for Responding to Risk
When you've identified and assessed a risk, you have four primary strategies for how to handle it. The right choice depends on a cost-benefit analysis that weighs the potential impact of the risk against the resources required to address it. This decision-making is at the heart of strategic risk management, ensuring that security investments are both practical and proportional to the threats they are meant to address. Let's look at each of the four core response strategies in more detail.
Mitigate
Mitigation is about reducing the likelihood or impact of a risk. This is often achieved by implementing security controls and tools that make it harder for an attack to succeed or lessen the potential damage if one does. For example, you might mitigate the risk of a phishing attack by implementing advanced email filtering and providing targeted security awareness training to employees. Mitigation doesn't eliminate the risk entirely, but it reduces it to a more acceptable level within your organization's risk tolerance.
Remediate
Remediation goes a step further than mitigation. Instead of just reducing the risk, remediation aims to fix the underlying vulnerability completely so it can no longer be exploited. If a vulnerability scan discovers a critical flaw in a piece of software, the remediation would be to apply the security patch that fixes the flaw. Remediation is often the preferred option for high-severity risks where a complete fix is available and feasible to implement, as it permanently removes the threat from your environment.
Transfer
Transferring risk involves shifting the financial burden of a potential incident to a third party. The most common way to do this is by purchasing cyber insurance. While insurance doesn't prevent an attack from happening, it can cover the significant costs associated with a data breach, such as regulatory fines, legal fees, and customer notification expenses. Transferring risk is a financial strategy that helps protect the organization from the catastrophic monetary losses that can result from a major security incident.
Accept
Sometimes, the most sensible business decision is to simply accept a risk. This strategy is typically reserved for risks that are very unlikely to occur or would have a very low impact on the business if they did. If the cost of mitigating or remediating a risk far outweighs the potential damage it could cause, accepting it might be the most logical choice. This is a calculated decision that should be formally documented and approved, acknowledging that the organization is aware of the risk and has chosen not to take action.
Understanding the Modern Cyber Risk Landscape
The landscape of cyber risk is constantly shifting, driven by new technologies, evolving business practices, and increasingly sophisticated adversaries. Today's enterprises face a complex web of threats that can have devastating consequences, extending far beyond simple IT disruptions. From crippling financial losses to severe reputational damage, the stakes have never been higher. Understanding the key characteristics of this modern risk landscape is the first step toward building a resilient and adaptive security program that can protect your organization's most critical assets in a challenging environment.
The Staggering Financial Impact of Cyber Threats
The financial consequences of a cyberattack can be immense. Beyond the immediate costs of remediation and recovery, organizations face regulatory fines, legal battles, and long-term damage to their brand reputation. The numbers speak for themselves. For example, according to IBM, the average cost of a data breach in the healthcare industry is a staggering $10.10 million. This figure highlights why cyber risk is no longer just an IT issue; it's a critical business issue that demands the attention of the entire executive team and the board of directors.
Common Cyber Threats Facing Enterprises
While the list of potential cyber threats is long, a few key categories consistently pose the greatest risk to large organizations. These are the threats that security teams spend the most time and resources defending against. They range from external attacks orchestrated by organized criminal groups to internal risks stemming from employee behavior. A clear understanding of these common threats is essential for developing a focused and effective cyber risk management strategy that prioritizes the defenses that matter most to your enterprise.
Ransomware and Malware Attacks
Ransomware and other forms of malware remain one of the most disruptive threats facing enterprises today. In a ransomware attack, malicious software encrypts an organization's critical data, and the attackers demand a hefty payment in exchange for the decryption key. These attacks can bring business operations to a complete standstill, leading to massive financial losses and significant downtime. Malware, more broadly, encompasses a range of malicious software designed to steal data, disrupt systems, or gain unauthorized access to a network.
Insider Threats
Not all threats come from the outside. Insider threats, which originate from current or former employees, contractors, or partners, can be particularly damaging because these individuals already have legitimate access to sensitive systems and data. These threats can be either malicious, where an employee intentionally steals data or sabotages systems, or accidental, where an employee unintentionally exposes data through negligence or a simple mistake. Predicting and preventing these threats requires a deep understanding of human behavior, which is why leading Human Risk Management platforms focus on analyzing signals across behavior, identity, and threat data to spot emerging risks before they lead to an incident.
Third-Party and Supply Chain Risks
Your organization's risk exposure doesn't end at your own network perimeter. In today's interconnected business ecosystem, companies rely on a vast network of third-party vendors, suppliers, and partners. Each of these connections introduces a potential new vector for an attack. A breach at one of your vendors could easily lead to a breach of your own systems. As a result, organizations are responsible not just for their own security but also for the security posture of their entire supply chain, making third-party risk management a critical component of any comprehensive security program.
Cloud Service Misconfigurations
The rapid adoption of cloud services has brought incredible benefits in terms of flexibility and scalability, but it has also introduced new categories of risk. One of the most common and costly cloud-related threats is a simple misconfiguration. An improperly secured cloud database or storage container can inadvertently expose massive amounts of sensitive data to the public internet. These misconfigurations are often the result of human error or a lack of expertise in complex cloud environments, highlighting the critical need for strong governance and automated security checks for all cloud deployments.
Key Frameworks and Regulations
Navigating the complex world of cyber risk doesn't have to be a journey without a map. A number of well-established frameworks and regulations provide organizations with a structured approach to managing their security posture. These frameworks offer a common language and a set of best practices that can help you build a comprehensive and defensible risk management program. They are not just about compliance; they are valuable tools that can guide your strategic planning, help you prioritize your security investments, and demonstrate due diligence to regulators, customers, and partners.
Widely-Used Industry Frameworks
Several industry-developed frameworks have become de facto standards for cyber risk management. These frameworks are designed to be flexible and adaptable to organizations of all sizes and across all sectors. They provide a roadmap for identifying, assessing, and responding to cyber risks in a systematic way. Adopting one of these frameworks can help you mature your security program, benchmark your posture against industry peers, and communicate your security efforts in a way that is easily understood by both technical and non-technical stakeholders.
NIST Frameworks
The NIST Cybersecurity Framework (CSF), developed by the U.S. National Institute of Standards and Technology, is one of the most widely adopted frameworks in the world. It provides a voluntary set of standards, guidelines, and best practices to help organizations manage their cybersecurity-related risks. The framework is organized around five core functions: Identify, Protect, Detect, Respond, and Recover. This logical flow provides a high-level, strategic view of an organization's cybersecurity risk management lifecycle, making it a powerful tool for organizing and communicating your security efforts.
ISO/IEC 27001
ISO/IEC 27001 is an international standard that specifies the requirements for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS). Unlike the NIST CSF, which is a set of voluntary guidelines, organizations can achieve a formal certification for ISO/IEC 27001 to demonstrate their compliance with the standard. This certification can be a valuable asset for building trust with customers and partners, particularly for companies that operate globally or handle highly sensitive data.
OCTAVE
The OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation) framework is a risk-based strategic assessment and planning technique for security. Developed at Carnegie Mellon University, OCTAVE is designed to be a self-directed methodology, meaning it can be run by an organization's internal team rather than relying on outside consultants. It focuses on identifying the assets that are most critical to the organization's mission and then evaluating the threats and vulnerabilities related to those specific assets, making it a highly focused and context-driven approach to risk assessment.
The Government's Role and Shared Responsibility
Governments around the world play a crucial role in shaping the cyber risk landscape. They establish regulations and compliance mandates, such as the GDPR in Europe or the CCPA in California, that set legal requirements for how organizations must protect personal data. They also act as a vital source of threat intelligence, sharing information about emerging threats and attack campaigns through agencies like CISA in the United States. Ultimately, cybersecurity is a shared responsibility, requiring a strong partnership between the public and private sectors to create a more secure and resilient digital ecosystem for everyone.
Essential Security Actions and Controls
While strategy and frameworks provide the high-level guidance for your risk management program, it's the specific security actions and controls you implement that form your practical lines of defense. These are the tactical measures that protect your systems, data, and users from threats on a daily basis. A layered approach, combining a variety of technical and procedural controls, is essential for building a defense-in-depth security posture. These foundational security practices are the building blocks of any effective cybersecurity program, regardless of your organization's size or industry.
Vulnerability Scans and Penetration Testing
You can't protect against weaknesses you don't know you have. That's why regularly checking for vulnerabilities is a fundamental security practice. This is typically done in two ways. Vulnerability scans are automated processes that check your systems against a database of known flaws. Penetration testing, or "pen testing," is a more hands-on approach where ethical hackers attempt to actively exploit weaknesses in your systems, simulating a real-world attack. Together, these two activities provide a comprehensive view of your technical vulnerabilities, allowing you to prioritize and remediate them before they can be exploited by adversaries.
Technical Security Tools
A wide array of technical security tools are available to help protect your digital environment. These are the technologies that form the core of your cybersecurity defenses. This includes foundational tools like firewalls, which control network traffic, and antivirus or endpoint detection and response (EDR) software, which protects individual devices from malware. It also includes more advanced systems that detect and stop intruders on your network. Deploying and properly configuring these tools is a critical step in mitigating a broad range of common cyber threats.
Data Backup and Recovery
In the event of a destructive cyberattack like ransomware, having a reliable data backup and recovery plan can be the difference between a minor disruption and a catastrophic business failure. Regularly backing up your critical data is essential, but it's only half the battle. You must also regularly test those backups to ensure that you can actually restore your data when you need it most. A well-tested backup and recovery strategy is your ultimate safety net, providing the resilience your organization needs to bounce back quickly from a major security incident.
Why Your Security Strategy Must Constantly Evolve
As cyber threats continue to evolve, it’s vital that security measures continue to transform as well—including the approach to security awareness and training. A 2022 Data Breach Investigations Report from Verizon found that 82% of breaches involved errors in human behavior, making it the biggest threat to cybersecurity. Because of this, the best way to reduce cyber risk is to take human behavior into account, not by assuming that humans will always be risky, but by understanding what behaviors lead to cybersecurity risks, and which ones can be changed. It’s simply not good enough, or effective enough, to let 82% of breaches fly by with a, “Well, what can you do?” approach.
Turns out, there’s a lot we can do.
The Shift to Security Awareness Training
As concerns about cybersecurity have continued to expand, so too have perspectives on security awareness and training. In the early days of computing, the field of cybersecurity ran parallel to the development of computers themselves, but today, the field of cybersecurity is its own complex arena.
The field of security awareness and training developed out of a need to inform employees across an organization of threats and to train them how to respond to them. Today, most companies have a dedicated team of cyber risk management specialists who monitor and report on threats and deal with incidents as they arise. As computer access became more widespread, security teams recognized that more and more threats were targeted at regular users, many of whom might not have the same level of technical savvy as those with an IT background.
Security leaders train employees to be aware of threats and how to respond to them by informing them of potential risk areas and giving them information about how to prevent an incident. This type of training typically covers a few key categories, including:
- Physical Security: Having a good awareness of things like access to buildings and/or restricted areas of a company; badge swiping protocols; document printing, sharing, and disposal protocols, etc.
- Best Practices: Teaching employees the importance of using complex passwords, logging into and out of workstations, and other basic security knowledge.
- Remote Computing: A subject of more recent discussion, given the emergence of remote work in the past few years.
The most important of all of the categories covered in cybersecurity training is Social Engineering. Social engineering is the psychological manipulation of human behavior that allows cybercriminals to thrive. As noted hacker-turned-security-expert Kevin Mitnick states in his book The Art of Deception, “Why are social engineering attacks so successful? It isn’t because people are stupid or lack common sense. But we, as human beings, are all vulnerable to being deceived because people can misplace their trust if manipulated in certain ways.”
If history has taught us anything, it’s that technologies may come and go, but people are people, and human behavior is, and always has been, a key component in cybersecurity. It’s only recently that organizations are starting to clue into this, however. The most successful approaches to risk management in cyber security must involve an understanding of human behaviors.
Why Human-Centric Cyber Risk Management Matters
Human Risk Management faces this risk head-on by changing the cybersecurity risk management model. Instead of assuming that human behavior will always be the weakest link in the security network, Human Risk Management starts with the idea that human behaviors can be changed in order to support a safer security culture, a more empowered workforce, and an organization where every employee can be at the front line of defense against all kinds of attacks.
A 3-Component Cyber Risk Management Model
Monitor the behavior of users within an organization
What are your employees doing when faced with certain threats, such as phishing, remote work, and other key security principles that could lead to vulnerabilities?
Analyze and report on their behavior
Analyze and report on any weaknesses, show trends, and preempt threats before they occur. Knowing what we now know, which groups’ behaviors might potentially put company data at risk?
Deploy strategic, effective cybersecurity training
Provide training to these users and groups to redirect them from disempowered to empowered. CISOs can turn human risk into a security culture that empowers each and every employee to know what to do, and when to do it.
What's Next for Cyber Risk Management?
Cybersecurity is changing, and if history is any indication, it will continue to change, grow, and adapt to new challenges. More and more companies are considering how best to integrate things like long-term remote work, new security architectures, and higher supply chain risk, into their cybersecurity frameworks.
It’s vital that security leaders continuously evaluate the security management of their organization. Thankfully, there are tools emerging on the market that allow these leaders to gain insight into their worker’s behavior, assess the risk, and apply the findings. Once they know how to assess cyber risk with the human element in mind, the whole culture can change for the better.
Common Cyber Risk Management Mistakes to Avoid
Even the most seasoned security teams can fall into common traps that undermine their cyber risk management strategies. Building a resilient security posture isn't just about implementing the latest technology; it's about avoiding the systemic errors that can leave your organization exposed. Recognizing these pitfalls is the first step toward creating a more proactive and effective defense. Many of these mistakes stem from an outdated, reactive view of security, where teams are constantly playing catch-up with emerging threats. A modern approach requires a fundamental shift in mindset, focusing on prediction and prevention rather than just detection and response. By sidestepping these common errors, you can allocate resources more effectively and build a security culture that truly reduces risk across the enterprise.
Ignoring Risks That Seem Small
It’s easy to get overwhelmed by the sheer volume of potential vulnerabilities, and it's tempting to dismiss minor issues to focus on the "big" threats. However, this approach overlooks a critical factor: context. A seemingly small risk, like an employee occasionally sharing credentials, becomes a major threat when that employee has privileged access to critical systems. As noted by security experts at IBM, effective risk management is about focusing on the weaknesses most likely to cause harm. To do this, you need to see the complete picture. A truly predictive security strategy involves correlating data across multiple pillars, including user behavior, identity and access permissions, and known threats. This allows you to identify which "small" risks carry the greatest potential impact and prioritize them before they can be exploited.
Failing to Update Security Plans
A cyber risk management plan isn't a document you create once and file away. The threat landscape is constantly changing, with new attack vectors and techniques emerging daily. A static security plan quickly becomes obsolete, leaving your organization vulnerable to threats it can no longer anticipate. Your strategy must be a living, breathing process that adapts in real time. This means continuously monitoring for new threats and changes within your own environment. Instead of relying on annual reviews, a proactive approach uses ongoing data analysis to inform your defenses. By leveraging a platform that provides continuous insight into risk trajectories, you can dynamically adjust your controls and interventions, ensuring your security plan evolves at the same pace as the threats you face.
Poor Communication Between Technical and Business Teams
Cyber risk is not just an IT problem; it's a business problem. Yet, security teams often struggle to communicate the importance of their initiatives to executive leadership in a language they understand. When technical teams operate in a silo, they miss the opportunity to align security goals with broader business objectives. This disconnect can lead to underfunded projects and a lack of buy-in from other departments. The key is to translate technical risks into measurable business outcomes. Instead of discussing malware signatures and firewall rules, present board-ready metrics that show a quantifiable reduction in human risk. When you can demonstrate how your efforts directly protect revenue and reputation, you build a bridge between security and the business, fostering a shared sense of responsibility for protecting the organization.
Not Testing Incident Response Plans
An untested incident response plan is merely a hypothesis. When a real incident occurs, you don't want to be discovering gaps and flaws in your strategy for the first time. Regular testing, through exercises like tabletop simulations and controlled drills, is essential to ensure your team can respond quickly and effectively under pressure. These tests reveal weaknesses in your processes, communication channels, and technical controls before a real attacker does. Furthermore, it's not enough to simply run a phishing simulation and see who clicks. You need to understand the behavioral patterns behind those actions and use that intelligence to refine your response plan and deliver targeted, preventative training. This creates a powerful feedback loop where you are not just practicing your response but actively reducing the likelihood of needing it.
Building a Proactive Cyber Risk Management Program
Human-driven risk thrives in fear, uncertainty, and manipulation but effective Human Risk Management only grows stronger with knowledge, confidence, and empowerment. Whether it’s preventing employees from doing what they shouldn’t be doing, to encouraging them to do things correctly that they might be skipping over or forgetting, simple changes and engaging training can go a long way to preventing cyber attacks before they start. At Living Security, our Unify Human Risk Management platform can change the cybersecurity game for your organization starting today.
Want to learn more? Let's talk.
Frequently Asked Questions
What’s the difference between cyber risk management and cybersecurity? Think of it as the difference between strategy and tactics. Cyber risk management is the high-level business process of deciding what to protect and why, based on a clear understanding of your organization's goals and risk tolerance. It’s the strategic thinking that guides your entire program. Cybersecurity is the tactical implementation of that strategy, involving the specific tools, controls, and actions you take to protect your systems and data.
Why is a formal risk management process so important? A formal process provides a consistent, repeatable, and defensible framework for making security decisions. Instead of reacting to the latest threat in the news, you have a structured cycle for identifying, assessing, and responding to risks in a way that aligns with your business objectives. This ensures your security resources are applied to the areas of greatest potential impact, making your entire program more effective.
My security program focuses on technical controls. Why do I need to worry about the "human element"? Technical controls are a critical layer of defense, but they can't account for human behavior. Since a significant majority of breaches involve a human factor, ignoring it leaves a major gap in your security posture. A human-centric approach isn't about blaming employees; it's about understanding the behaviors that create risk. This allows you to implement targeted training and interventions that address the root cause of many incidents before they happen.
How can we prioritize risks when there are so many potential threats? Effective prioritization requires context that goes beyond a simple vulnerability score. A modern approach involves correlating data across multiple sources, including employee behavior, identity and access privileges, and external threat intelligence. This gives you a complete picture of your risk landscape. It helps you identify which individuals or systems, if compromised, would have the greatest impact on the business, allowing you to focus your resources where they matter most.
What's the first step to making our cyber risk management more proactive instead of reactive? The initial step is to move from a static to a dynamic approach. Your risk management plan should be a living process, not a document you review once a year. Begin by establishing a system for continuous monitoring that provides ongoing feedback on your security controls and the evolving threat landscape. This allows you to spot emerging risk trajectories and make adjustments to your strategy in near real-time, putting you in a position to prevent incidents rather than just respond to them.
Key Takeaways
- Prioritize the human element in your defense: Since 82% of breaches involve human behavior, technical controls alone are insufficient. A modern security strategy must actively manage human risk by understanding behavioral patterns and guiding employees toward safer practices.
- Implement a formal risk management framework: Use established frameworks like NIST or ISO 27001 to build a structured, repeatable process. This ensures your security investments align with business objectives and that your program can adapt to the constantly changing threat landscape.
- Shift from detection to prediction with data: Proactively identify your greatest risks by correlating data across three key pillars: user behavior, identity and access, and external threats. This comprehensive analysis allows you to predict and prevent incidents, rather than just reacting to them.
