

Blogs 
January 17, 2024
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
Introducing Unify Power Insights

At Living Security, we look forward to all that 2024 will bring. This year will see a big increase in security teams transitioning from security awareness and training to human risk management.
To kickstart this journey, we're excited to announce Unify Power Insights, a game-changing feature designed to provide you with specific windows into key areas of human risk behaviors for CISOs, Insider Threat teams, and Human Risk Managers.
We've revamped our Insight Dashboard to focus on Power Insights, taking your ability to understand and manage human risk to a whole new level. Building on the success of our Lenses feature, Power Insights offers a consolidated view across multiple integrations, allowing you to identify and track related behaviors in a single view.
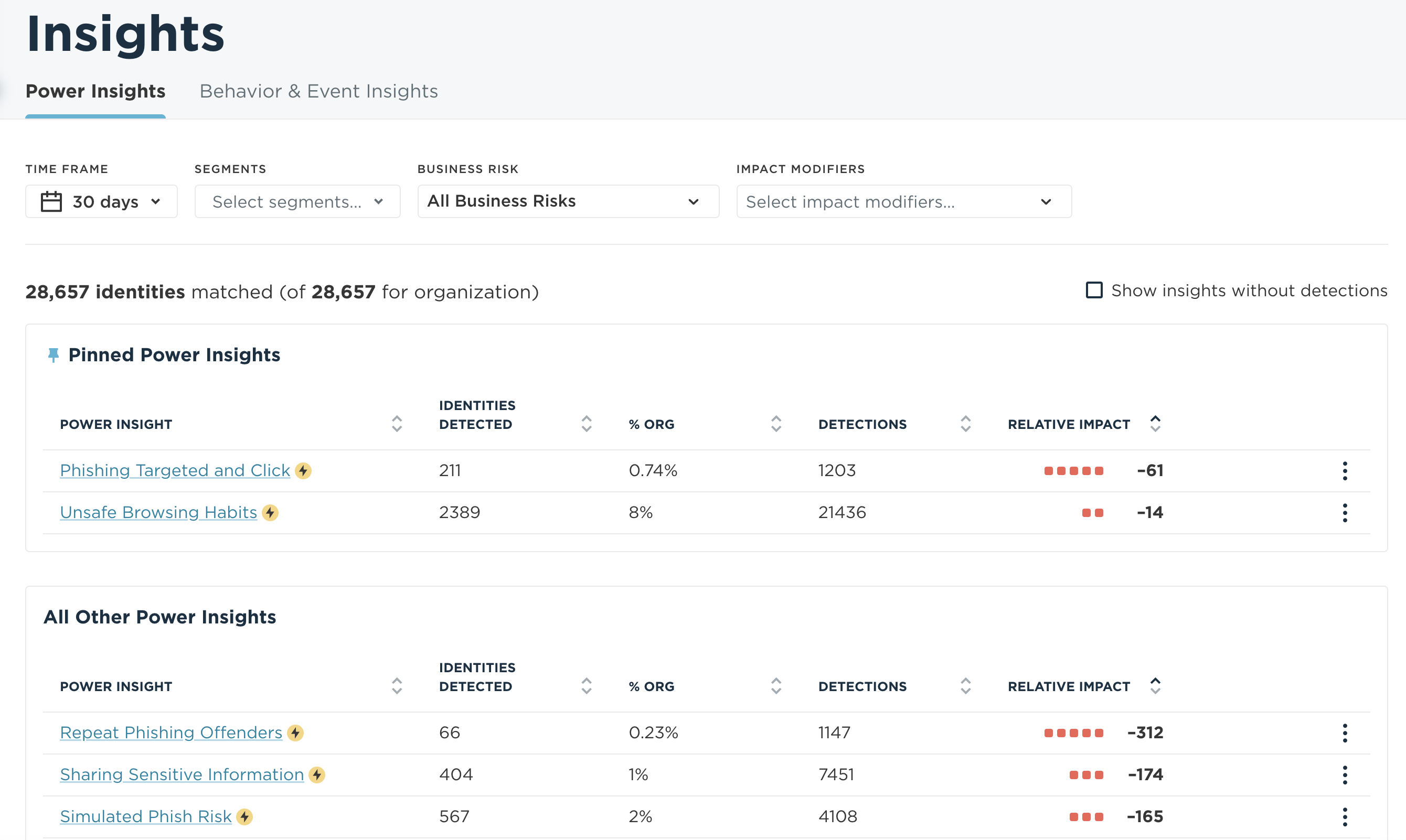
- Phishing Behaviors Analysis: Identify individuals repeatedly failing phishing simulations and focus on those being actively targeted by real phish.
- Malware and Unsafe Browsing Correlation: Uncover the link between malware incidents and unsafe browsing habits among users with elevated credentials.
- Sensitive Information Sharing Metrics: Gain insights into the frequency of sensitive information being shared across the organization.
Why Power Insights Matter:
This feature empowers you to track crucial groupings of user behaviors, detect spikes in risky activities in key areas of the business, and provides straightforward ways to mitigate associated risks.
Unify Power Insights empowers every team in the security organization:
- Security Operations Center and Incident Response: Investigate employees with privileged access to sensitive information that Unify Power Insights flags for high risk across phishing, account compromise, malware, or data loss.
- Governance, Risk, and Compliance: Automate policies that increase account security (such as multi-factor authentication) or restrict access to sensitive information amongst employees exhibiting high risk.
- Security Awareness & Training: Target topically relevant training and nudges to employees at high risk and save time by enabling vigilant employees to bypass training.
- Chief Information Security Officer: Improve the overall performance of the security organization by increasing the effectiveness of security prevention, detection, and response.
Let's Dive In Together:
If you're eager to explore the potential of Power Insights further, read our press release, sign up for our first look webinar on Feb. 28, or request a personalized demo to see firsthand how powerful these insights are for your organization!