

Blogs 
May 1, 2024
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
What is an Attack Surface? And How to Reduce it?
What is an Attack Surface? And How to Reduce it?
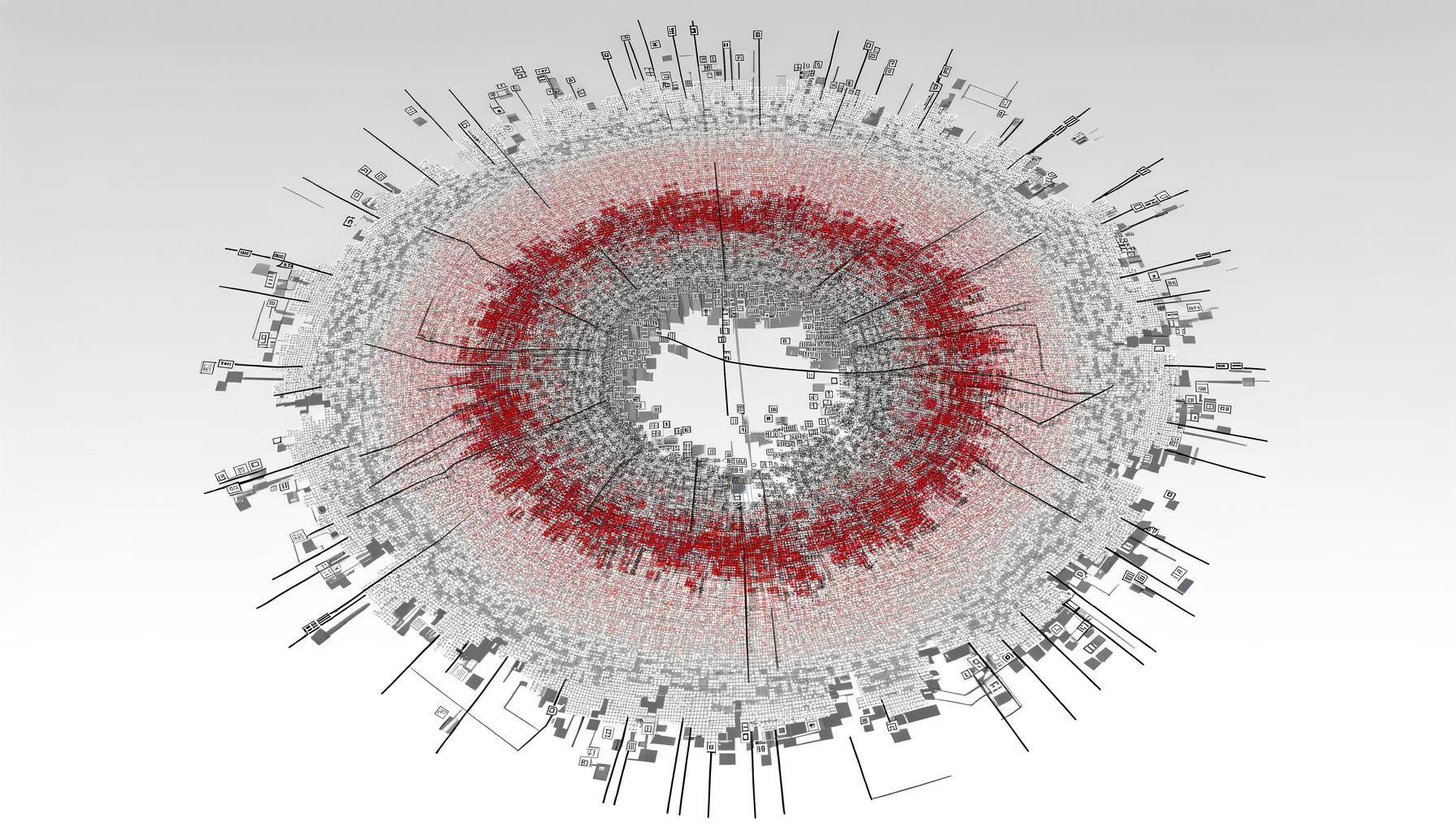
In today's digital age, understanding and managing an organization's attack surface is critical to safeguarding against cyber threats. An attack surface encompasses all the possible points where an unauthorized user can try to enter data to or extract data from an environment. Essentially, it's a sum of the organization's security risk exposure, including all vulnerabilities that can be exploited by cyber attackers to gain unauthorized access to systems and data. Reducing this surface is vital for minimizing the potential for breaches, ensuring data integrity, and maintaining customer trust. Effective attack surface management, analysis, and monitoring techniques not only improve security but also enhance overall protection against the evolving landscape of cyber threats, including malware and ransomware attacks. The process involves a detailed assessment of all points of entry that could be exploited by cybercriminals and the implementation of strategies to mitigate these vulnerabilities.
What is an Attack Surface?
An attack surface refers to the collective vulnerabilities within an organization's IT infrastructure, including hardware, software, and networks that can be exploited by cybercriminals. It is a critical concept in cybersecurity, highlighting the importance of analyzing and monitoring an organization's vulnerabilities to mitigate risks. Effective attack surface management involves identifying potential security weaknesses before they can be exploited by adversaries. By employing key strategies such as regular vulnerability scanning, patch management, and access controls, organizations can significantly reduce their attack surface and the likelihood of cyber attacks, thereby bolstering trust in their security posture. This proactive approach ensures that security measures keep pace with the rapidly evolving cyber threat landscape, safeguarding sensitive data and infrastructure.
Attack Surfaces vs. Attack Vectors
While both critical in cybersecurity, attack surfaces and attack vectors serve distinct roles. The attack surface encompasses the entirety of vulnerabilities within an organization's security that can be exploited. Conversely, attack vectors are the methods or pathways an attacker uses to deliver a payload or malicious outcome, such as malware or ransomware, to the target. An expansive attack surface can provide numerous opportunities (attack vectors) for cybercriminals, illustrating the importance of securing vulnerabilities to mitigate threats. Understanding the relationship between attack surfaces and vectors is fundamental for a holistic security strategy, emphasizing the necessity of addressing both to protect against cyber threats effectively. This distinction helps organizations tailor their security strategies to cover both the breadth of potential vulnerabilities and the specific methods attackers might use.
What are the Types of Attack Surfaces?
Identifying and understanding the different types of attack surfaces is crucial for comprehensive security management. The categorization of attack surfaces into digital, physical, and social engineering domains helps organizations to tailor their cybersecurity strategies effectively. By understanding the distinct nature of each type, businesses can allocate resources and implement security measures more efficiently, ensuring that all potential vulnerabilities are covered.
Digital Attack Surface
This includes all digital components like software, hardware, and network infrastructures accessible via the internet. Vulnerabilities may stem from outdated systems, unsecured APIs, or exposed internet services. Strategies such as consistent software updates, network segmentation, encryption, and strict access controls are vital for managing the digital attack surface effectively. As businesses increasingly migrate to digital platforms, the complexity and scope of the digital attack surface expand, necessitating advanced security measures to protect against sophisticated cyber attacks.
Physical Attack Surface
The physical attack surface represents the tangible avenues through which unauthorized access could occur, such as unsecured entryways or unattended laptops and servers. Employing physical security measures like surveillance, secure locks, and access control systems is paramount in minimizing this risk. The convergence of physical and digital security strategies is critical in today's interconnected world, where physical breaches can lead to digital vulnerabilities and vice versa.
Social Engineering Attack Surface
This surface involves exploiting human factors, using deception to breach security protocols. Tactics like phishing and pretexting are common, underscoring the importance of employee awareness and training in recognizing and mitigating such threats. Social engineering remains one of the most challenging attack surfaces to defend against due to its reliance on human psychology rather than technical vulnerabilities, highlighting the need for comprehensive security awareness programs.
Attack Surface Reduction Steps
Reducing the attack surface involves several strategies, including minimizing unnecessary services, enforcing robust access controls, and ensuring timely updates and patches. Each technique contributes to narrowing the avenues available for exploitation, enhancing organizational security. Attack surface reduction is a dynamic process, requiring ongoing assessment and adjustment to address new vulnerabilities and threats as they arise.
Implementing Attack Surface Analysis
Conducting thorough attack surface analysis involves identifying potential vulnerabilities and entry points for cyber threats. Continuous analysis and adaptation are crucial in keeping pace with evolving threats, significantly reducing the organization's exposure to attacks. This comprehensive evaluation allows security teams to prioritize risks and allocate resources more effectively, ensuring that the most critical vulnerabilities are addressed promptly.
Monitoring the Attack Surface
Ongoing attack surface monitoring is essential for maintaining a minimized attack surface, enabling real-time threat detection and prompt incident response. Proactive measures and continuous oversight are key to effective attack surface management. By keeping a vigilant eye on the security landscape and responding swiftly to potential threats, organizations can significantly enhance their resilience against cyber attacks. This real-time monitoring complements the analytical phase of attack surface analysis by providing actionable intelligence that can be used to fortify defenses and protect critical assets.
Key Benefits of Attack Surface Reduction
Reducing the attack surface offers numerous advantages, including an improved security posture, diminished risk of cyber attacks, and enhanced data protection. Effective attack surface reduction strategies can lead to significant cost savings, better compliance, and increased trust from customers and partners. Furthermore, a streamlined attack surface simplifies security management, allowing security teams to focus their efforts on the most pressing threats. This proactive approach not only mitigates the risk of successful cyber attacks but also positions organizations as responsible stewards of their stakeholders' data.
Recommended Tools and Platforms for Attack Surface Management
For effective attack surface management, leveraging specialized tools like Living Security’s human risk management platform, phishing awareness training tools, and security awareness training platform is recommended. These solutions offer comprehensive features for identifying, analyzing, and mitigating risks, tailored to meet the needs of various business types. Utilizing such tools enhances an organization's ability to respond to threats dynamically, ensuring that the security posture is both robust and adaptable to the ever-changing cyber threat environment.
Secure Your Attack Surface with Living Security
In conclusion, effectively managing and reducing your attack surface is integral to enhancing your cybersecurity posture. Living Security's suite of tools, including their human risk management platform and security awareness training, offers a robust solution for addressing the complexities of the digital threat landscape. By prioritizing attack surface reduction and employing strategic security management practices, organizations can safeguard their assets and data against cyber threats. Explore Living Security's solutions to enhance your security measures and protect your organization's future, fostering an environment where trust, resilience, and security thrive.