

Blogs 
September 11, 2019
The 7 Strategic Security Sins Creating Human Risk

What if you could predict your next security incident before it happens? It’s not about a crystal ball; it’s about data. The vast majority of cyberattacks are not sophisticated zero-day exploits but are the result of common, repeatable human errors. We call these the "security sins," and they represent predictable patterns of behavior that lead to breaches. For too long, security programs have been stuck in a reactive loop of training and phishing tests. A modern approach requires shifting from detection to prediction by correlating signals across human behavior, identity and access, and threat intelligence to identify risk trajectories and intervene proactively.
Where Do Your Biggest Cyber Threats Originate?
7 cybersecurity ‘sins’ are responsible for the majority of your human risk.
Meaning, employees who are unaware of (or intentionally) committing these seven security blunders are significantly more likely to assist or accelerate cyber attack against your company:
- Misinterpret legitimacy
- React impulsively
- Over-rely on security controls
- Disregard policy
- Mishandle devices
- Neglect suspicious activity
- Surrender to security fatigue
The cost of ignoring these ‘sins’ is steep. A successful cyber attack in 2019 is over $5 million USD on average, or around $301 per employee (ponemon). Coupled with the fact that people are now 20x more likely to be robbed at their computers by a cyber criminal than to be held up in the street, the urgency becomes all the more real for people to become situationally aware of current and emerging threats before it's too late.
Traditionally, the reaction by security awareness program owners has been some form of blame-and-train. But better program design means taking responsibility for any resistance and instead choosing to influence culture change through non-punitive action steps. Sustaining culture change requires understanding not just behavior, but also the identity and motivation behind each decision made.
A Quick Refresher: The Original Seven Deadly Sins
Pride, Greed, Wrath, Envy, Lust, Gluttony, and Sloth
The Foundation of Human Error
The concept of the seven deadly sins has served as a framework for understanding human behavior for centuries. While they may seem archaic, these core motivations are still very much alive in the modern workplace and can be directly linked to the human errors that create cybersecurity vulnerabilities. Understanding these foundational drivers is the first step in moving beyond reactive training and toward a predictive model of human risk management. By identifying the "why" behind an action, security teams can better anticipate and prevent incidents before they happen. This deeper understanding comes from correlating signals across employee behavior, identity and access patterns, and incoming threats to see the full picture of risk.
- Pride: This often appears as overconfidence. An employee who believes they are too smart to fall for a phishing scam is the one who clicks without thinking. This hubris leads to an underestimation of threats and an overestimation of personal ability, creating a dangerous blind spot that attackers are quick to exploit.
- Greed: In a corporate setting, greed is the desire to cut corners for a faster result. This can lead employees to use unauthorized applications to share files or ignore security protocols that slow them down. The drive for efficiency, when unchecked, can directly undermine established security controls.
- Wrath: A moment of intense frustration or anger can impair judgment. A disgruntled employee might impulsively click a malicious link, ignore IT guidance out of spite, or handle sensitive data carelessly. These emotionally-driven actions are unpredictable and can have immediate security consequences.
- Envy: Resentment toward a colleague can motivate insider threats. Envy might drive an employee to leak confidential project data to sabotage a peer's success or misuse their access to gain an unfair advantage, turning internal competition into a significant security risk.
- Lust: This isn't just about desire, but an intense craving for something, whether it's information, access, or status. This can manifest as an employee trying to access files and systems beyond their clearance level or falling for a scam that promises exclusive information.
- Gluttony: In cybersecurity, gluttony is the excessive accumulation of data and access privileges. When employees have access to more information than they need to do their jobs, it needlessly expands the potential attack surface, making any eventual breach far more damaging.
- Sloth: This is simple negligence born from apathy or burnout. It’s failing to report a suspicious email, reusing passwords across multiple systems, or putting off a critical software update. Sloth creates vulnerabilities through inaction, making the entire organization an easier target.
The Sins
Misinterpreting email legitimacy
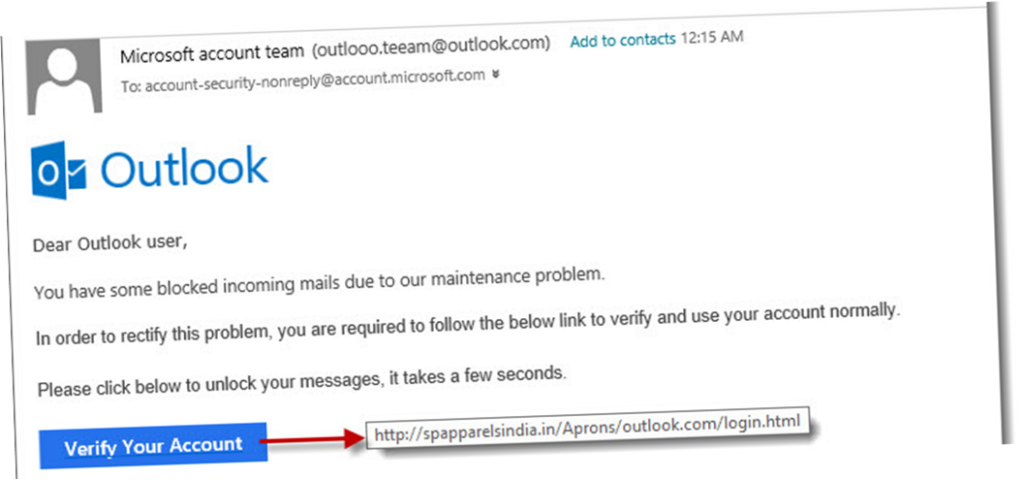
- 91% of cyberattacks begin with a phishing email (TrendMicro)
- 86% of people said they had received more than one suspicious email in the last two weeks, and a majority of them said they would appreciate additional training (Living Security)
- 76% of businesses reported being a victim of a phishing attack in the last year. (Wombat Security)
- 56% of organizations identified targeted phishing attacks as their biggest current cybersecurity threat. (CyberArk)
- 30% of all phishing emails are opened, 12% clicked (Verizon)
Reacting impulsively to suspicious calls

- Being “caught off guard” and “curious” were the two main reasons why respondents fell for social engineering scams, according to a Living Security study. For respondents being “caught off guard,” they did not understand that it was OK to hang up, collect their thoughts, talk to security and call back (if applicable). “Curious” respondents, on the other hand, were unaware of the dangers of inquisitiveness.
Over-reliance on mobile security controls

- Millions of people have over-trusted the native security controls of their phone. The obvious corporate implication is that users will inevitably bring compromised devices into the workplace (barring strict BYOD policies) and connect to WiFi (NetworkWorld). Moreover, the next wave of malicious mobile applications is expected to be even more advanced, with botnet tendencies to actually hijack and control infected devices (VeraCode).
- 73% of people admit to not notifying IT when their device has been infected (webroot)
Disregarding policy guidelines

- Policy questions had the lowest net score on the Living Security platform in 2018, indicating a difficulty identifying appropriate responses to corporate policies and industry regulations.
- 12% of employed respondents were fully aware of the IT security policies and rules set out by their employers (B2B International, Kaspersky Lab)
Mishandling company devices while teleworking or traveling
- 64% of people felt their role made them a moderate to high risk target for cyber criminals, many without an adequate understanding of what security precautions to follow while teleworking or traveling. This attack surface presents a significant risk for accidental loss, theft or tampering of company-furnished devices while away from the workplace. (Living Security)
Neglecting to challenge strangers on premise/ reporting suspicious activity on network

- 90% of all cyber crimes stem from minor oversights (on premise or on network), whether because of gross neglect or stress. (Willis Towers Watson)
Surrendering to password fatigue

- Password-related questions are one of the most misunderstood topics among end users on the Living Security platform, and some indicate the practice of reusing passwords across all their platforms, or merely incrementing/decrementing them to only slightly change the base password (Living Security). Recent reports show that users are also overwhelmed with managing an array of passwords and are looking for “convenience” (Yubico -Ponemon study).
Beyond Individual Actions: Strategic Security Sins
While individual employee actions are a critical piece of the risk puzzle, they don’t tell the whole story. Human risk is often amplified by strategic missteps and flawed security philosophies that originate within security teams and executive leadership. These organizational "sins" create an environment where individual errors are more likely and more damaging. They manifest as poor purchasing decisions, outdated management practices, and a fundamental misunderstanding of security's role in the business. Addressing these high-level issues is essential for building a resilient security culture that moves beyond simply reacting to incidents and starts actively preventing them.
Mistakes in Security Purchasing and Management
The tools and strategies a security team chooses can either build a fortress or a house of cards. Too often, purchasing decisions are driven by factors that have little to do with an organization's actual risk profile. As Phil Venables outlines in his work on Security and The 7 Deadly Sins, these common pitfalls lead to wasted budgets, complex and unmanageable security stacks, and critical gaps in defense. Recognizing these patterns is the first step toward making more intelligent, effective, and data-driven decisions about your security program.
Gluttony: An Excess of Unused Security Tools
Many organizations accumulate security products they don't need or can't fully implement. This leads to a cluttered and inefficient system, with valuable data siloed across dozens of unused or underutilized tools. This "shelfware" not only drains the budget but also creates noise that makes it harder to spot genuine threats. A lean, integrated security stack is far more effective than a bloated one.
Greed: Wanting Top-Tier Features for a Low Price
Some teams get stuck in endless negotiations, trying to acquire premium security features for a bargain-basement price. While fiscal responsibility is important, this approach often backfires. When you squeeze vendors too tightly on price, you often sacrifice the quality of support and partnership needed to make the tool successful, leading to frustration and a poor return on investment.
Sloth: Relying on Outdated Security Methods
The threat landscape evolves constantly, but many security programs do not. Sloth is the tendency to stick with familiar, outdated methods or purchase what's easiest to implement rather than what's most effective. This passive approach means you are always a step behind attackers, relying on yesterday's defenses to fight tomorrow's threats.
Lust: Chasing Unproven Technology Trends
The opposite of sloth, this sin involves jumping on every new, hyped-up technology without proper vetting. Teams get excited about the "next big thing" and hastily abandon current tools for something shiny and new, even if it isn't proven or a good fit for their environment. This creates instability and distracts from core security objectives.
Envy: Buying Tools to Match Competitors, Not Needs
Security purchasing should be based on your organization's specific risks and requirements, not on what a competitor is doing. Buying a tool simply because another company has it, without a clear understanding of how it fits into your strategy, is a recipe for failure. Your security program should be tailored to your unique environment.
Wrath: Treating Security Vendors with Suspicion
Viewing every security vendor as an adversary creates a toxic dynamic. While healthy skepticism is necessary, a default stance of deep suspicion makes it difficult to build the collaborative partnerships required for success. This often leads to poor purchasing decisions and an inability to leverage the full expertise of your chosen partners.
Pride: Believing You Can Build Everything In-House
The "not invented here" syndrome can be particularly damaging. Some teams, especially in large enterprises, believe they can build better security tools than any vendor. This path is often plagued by long delays, soaring costs, and solutions that lack the dedicated support and continuous innovation of a commercial product.
High-Level Leadership and Management Missteps
Effective cybersecurity is not just the responsibility of the security team; it requires buy-in and direction from the very top of the organization. When senior leadership fails to grasp the strategic importance of security, it creates systemic weaknesses that no amount of technology can fix. These management missteps often stem from a dated perspective on what security is and how it contributes to the overall health of the business.
Viewing Security as an IT Problem, Not a Business Imperative
One of the most dangerous missteps is relegating cybersecurity to a siloed IT function. As noted in a ScienceDirect analysis, information security is a core business responsibility. When leaders fail to treat it as such, security is perpetually underfunded, understaffed, and disconnected from strategic business objectives, leaving the entire organization vulnerable.
Underestimating the True Cost of a Breach vs. Prevention
Many leaders balk at the cost of a robust security program while underestimating the catastrophic cost of a breach. With the average successful cyberattack costing over $5 million, the investment in proactive prevention offers a clear and compelling return. Failing to make this calculation puts the company's finances, reputation, and customer trust at severe risk.
Searching for a Single "Silver Bullet" Solution
There is no single tool or technology that can solve all security problems. Leadership often seeks a simple, all-in-one fix, but effective security is a complex, multi-layered program that combines technology, processes, and people. The search for a "silver bullet" is a distraction that prevents the development of a truly comprehensive and resilient security posture.
Building a Proactive Security Program
Avoiding these strategic sins requires a fundamental shift in mindset, from a reactive, compliance-driven approach to a proactive, risk-based one. A modern security program is built on a strong foundation of essential practices but goes further by leveraging data to anticipate and prevent threats before they can cause harm. This means not only strengthening your defenses but also gaining the intelligence needed to understand where your true risks lie and how to address them efficiently. It’s about moving from a state of constant reaction to one of confident prediction and prevention.
Strengthen Foundational Security Practices
Before you can predict and prevent advanced threats, you must master the fundamentals. Foundational security practices are the non-negotiable bedrock of any effective program. These are the core controls and processes that reduce the most common risks and create a baseline of security hygiene across the organization. Neglecting these basics is like building a skyscraper on a foundation of sand; no matter how advanced your other defenses are, the entire structure remains at risk of collapse.
Implement Stronger Password Policies
Passwords remain a primary target for attackers, yet password fatigue is a real problem for employees. Simply enforcing complexity and rotation rules is no longer enough. A modern approach includes promoting the use of password managers, implementing multi-factor authentication (MFA) wherever possible, and educating users on the dangers of reusing credentials across personal and professional accounts. These steps significantly raise the bar for attackers attempting to gain unauthorized access.
Deliver Ongoing, Targeted Employee Training
Annual, one-size-fits-all training is no longer effective. To truly change behavior, you need a security awareness and training program that is continuous, relevant, and tailored to individual risk. This means delivering micro-training and nudges at the moment of need, based on an employee's specific role, access level, and observed behaviors. This targeted approach ensures that training is not just a compliance checkbox but a powerful tool for reducing human risk.
Moving from Detection to Prediction
A truly mature security program doesn't just detect and respond to threats; it predicts and prevents them. This represents the most critical evolution in cybersecurity strategy, shifting from a reactive posture to a proactive one. This shift is powered by data and intelligence, allowing you to see risk trajectories developing and intervene before an incident occurs. It’s about getting ahead of attackers by understanding and mitigating risk at its source: your people and their interactions with technology.
Use Monitoring Tools to Establish a Baseline
You cannot identify abnormal activity if you don’t know what normal looks like. The first step toward a predictive model is to use monitoring tools to gather data and establish a baseline for user behavior, system activity, and network traffic. This baseline provides the context needed to spot deviations that could indicate an emerging threat, moving you from finding known bads to identifying unknown anomalies.
Correlate Data to Prevent Incidents Before They Happen
The key to prediction is connecting disparate data points into a cohesive picture of risk. The Living Security Platform achieves this by correlating data across three critical pillars: human **behavior**, **identity and access**, and **threat** intelligence. By analyzing these signals together, our AI-native engine, Livvy, can predict which users are on a high-risk trajectory and guide your team to act autonomously with targeted interventions. This provides the actionable visibility needed to prevent incidents, not just respond to them after the damage is done.
Thinking about briefing your team on the 7 deadlies? Maybe you want to customize a slide-deck for your end-users? Download the editable slide deck (.pptx) below just by signing up!
Frequently Asked Questions
Are these "security sins" just another way to blame employees for security failures? Not at all. In fact, the goal is the complete opposite. The traditional "blame-and-train" cycle is ineffective because it focuses on the mistake, not the motivation. Understanding these common patterns helps us see security failures as predictable outcomes of human nature, not isolated personal failings. The focus shifts from punishing an individual to improving the system and culture that allowed the error to happen in the first place.
We already have a security awareness program. How is addressing these "sins" different? A traditional awareness program often focuses on checking a compliance box with annual training and phishing tests. Addressing these sins requires a more dynamic approach. It means moving beyond general awareness to manage human risk proactively. This involves using data to understand who is most at risk and why, then delivering targeted, timely interventions that actually change behavior, rather than relying on a one-size-fits-all training module.
How can we realistically predict these behaviors instead of just reacting after someone clicks a bad link? Prediction becomes possible when you stop looking at security events in isolation. A single click is just one data point. A predictive model works by establishing a baseline of normal activity and then correlating signals from different sources to spot a person's risk trajectory changing over time. By analyzing patterns across employee behavior, their identity and access levels, and the specific threats targeting them, you can identify high-risk situations before they lead to an incident.
The article mentions both individual and strategic sins. Which should we focus on first? This is a great question because the two are deeply connected. While individual actions are the final step in a breach, they often happen within a flawed system. We recommend leaders first look inward at the strategic sins. If your security stack is bloated and inefficient (gluttony) or you're relying on outdated methods (sloth), you are creating an environment where individual mistakes are more likely and more damaging. Strengthening your foundational strategy makes managing individual risk much more effective.
What is the most critical data needed to start identifying these risk patterns? To get a complete and accurate picture of risk, you need to correlate data across three core pillars. First is human behavior, which tells you what people are actually doing. Second is identity and access, which shows you the potential impact an individual could have if compromised. Third is threat intelligence, which reveals who is being actively targeted by attackers. Relying on just one of these gives you an incomplete story; true prediction comes from seeing how all three interact.
Key Takeaways
- Identify predictable patterns in human error: Most security incidents are not random; they result from a few common behaviors, or "security sins," like misinterpreting legitimacy or reacting impulsively. Recognizing these patterns is the first step to getting ahead of them.
- Address strategic flaws that enable risk: Individual mistakes are often symptoms of larger organizational issues. Flawed purchasing decisions, outdated security management, and treating security as just an IT problem create an environment where employee errors are more likely to happen.
- Adopt a predictive security model: Move beyond simply reacting to incidents by correlating data across employee behavior, identity and access, and threat intelligence. This provides the insight needed to identify high-risk trajectories and intervene proactively before a breach occurs.
Related Articles
- Cyber Threats 7 Deadly Sins
- Cyber Threats - The 7 Deadly Sins of Security Awareness - a Living Security Intelligence Report
- 7 Human Risk Management and Cybersecurity Terms You Should Know
- People: Criminally Underutilized in the Fight vs. Cybercrime
- Measure Cybersecurity Behavior for Lasting Change | Living Security
