

Blogs 
November 11, 2022
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
Making the Business Case for Human Risk Management
Human Risk Management is the evolution of cybersecurity awareness and training, but how do you make the case to invest up and across the business? Hear from Western Governors University and VillageMD to see how they accomplished this.
Read the full transcript here.
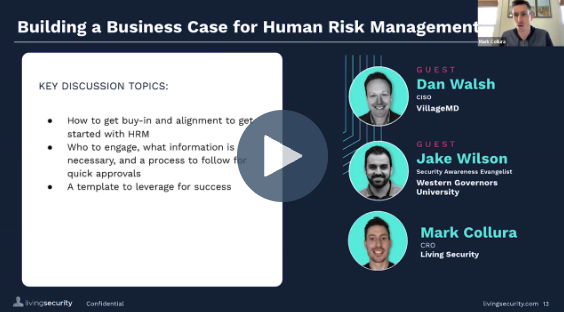
Mark Collara (00:05): This is part of the conversation that I'm really excited about. We've had hundreds and hundreds of conversations with prospects and clients, and moving from training and awareness with really that have to do the compliance side, to moving towards human risk management. But one of the terms that I've heard used is, how do we land the plane? Very few people come and say, "I'm not interested in analytics and behavior and change over time and targeted focus training and the ROI of training." But they really struggle with, "How do I present this internally? How do I get other people excited? How do I build the business case for this?"
So for this segment, I really want to focus on two areas here. So Jake, as a program owner, leader of the training and awareness space, as well as Dan at the CISO level, how do you view human risk management and the transition there, and how did you get both of your organizations ... VillageMD we've been partnered with for a few years now on the training side, but as of about six months ago, moving more towards data. And Jake, your organization came on full blown into the human risk space.
So during this segment, I really want to focus on how we get that alignment across the organization, who to engage with and what's necessary and what's too much information, and then understanding what's that template? How do we move from start to finish as we go through this journey?
So Jake, I want to start with you from a value perceived perspective. When you first heard about Unify, what jumped out at you and what were your initial thoughts once you got an overview of it?
Jake Wilson (02:04): Yeah, so I first heard about Unify, I actually attended the National Cybersecurity Alliance Conference in Scottsdale, and I was just casually talking with Drew. I don't think he was trying to sell me on it. We were just having a conversation about human risk and training programs and things like that. If he was trying to sell it, he did a pretty good job, nonchalantly. We were just kind of casually chatting about it. and for years and years, program owners learn about maturity models and whether it's nonexistent, compliance focus, and metrics and things like that, but it's always difficult to try to get over that hump of the compliance focus. Or even if you have some metrics that you're providing, it's hard to just get past that and keep building out a mature program.
So when I learned about Unify and this human risk management tool, to me it kind of seemed like a no-brainer. I knew within our organization that it could give us that shift from just doing some metrics and little lunch and learns and things like that to really drilling down and looking at the behavior change across teams and locations, job titles or their roles, and actually give us some actual meaningful data around our program.
Mark Collara (03:20): So I did liken, back to what Molly had talked about earlier, it's focus on risk, focus on risk, focus on risk, as opposed to engagement and potentially vanity metrics that come with the program. One of the things that our clients really struggle with, when you think about the data, how were you getting data to begin with? Because I know you guys did center on some data, but what did that process look like? Who did you need to get on board with sharing this, and what did that process look like before we kind of integrated together?
Jake Wilson (03:57): I mean, to be honest with you, it's been difficult. I'm a team of one. I know there's programs out there, they have multiple individuals dedicated. Like Molly said, she has a team of eight. I'm a team of one individual. I don't even know if that's really considered a team. It's just, I own it. But it's hard to capture the data. You're going across the different teams within the department and you're trying to say, "Hey, I want to get this data to look at this," and sometimes it's just almost impossible. It's hard to scale, it's difficult to achieve.
That's why I knew where Unify could obviously help us out a lot is it'd be easy to implement, it would save a lot of time for the people I'm trying to ping about getting data and things like that. And to be honest with you, I think I'd say our data gets a little bit stale. It's like every month we might go to the board or go to our executive team and we'll provide phishing metrics and things like that. But my manager, my leadership is always asking, "What's next? What are you going to do next? Where are you going to take this awareness program?" But yeah, obviously being able to get a bunch of different data from different APIs and integrations is invaluable.
Mark Collara (05:11): Yeah, and I think that what's next, I want to touch on that in a minute, and that goes to something we talked about with Dan a few weeks ago as we thought about this conversation. But one of the things that immediately jumped to when we thought about ClientDay is a lot of people say, "Yep, we need to go in this direction. This is where we need to mature the program."
But you were one of the early people that had a team join the next conversation. It was very interesting to see somebody that could get everyone on board, get other people excited. They came with questions, they wanted to know how it impacted them. So you have a conversation with Drew, we do a quick demo, it kind of clicked. What did you do behind the scenes to get that group together, which made this a very quick decision?
Jake Wilson (06:08): Yeah, definitely. I went to that conference in Scottsdale, right down the road from me actually, which was great, but came back and I kind of briefly mentioned it to my manager. And my manager goes, "Well, you know what, we have a team meeting every Thursday. Why don't you talk about some of the presentations or things that you learned at the conference?" I thought that was a prime opportunity to really go back to our original program plan and the different maturity levels of awareness programs, and just talk to my team. There's about 25 people on our team, our SOC, we have an email security team, I mean, application security team, et cetera.
I obviously went through some of the presentations, but one of the things I really wanted to hit home on was human risk management and where we're at in terms of the maturity level of an organization, kind of where we started, where we're at now, I've been with WGU for a few years, and really the direction that we need to go in the future if we actually want to have an award-winning stellar program that actually changes the culture of an organization.
So I had that quick demo, talked about maturity levels and things like that, and one of the things I mentioned during that meeting was where we're at, and this is actually written down in a [inaudible 00:07:33] plan. One of the first things I did when I joined WGU, and I would urge every program owner to do this, is to actually have a strategic guiding document that kind of outlines what you're doing in your program plan, in your program, and where you want to take it in the future. I presented that also.
I said, "Hey, you could base it on the SANS Security Awareness Maturity model. [inaudible 00:07:58] wrote a book, he has another maturity model. You could even create your own. But it's nice to tie into one that's been out there for a while, and a lot of industry professionals worked on it. But have that in your program plan and then talk about it, talk about where you want to take it."
But after that first team meeting, I just set up a demo for myself, I think, initially, just to see, okay, let's see what this is all about. It sounds really cool. Let's see if it actually makes sense. And it did instantly. I was like, this is a no-brainer. Why haven't organizations been doing this for years? Or they probably have, or some organizations have, but they're doing it manually. I'm sure it's a super intensive, time consuming process, I would imagine.
So I just set up another meeting. I set up another demo. I said, "Hey, this is what I was talking about. This is where I want to take our program." I invited, just kind of an open invitation, I had a couple individuals from our risk management team join, I had the manager of our SOC team join, somebody from our email security team, and some other team members from our GRC team.
And immediately afterwards, the meeting ended. I posted a message in Teams chat, I said, "Hey, what do you guys all think?" And every single person found value in it. They could see how not only would it help mature our own awareness program at the university, but help their own teams as well, as far as getting data.
Mark Collara (09:26): I always find it funny, Jake, when you brought people, and we've had more of the owners of the point solutions, Proofpoint or CrowdStrike or the SOC team, once they realize that they don't have to own it and they're not getting all of the alerts, they're like, "Oh, okay Jake, go do that thing and share back the data." It is an interesting dynamic of once they understand what it is, it changes the perception of the tool.
Jake Wilson (09:54): Yeah, absolutely. And it took a couple more meetings after that. It started sparking some more conversations. It was obviously conversations within our team, and then you get more people involved, they start talking about it a little bit more. I've even seen things come across Teams channels at the enterprise level, going, "Hey, can anybody look into this? Are we able to do this in SharePoint?" I thought to myself, I bet Unify can do that. I even posted that. This was across our whole EdTech department of 400 people, and I said, "Hey, we just signed on with this new company, Living Security. I'm pretty sure once we set up that integration, we'll be able to look at that kind of stuff." But we started having these conversations about it.
And I just set up some more, I mean, it took a while, but I brought in my director and as soon as my director saw it, I mean, he saw value in it. But I would say the biggest thing, if you're trying to tie in other people and get their buy-in, you just have to be passionate about security awareness and you have to be passionate about trying to change the culture and changing behaviors and human risk management. I mean, if you're just, you're not passionate about it and you really don't care, they're not going to find value in it. They're not going to be excited about it if you're not.
Mark Collara (11:06): Yeah, no, it is really important. It's really important to show the passion, the drive, the plan to execute the ownership of it. It's not going to be additional work on somebody else's plate. Yeah, that's great.
Dan, I think I've had a few really important light bulb moments. I see Robin has been commenting here. He had the left of boom conversation when we first started building this product. It's the idea that instead of looking at what has happened in a SIM and trying to go backwards, how do we start looking at bread crumbs of risk, whether it's individuals or groups, people showing they are trending towards a real issue and being able to intervene there. So that was a big light bulb moment for me.
And then a few weeks ago when we met to prepare for this session, you brought up another one, and I think it is a nice snapshot of the early adopters of human risk. You brought up the idea of static teams and team members and programs versus dynamic team, team members in programs. Can you talk a little bit about that and how you think about that as a leader and a CISO within your department?
Dan Walsh (12:23): Yeah, sure. I mean, I think we would all agree that there's nothing that's truly static. If you look at the molecular level of everything, there's always movement. And so the question then has become, are you living or are you dying? And so when I think about static versus dynamic when it comes to human risk management or training, let's just take it, we just have this boring, static, plain Jane, apologies to people named Jane, program where we're just checking a box and people are grumbling that they have to spend so much time and they wonder why they can't click through the slide fast enough. They have to wait for the slide to play before they can move on and get this thing over with.
And it's that way with human risk. And so for people who are leading security awareness, I think that can be one of the most valuable, it is one of the most valuable roles that an organization can have. And whether you have Jake, or there's a gal on my team, Jessica, who leads it for us, very dynamic individual, she's going to be a future CISO one day if that's what she wants. And it's because of the content, it's because they're moving the ball forward around human risk management.
And so my encouragement to this group today would be just that don't view it as “Well, it's just training,” or “I'm just here to market the program to the internal team at our company.” You're a valuable component of the team. And the one thing I will say just generally about leaders is that being a leader, when I have somebody who's a go-getter, who's very ambitious, who may be ambitious because they want to climb the [inaudible 00:14:10] ladder, may be ambitious just because they want to do a good job, sometimes those things are different. Sometimes they're the same. When you have someone who's high quality like that, they really get the attention of the leader.
And I think that it's vital when we talk about the left of boom, I mean, the tax that human risk is causing on organizations is tremendous. Everyone always hears about KnowBe4 and Solarwinds and Colonial Pipeline and the meat packing plant, and these big things that make national headlines. But when you look at the millions of incidents that happen every day, whether it's just people making mistakes, people not reporting something, somebody trying to shortcut something because technology's not working the right way, somebody trying to take something to their next job, when you add up all those things, the tax that has on organizations is tremendous. And that's why I think it's so important that we as an industry have to get human risk management right.
I think that Unify is going to be the way that it will go ultimately, or solutions like that. And so for me the question comes down to the folks that are these program owners, what kind of leader are you? Because even if you're just a team of one, or maybe you have a team of 10 or whatever, at the end of the day you are leading that function for your organization. And I just think it's super, super valuable. And I think that, again, if you're static, you're dying, and if you're dynamic, you're living and empowering your organization to live.
Mark Collara (15:49): So Dan, when you think about those millions of little things that are taxing on the organization, when you think about your dynamic team and Jessica, how do you envision her and the team chopping away at that? What's the long tail of that? And do you have any tactical examples of what she has done to help the department as a whole?
Dan Walsh (16:16): Yeah, I do. So one of the things that, and I don't mean to, I don't know if she's here today, maybe she is. But I think one of the things that's important is just the communication to the other aspects of the security program. So one thing I'm very passionate about, Mark, is that there should be feedback loops between each of the teams. So GRC should be talking with application security, if you operate software. Application security should be talking about security operations. Security operations should be talking to human risk management. And that should be that exchange of information because each has a dependency on the other. And if you don't believe that it does, then you're probably doing something wrong. And so having those conversations I think is super valuable.
And then going to your leaders and sharing information with them. One of the things that Jessica's done is we have a monthly newsletter that goes out via email. She shares with me the engagement rates on that. I was surprised at how much engagement we actually have.
We just got done with a security awareness month, where we took advantage of some of the content produced by Living Security and we sent out weekly emails. And we split it up between our clinical staff, because we're a primary care company, so folks in the clinics, corporate folks, and then our executive team, and looking at the data across all of that. It is, just as these millions of events on organizations are taxes, the way that we can comprehensively have a well-rounded human risk management or security awareness program, that really helps push that back incrementally.
And I think that it's not just that one communication, that one video, it's really all of it coming together. And that is hard to quantify at times. I will be honest, it is hard to quantify. But people know a good brand and they know good quality when they see it. And so that's why I think it's so important to have that regular communication because it is very qualitative. But when you think about the most iconic brands in our country, they're there because they're qualitative. Apple's a brand. That brand is very qualitative in terms of what the actual value is. But then that's reflected in the stock price and how people think about Apple as a company.
So I would just say, to be concise, Mark, is to communicate amongst the different domains within your program and communicate with your leaders and share that vision, that excitement. Every time I meet with her, I walk away and I'm like wow, thank goodness I have Jessica. Because if I didn't, it'd be like stick figures and it would be very bad. So fortunately I'm not in that position
Mark Collara (19:05): And I think it pivots nicely. And Jake, I want to throw it back to you. One of the things that we hit on a few weeks ago, we know what the tool can do, cross correlating data, looking at risk in a very simple way, and action plans. We see something, we do something, and we're going to see if it works or not. But then we talked about the personal side of it, the champion, the Jakes of the world. And I hit on, I don't think we talk about it enough, what it would mean for that role, whether it's Molly, yourself, or anyone else listening today.
What I've always loved about the revenue side of the business is I've never walked in for a promotion or a raise and worried about the conversation, because I had the numbers to back it up. My team's done X or we've achieved Y since we've been. And I find that's going to be a very empowering value prop to the program owner, to be able to say, October awareness month, I spent a ton of time over the summer planning and promoting and creating. How can we come back in November and say our privileged access users, we've decreased their risk profile by 41%? Like, that to me means something.
So Jake, as you think about this for your own individual brand within WGU and the market, how are you thinking about that? Or did that play into it at all as you were looking at Unify as a potential partner here?
Jake Wilson (20:44): Yeah, it definitely played into it. I mean, I think for the longest time it's always been kind of a one size fits all approach. It's this blanket approach of, so there's some organizations that do compliance training, and we're past that. We roll out quarterly courses, call them essential learning courses and things like that. We'll have lunch-and-learns. We've hosted a bunch of Living Security escape rooms throughout October, which was awesome.
But for the most part, it's always this blanket approach, and it's difficult to establish one-on-one conversations or interacting with specific teams and getting managers or specific teams excited about security. And this definitely will play a role into that. I was thinking about this just this morning. Instead of just a one size fits all approach where just some people don't care, they don't necessarily need what you're providing them. It doesn't necessarily mean they're not going to learn something.
But it's like, I have three kids. If only one of my kids bites their nails and the other two don't, and I'm sitting down all three of them once a month or every single week, saying, "You guys have got to stop biting your nails," the other two kids are going to be like, "Why are you even talking to me, Dad? It's Coco, she's the one that's biting her nails all the time." And they're just going to get bored, and your message is going to get kind of lost and they're just not going to care about security. And those people, they're not necessarily going to help, probably change the organization.
But I think really being able to drill, I'm super excited about this because I know we don't currently drill into job roles and risks or what location or what offices have the most risks tied to them and things like that. And we will for phishing and things like that, but being able to implement Unify and actually look at specific teams and being able to either have conversations or one-on-one training sessions with individuals or teams, or reward teams for their vigilant behavior if they're doing the right things, we haven't been able to do that. So this is kind of a hump that we're finally able to get over and really communicate with our employees. And in the end, I mean, I know it's going to ultimately help shift the direction and the culture of our organization in terms of security.
Mark Collara (23:03): Now, have you started the conversations yet with the department leaders? Because anyone that is on this that came from a different space, or somebody like me that's led departments in the past at other organizations, most of my conversations with security was, "Your team's not taking the training, here's a list, go talk to them." Or they clicked on something. And I've never got the explanation of why that really matters. Tell me why.
And have you started thinking about what the conversations will be like at that department level when you can start kind of benchmarking, but more importantly put it in terms that they understand? Your team is releasing data or deleting data, or taking emails out of quarantine, not using the VPN when your team is traveling, things they understand. Have you started formalizing that yet or socializing to get a feel for how they want that information disseminated to them?
Jake Wilson (24:00): Yeah, I've thought about it. I haven't formalized anything at this point. I've had conversations like that, but it's all more of a reactive thing, like, "Hey, can you reach out to this manager? Can you reach out to this individual, have a conversation about data loss or oversharing," or something like that. And currently what I do, I do one-on-one training sessions with our repeat responders. So I kind of envision something similar to that where you go in and it's just a conversation, it's not a punitive thing. I might let the manager know that, "Hey, I'm going to be setting up a meeting with your employee." And all the employees are great about it. They're not like, "Oh my gosh, why are you attacking me," and things like that. But it all comes with your approach and it depends on the initial email you send to them or the initial Teams chat or whatever.
But I would envision probably something similar to that, where it's like, "Hey, let's just have a conversation. Let me help you. This isn't punitive by any means. I'm not tied in with HR. If HR's going to do something, that's beyond me, I don't worry about any of that kind of stuff. But I just really want to have a conversation with you. I want to see what I can do to help you, provide you with resources at work, at home, et cetera." So I envision something like that, but I haven't actually formalized any particular process.
Mark Collara (25:18): So the other thing that's come up, and Dan, this is more for you at that CISO level, one of the things that our clients that know they need to go in this direction, starting down the path of what integrations to start with, they're really struggling to walk into somebody like your office and say, "I want to go do this thing." So I think it ties back to your dynamic. Is somebody Jessica empowered to do that? And does she have the confidence? So I think that's part of it.
The second piece is how would you coach up somebody? Is it tying it to other main initiatives, whether it's DLP or email securities being talked about on a monthly basis, tying it back to something like that? How would you want to be approached with something innovative like this, and how would you coach people that are listening today to go start that conversation with some confidence?
Dan Walsh (26:15): So I think there's a couple things. I think it always goes back to what is the risk to the business? And I think when you can show that the majority of, and again it's easy to quote like the IBM breach report or the Verizon DBIR or these other industry types of reports. And I think those are valuable, but setting those aside, I think looking at your business, your organization to see, hey, here's the security events that we've had. Here's the security risks that we've had. Here's something that we could consider that would help us catch these things earlier.
Because most of those statistics that you have around incidents are after the security alerts went off, after the security operations team researched, and after you engaged the incident response process. So anything that you can do to say ... And partner with your security operations team, partner with your security analyst and understand root cause analysis on why these things occurred. And when you understand that one of those leading cause is going to be human error or human mistake or something back to the human.
And so I think taking those and saying, "Hey, here's an opportunity that we have, could we have identified them?" And the reality of it is don't say we would've identified all of them because that's just not realistic, but there likely is going to be probably about 80% that you may have been able to identify. And I think just again, engage, show that you're engaged and plugged into the rest of the teams. I think that's really, really huge.
And then I think the other aspect of it is to keep a pulse on where the industry's going, because one of the things that most CISOs do is they always have to look ahead to the next thing because the next thing is what will happen from a risk point of view. And so we also want to look ahead to the next thing in terms of what are the people, processes, and technology that we can put in place to address the next thing. And so I would also view it through that lens.
And then I think the other thing too is understand, admit what you don't know, so clear [inaudible 00:28:15] your assumptions, admit what you don't know. And then the other thing is really understand the effort, and if there's an ROI that you can demonstrate, it goes back to just making the old fashioned business case forward.
Mark Collara (28:28): Yeah, I love it. So I think, so Jake, to that point, we heard Molly talk about if we can intervene, whether that's a technical control, whether that's a policy change, whether it's short form training, long form training, a lunch and learn, the plan would be how do we make a dent in the number of incidents that team is dealing with?
So when you think back six months ago when you went to that room, you don't want to make big statements that you don't know to be true because a lot of it is based on what we see once we turn this on. What were some of the positive impacts that you were expecting to see from this? So when you look back in 12 or 24 months, we say it worked, this is doing what we expected to do. What were some of those things that you had shared when you saw it? I want to try to measure that.
Jake Wilson (29:21): And so I think a great example is, so we use Mimecast for our email security, and we have this Mimecast personal portal where folks go in, they could release emails, block things, things are caught up in quarantine. We created a 25 minute course on how to use this Mimecast personal portal. It was horrible. I wouldn't say it was horrible. I mean, it was very informative, but a lot of people just don't, they just want to check their email. They don't want to have to go to another website and block domains or senders and things like that.
And our email security team kept coming back to me, going, "Jake, so many people are reporting phishing emails, and they're just newsletters or whatever they signed up for. Can you roll out this training again?" It's like, well, we only got a 60% completion rate on it. It wasn't great. And this is a prime example, it's like we don't want to roll out a 20 minute training on how to use the email quarantine system for 7,500 employees. I could go back to this team now, and they ask me almost every single year because they get tired of the emails that are getting reported and stuff. So it's great that I'm going to be able to go back and go, "Guys, we only got like, there's 300 people that are doing the same thing." Or maybe it's more, maybe it's less, but I know 7,500 employees aren't reporting newsletters and things like that, that they signed up for the day before, or whatever, video conference.
But so it's like, I know that'll directly impact that team and they're super excited about it. And that's just one example. But we could tie in so much other stuff that I think I mentioned the other day about SharePoint and like, hey, can we see if somebody downloaded this file from SharePoint or what they're accessing or they're exporting a bunch of files, things like that. It's going to be great to be able to go back and go, "Yeah, here I can look into this for you."
Another conversation I had, which I haven't even really began to wrap my head around it, but it's just a quick off the cuff comment I made to one of the administrators of our learning management system. We have a learning management system outside of Living Security and I talked to her about, "Hey, can we potentially use Living Security for our required training for security and things like that?"
And she started being intrigued and she was like, "Well, we have so many learning management systems. We've got Panopto, we've got Living Security now, we have Bridge." And she's like, "I'm trying to centralize everything. I want to just centralize everything within one learning management system because we don't know what's out there. People are, we have departments using their own LMSs and they're doing required training within their department, and things like that."
And I was like, "Well, you know we also have this new product that I know we could tie in with Bridge. I know it ties in with Living Security. I know it ties in with other LMSs." I go, "We could potentially just tie in all these other LMSs within this one product." And she's like, "Are you kidding me? Really? That would be so amazing." And that was just a conversation like a week or two ago. We haven't even begun to really go down in it.
But I mean, there's all these different departments that would potentially be able to utilize this product, just outside of security. I mean, this is somebody that runs the learning management system for the organization, things like that. And potentially just help her out a ton and decrease the time that she's trying to tie everything in together and look at required training.
Mark Collara (32:43): And hopefully, ideally what you're going to be able to look at is when Mark took that training, did it impact the risk? Are we moving him in the right direction, or is 45 minutes a complete waste of his time, my time, all of it? How do we tie back an outcome to the activity?
So I think with about five minutes left, I want to leave time. Nick, were there any questions that came up from the group? I know these are the big ones that I'm getting pretty consistently as we're talking to the market. Was there anything else that came up that you can think of that you'd want to ask here Nick?
Nick Marchiselli (33:26): Yeah, we've got a couple questions coming in. One actually just came in the chat from Taylor. How do you factor for “correlation does not equal causation” when it comes to training efforts? So why don't we take care of Taylor's question first, and then I've got one or two more.
Mark Collara (33:41): So Jake, you want to handle that one more from a training and awareness perspective?
Jake Wilson (33:47):
Yeah, let me look at this. How do you factor for “correlation does not equal causation” when it comes to training efforts? Let me think about that real quick. I don't know if Dan wants to take that. Let me think about this a little bit more, if you don't mind, for a moment.
Nick Marchiselli (34:05): Yeah, I'll hit you with another one and I'll put this one to Dan for a second. So if we've got a program owner, they're aligned, they know they want to move forward with HRM, what are some potential push backs they might expect to get from a CISO level that they should be prepared for, going into that conversation?
Dan Walsh (34:26): So it's always about the risk versus the spend. So make sure you understand what the numbers are. If you don't talk to your CISO a lot, the first question they're going to ask is how much this costs me? So you have to be crystal clear on that and you need to be crystal clear in terms of the value that you believe that it will drive.
The second thing I would add is if you're just phoning it in right now on everything else, then you may not even get a meeting with the CISO. So you should be driving a dynamic security [inaudible 00:35:02]. Continuous improvement should be your motto, because again, security's tough, security's all about trust, and the CISO has to trust the people that are leading the function of their team. And if you're doing a great job, he or she will trust you, and that will go a long way as well.
And then I think the other thing is come prepared with some, do your homework with the other teams, understand what their concerns might be. On any tool, CISO is going to want to know, and the other teams are going to want to know, how much overhead is there to maintain this? What's the implementation cost in terms of my time and resources? Is this something that the security awareness person's just going to drop on my application security or security analyst or security team? Make sure that you have all those factors considered so you can have that conversation with the CISO.
Mark Collara (35:57): Love it. Jake, anything you want to add there?
Jake Wilson (36:01): Yeah, not necessarily to that. Back to that original question. I think Jenny mentioned in the chat trends and things like that, but I mean, that's the whole focus of human risk management, is just obviously looking at these trends, looking at behaviors, seeing what's changing, what's not.
One of the other things I wanted to mention that I forgot to touch base on earlier, and kind of touched on it as far as being that star within your team, the last thing I think you want to do as a program owner is have somebody else come to you with an idea. And I failed to mention that earlier, and that's part of pitching this or getting the buy-in and things like that. But it would be a bummer if your manager or another team member comes and goes into a meeting and says, "Hey Jake, have you ever thought about doing a product like Unify for human risk management?" Because it's almost like somebody's coming up with the ideas for you.
And just for everybody on this call, you're the subject matter expert, you're the program owner. People are looking to you for ideas. So it's important to kind of, like Dan mentioned, look at the trends, stay ahead of, be aware of what's out there, and as a subject matter expert and the program owner, be coming up with ideas and pitching them to the rest of the team. Don't wait for somebody else to come to you with the idea.
Mark Collara (37:25): Yeah, I think that's a good way to wrap this up. So the way I look at it, the training and awareness function, because of the lack of tooling, has had to rely on engagement and completion and click rates, things that they can tie the reason why they're doing things to a number. So I think we need to really educate on what is now possible, what's the crawl, walk, run approach to it, depending on how you are set up functionally internally, whether it's tech stack or team support or bandwidth and what's going on. But I think that's the challenge to the market now. Who's ready to make a run at the next level, who's ready to be held accountable to, I'm going to run this program and I'm going to come back in six months and show you what I've changed within the organization. I'm going to show what metrics.
And I'm not afraid to walk into Dan's office and say, "Hey, I tried these lunch and learns at these six locations, and it actually didn't work." That's okay too. That's what I look for. And it goes back to Dan's comment. I always want to be viewed as dynamic. It doesn't always have to be successful, but I'm going to push it forward. I'm going to challenge the status quo. And I think that's what a lot of our clients are really excited about now, that we have the tooling that other teams have.
And Dan, you touched on this, how do we put security awareness and training on the same level as the head of the SOC? Because we can quantify it and we can prove the value now. So I think that, to me, is the call to action. The tooling is there now. The energy and effort can be put in the areas that need it and justify it, and then we're going to be able to measure and make decisions off of it from there.
So guys, I really appreciate the time because I don't sit in the seat, I don't have to go make these business cases internally. So I think it's massively valuable to hear from both of you about how you go get it approved, and Dan, what do you look forward to approving something? So guys, I really appreciate it, and yeah, I look forward to continuing these conversations in the future.