

Blogs 
June 15, 2020
4 Phishing Scams & How to Predict Human Risk

You're here to learn about the latest phishing themes, and we'll get to that. But what if the real threat isn't the bait, but predicting who will bite? Your team completes security training, yet risky clicks still happen. Why? Because you can't see the warning signs. You don't know if the employee searching for cracked software with queries like site:themesx.com themex is your next major security incident. Let's explore five common phishing attacks and, more importantly, how to connect these behaviors to predict and prevent risk.
2020 Top Phishing Scams
We’ve talked about phishing before and if you need a refresher, check out this link.
Today, we’re looking into 5 types of themed phishing scams. We want to tell you which scams are most notorious in 2020 so that you can be ready if you are ever on the receiving end. Here’s some real-life examples and how to avoid them.
- COVID-19 or the novel coronavirus
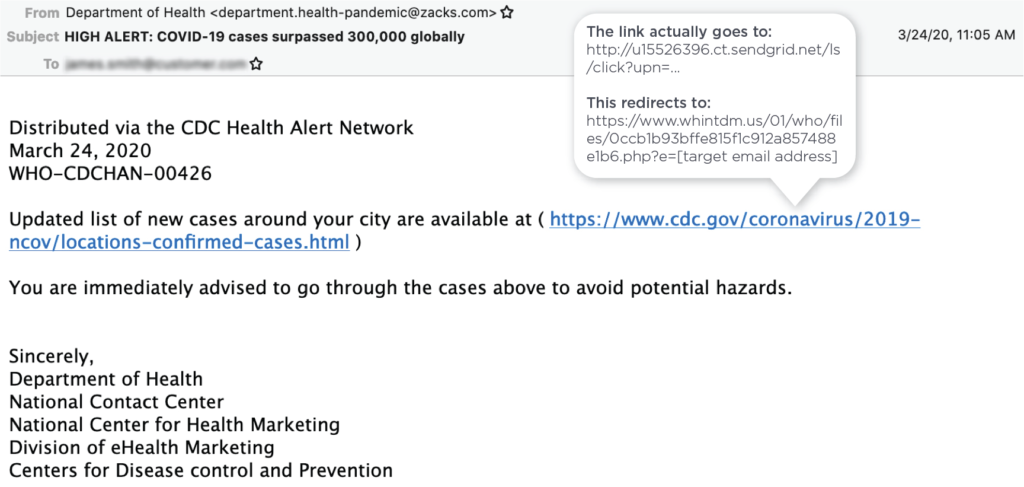
- Example: COVID-19 cases surpassed 300,00 globally
- Unsurprisingly, coronavirus (or COVID-19) is the undisputed winner here. The whole world is worried about the current pandemic, offering cybercriminals an ideal opportunity to exploit our fear and attack us when we are most vulnerable. In a single week in April, Google blocked more than 18 million COVID-19 phishing emails daily. That gives you an idea of the scale of the problem. :/
- Themed Phishing photos
- Donations for fake charities and healthcare organizations
- Example: We need your support! Donate now!
- Donations is a classic example of a popular phishing theme, which gained an extra twist with the COVID-19 pandemic. Cybercriminals are pretending they are charities or companies working to develop vaccines or drugs for the novel coronavirus. They hook you in by explaining how you can do your part by donating in order to fund their studies or charitable work.
- Tests and cure for coronavirus
- Example: New COVID-19 prevention and treatment information! Attachment contains instructions from the U.S. Department of Health on how to get the vaccine for FREE
- In this type of phishing scam you receive an email saying that the test for coronavirus is available for you for free or that there is a new drug that will eliminate coronavirus completely. To get it, you just need to click the link below and provide your personal details…
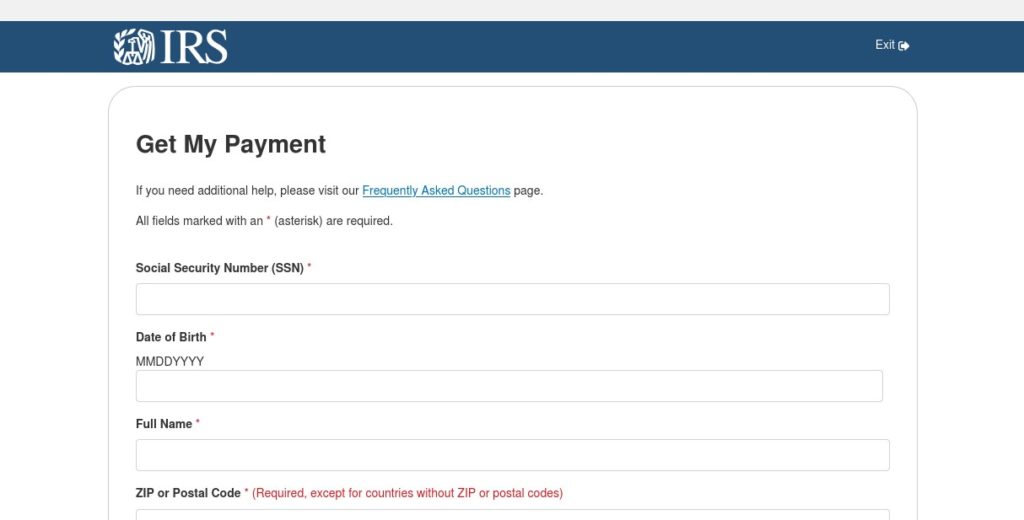
- Economic relief
- Example: IMPORTANT: Details on the government scheme to help businesses affected by the COVID-19 pandemic
- For some, the current lockdown means severe financial problems. Governments in many countries promised to help businesses and entrepreneurs which were negatively affected. To make the most out of this situation, fraudsters and cyber criminals produce emails about available financial support schemes. They look like they are coming from a government agency or a bank and very often contain notorious malware!
- Spoofed IRS Payment Credential Phishing Page via cmattayers[.]com
- Remote work
- Example: Message Detail Internal Communication Alert: Coronavirus (COVID-19) Update
- Working from home is today’s reality. Many companies switched to remote work at the end of March and are still operating this way. Communication between the employees is done by emails, which opens doors to a huge wave of cyber-attacks. Cybercriminals can pose as your employers, sending you updates on the company’s policies. Or they can pretend to be your IT department, emailing you a link to download a new software which allegedly increases the company’s teleworking capabilities.
Spear Phishing
While standard phishing campaigns cast a wide, impersonal net, spear phishing is the opposite. It’s a highly targeted attack where cybercriminals aim for specific individuals or groups within an organization. These attackers do their homework, using information from social media or company websites to craft convincing and personalized emails. According to a 2023 report from Barracuda Networks, while spear phishing has a low volume, it has a disproportionately high impact because the tailored approach makes the messages seem legitimate. This is why traditional security awareness training, which often focuses on generic examples, can fall short. To effectively counter these threats, security teams need to understand risk at an individual level by correlating data across behavior, identity and access, and real-time threats.
Whaling and CEO Fraud
Whaling is a form of spear phishing that sets its sights on the biggest targets in an organization: senior executives. As IBM notes, these attacks are aimed exclusively at high-level employees who have the authority to approve large financial transactions or access confidential company strategy. An attacker might impersonate the CEO, a tactic known as CEO fraud, and email someone in the finance department with an urgent request to wire funds to a new vendor. Because these individuals have elevated access and are often heavily targeted, their risk profile is unique. A proactive defense requires identifying which leaders are most at risk not just based on their behavior, but by analyzing their access privileges and the threat intelligence surrounding them.
Business Email Compromise (BEC)
Business Email Compromise, or BEC, is one of the most insidious and financially damaging attacks. Instead of just spoofing an email address, attackers gain actual control of a legitimate corporate email account. From there, they can send fraudulent invoices to customers, request fraudulent wire transfers, or access sensitive data, all from a trusted source. The problem is widespread; research shows that one in four organizations had at least one email account compromised. Because the malicious requests come from a real account, they bypass many technical security filters, making human vigilance the last line of defense. This underscores the need for a system that can predict and flag anomalous activity by analyzing identity and access signals alongside user behavior.
Smishing and Vishing
Phishing isn’t limited to email anymore. Attackers are increasingly turning to other communication channels to reach their targets. Smishing uses fraudulent SMS text messages, often with urgent links about a package delivery or a compromised bank account. Vishing, or voice phishing, involves phone calls where attackers impersonate a trusted entity like your bank, the IT help desk, or a government agency to trick you into revealing sensitive information. As attackers diversify their methods, organizations must broaden their view of human risk. A comprehensive Human Risk Management strategy should account for these varied threat vectors to build a complete and accurate picture of an individual’s risk profile across all platforms.
The Business Impact of Phishing
When a phishing attack succeeds, the consequences ripple far beyond a single compromised computer or user account. It’s not just an IT issue; it’s a significant business problem with tangible, and often severe, operational, financial, and reputational consequences. A successful attack can halt business operations, trigger regulatory fines, and lead to costly legal battles. The initial breach is often just the starting point for a cascade of negative outcomes that can impact an organization’s bottom line and its standing in the market for years to come. This is why a reactive, "detect and respond" approach is no longer sufficient. Businesses need a proactive security posture that predicts and prevents these incidents before they can cause widespread damage.
Understanding the full scope of the business impact is critical for CISOs and security leaders who need to justify investments in modern security solutions. The conversation is shifting from technical controls to business outcomes. Preventing a single major breach protects revenue, maintains customer trust, and ensures business continuity. By focusing on a predictive model of risk that incorporates signals from user behavior, identity systems, and threat intelligence, organizations can move from simply training employees to actively managing human risk. This approach provides the actionable visibility needed to stop incidents before they happen and demonstrate a clear return on investment by safeguarding the entire enterprise from the cascading effects of a successful phishing attack.
Financial Losses and Data Breaches
The financial toll of a successful phishing attack can be staggering. According to research from IBM, spear phishing accounts for less than 0.1% of all emails but is responsible for an astonishing 66% of all breaches. The report also found that the average cost of a data breach has reached approximately $4.76 million. This figure includes not only the direct financial losses from fraudulent wire transfers but also the extensive costs associated with incident response, forensic investigations, legal fees, and potential regulatory fines. For enterprise organizations, a single, well-executed attack on a high-value target can result in a multi-million dollar event, making the case for proactive prevention incredibly clear.
Reputational Damage
Beyond the immediate financial hit, the long-term damage to an organization's reputation can be even more devastating. A data breach erodes the trust that customers, partners, and investors have placed in a company. As Barracuda Networks highlights, this loss of trust is a significant consequence of a successful attack. Once sensitive customer data is compromised, rebuilding that confidence is a slow and expensive process. The negative press, customer churn, and damage to brand equity can have lasting effects on a company's market position and ability to compete. Protecting your reputation is a core component of a robust security strategy, reinforcing the need to prevent incidents before they can tarnish the brand you’ve worked so hard to build.
How Not to Get Caught?
Phishing emails are becoming much more sophisticated and creative. At the moment, they are the most common tool used by cybercriminals. To help you stay safe online we prepared a list of things you should remember when checking your emails.
- Stay alert and ask yourself questions! If an email contains info that looks unreal or too good to be true, you should not open it. If anything looks suspicious, it’s because it definitely is!
- Verify before you click a link or submit any personal information. If it’s an email from your bank or an organisation you know, call them and ask if they really sent it to you.
- Never download anything you received in an email unless you are 100% sure it’s from a trusted source.
- If you’re interested in the information the email claims to have, google it. Visit verified websites and check there.
- If in doubt, don’t open it! Ask your IT department or simply delete the message.
- Invest in training. Your attention and knowledge are your best defense against phishing attacks. Good training will make you more aware of tactics used by cybercriminals and will help you stay safe.
Security Awareness Training
Your team's attention and knowledge are the best defense against phishing. Effective security awareness training is the foundation of any strong phishing prevention program. The goal is to educate employees about the nature of these threats, how to recognize them, and what to do when they encounter a potential phishing attempt. This training moves security from a purely technical function to a shared organizational responsibility. It equips every individual, from the C-suite to the front lines, with the skills to defend against social engineering and other attacks that target the human element of your security posture.
Good training makes your team more aware of the tactics cybercriminals use. It teaches them to understand the potential dangers of opening attachments from unknown sources or clicking on suspicious links. By building this baseline knowledge, you empower your employees to become an active part of your defense strategy. They learn to question unusual requests, verify information through trusted channels, and report potential threats. This proactive stance is critical for stopping attacks before they can cause significant damage to your organization's data, finances, and reputation.
Realistic Phishing Simulations
Theory is important, but practical application is where real learning happens. Realistic phishing simulations are essential for testing and reinforcing the lessons from security awareness training. These controlled exercises mimic the sophisticated attacks your employees will face, allowing them to practice their detection skills in a safe environment. An effective phishing awareness campaign helps employees recognize suspicious emails and makes them aware of the threat in a tangible way. When an employee interacts with a simulation, it creates a memorable learning moment that is far more impactful than simply reading about threats.
Simulations also provide security teams with invaluable data. They reveal which employees or departments are most vulnerable and which types of phishing lures are most effective against your organization. This information allows you to tailor your training efforts, focusing on the specific areas of weakness you've identified. Instead of a one-size-fits-all approach, you can deliver targeted micro-training to individuals who need it most, making your entire program more efficient and effective at reducing risky behaviors across the workforce.
Analyzing Human Risk to Predict Vulnerabilities
Knowing who clicked on a phishing simulation is just the beginning. To truly get ahead of threats, you need to understand the underlying risks and predict where the next incident is likely to occur. This is the core principle of Human Risk Management (HRM). It involves shifting from a reactive model of detecting and responding to incidents to a proactive one that predicts and prevents them. By analyzing patterns in human behavior and other risk factors, you can identify vulnerabilities before an attacker has a chance to exploit them.
This predictive approach allows security leaders to move beyond simple awareness and start managing human risk with the same data-driven precision as any other area of cybersecurity. It’s about understanding the "why" behind an action, not just the action itself. Is an employee consistently failing simulations because of a knowledge gap, or are they being heavily targeted by external threats? Answering these questions provides the context needed to apply the right intervention at the right time, effectively reducing your organization's overall risk exposure.
Correlating Behavior, Identity, and Threat Data
A single data point, like a simulation click rate, offers a very limited view of your actual risk. True, actionable insight comes from correlating data across multiple dimensions. The most effective programs analyze signals across three core pillars: human behavior, identity and access, and external threats. This comprehensive analysis provides a multi-faceted view of risk that is impossible to see when looking at each data stream in isolation. It helps you understand not just who is acting in a risky way, but who has the access to cause significant damage and who is actively being targeted by adversaries.
For example, an executive with privileged access to sensitive systems who repeatedly engages with phishing simulations and is also the target of a real-world spear-phishing campaign represents a critical risk. The Living Security platform autonomously correlates these signals to surface these high-impact risks. This allows security teams to prioritize their efforts, focusing on the individuals and groups that pose the greatest potential threat to the organization and applying precise, guided interventions to mitigate that specific risk.
Developing a Strong Security Culture
Ultimately, technology and training are tools to support a larger goal: building a strong, resilient security culture. Phishing prevention is not just the responsibility of the security team; it belongs to everyone in the organization. A positive security culture is one where employees feel empowered to act as a line of defense. They are encouraged to be vigilant, to question suspicious communications, and to report potential incidents without any fear of blame. This creates a powerful feedback loop that strengthens your overall security posture from the inside out.
This culture is built through consistent communication, leadership buy-in, and positive reinforcement. It reframes security from a set of restrictive rules into a shared mission to protect the organization and its people. As your program matures, it becomes less about checking a compliance box and more about fostering a collective mindset of security awareness. This cultural shift is a key indicator of a mature Human Risk Management program and is fundamental to achieving long-term, sustainable risk reduction.
Measuring the Effectiveness of Your Phishing Prevention Program
If you can't measure it, you can't manage it. To justify investment and demonstrate progress, security leaders must be able to measure the effectiveness of their phishing prevention efforts. This requires moving beyond vanity metrics and focusing on data that reflects genuine risk reduction. The right metrics provide clear, board-ready insights into how the program is performing and where improvements are needed. They tell a story about how your organization's security posture is strengthening over time, backed by credible data.
Effective measurement starts with establishing a baseline to understand your initial risk level. From there, you can track progress against key indicators that show how employee behavior is changing. According to recent industry analysis, organizations that implement comprehensive programs see significant improvements in their resilience to social engineering attacks. The key is to choose metrics that align with your business objectives and provide a clear picture of your return on investment, turning security from a cost center into a strategic business enabler.
Key Performance Indicators (KPIs)
Several key performance indicators (KPIs) can help you track the health of your phishing prevention program. Training completion rates are a foundational metric, showing whether employees are engaging with the educational content you provide. Phishing simulation click rates measure susceptibility, while report rates are an even more valuable indicator. A high report rate demonstrates that employees are not only spotting suspicious emails but are also actively participating in the defense process by alerting the security team. This is a strong sign of a healthy and engaged security culture.
Tracking these KPIs over time allows you to identify trends and measure the impact of your interventions. For instance, you might see click rates decrease while report rates increase after a targeted training campaign. As recognized by leading analysts in reports like the Forrester Wave™, top-tier programs use these metrics to continuously refine their strategy. They provide the data needed to prove the program's value and make informed decisions about where to allocate resources for maximum impact on risk reduction.
Moving Beyond Click Rates
While click rates are a useful starting point, they are not the ultimate measure of success. A low click rate doesn't always equal low risk. It only tells you what happened in a specific simulation, not what could happen in a real-world attack or why it happened. To truly understand your risk posture, you must look deeper. The most advanced programs move beyond this single metric to measure the actual reduction in human risk, which requires a more sophisticated, data-driven approach that considers a much broader context.
This means measuring changes in risk trajectories by correlating behavior with identity and threat data. The goal is to gain predictive intelligence that shows which employees are becoming less risky over time and which still require intervention. By focusing on risk reduction as the primary KPI, you can demonstrate a direct impact on the organization's security. This approach provides a far more accurate and meaningful picture of your program's effectiveness, showing how your efforts are preventing incidents, not just reducing clicks on simulated emails.
Frequently Asked Questions
My team already does phishing simulations. Isn't that enough to prevent attacks? Phishing simulations are a great starting point, but they only show you one piece of the puzzle: who clicked on a fake email at a specific moment. A true prevention strategy goes deeper to understand the context behind that click. It connects simulation performance with other critical data, like an employee's access level and whether they are being actively targeted by real-world threats, to predict where your next real incident is most likely to happen.
You mention correlating data to predict risk. What kind of data are you talking about? Effective prediction relies on analyzing data across three core areas. First is behavior, which includes things like security training performance and simulation results. Second is identity and access, which tells you who has privileged access to sensitive systems. The third is threat intelligence, which shows who is being targeted by actual adversaries. By combining these signals, you get a complete and actionable view of risk that a single data source could never provide.
How does this predictive approach help against targeted attacks like CEO fraud or Business Email Compromise (BEC)? These attacks work because they are aimed at specific, high-value individuals. A predictive model identifies who is most vulnerable to these attacks before they even happen. It does this by recognizing the dangerous combination of factors: an executive with high-level permissions who is also being targeted by external threats and perhaps shows a pattern of risky behavior. This allows you to apply protective measures for that person specifically, rather than waiting for a fraudulent wire transfer request to appear.
What is the first step to move from basic awareness training to a more predictive risk management model? The best first step is to understand where your program currently stands. A Human Risk Management maturity model can help you assess your current practices, from foundational training to a fully predictive and data-driven program. This assessment gives you a clear baseline and a roadmap for integrating more sophisticated data analysis and proactive interventions into your security strategy.
How does AI fit into predicting human risk without being just another tool to manage? Think of AI as the engine that makes sense of all the complex data. An AI-native platform can analyze billions of signals across behavior, identity, and threat intelligence far more effectively than a human team ever could. It connects the dots to predict risk, provides clear recommendations on how to act, and can even execute routine tasks like sending micro-trainings autonomously, all while keeping your team in full control with human oversight.
Key Takeaways
- Go beyond awareness to prediction: A modern defense strategy moves past simply identifying phishing types and instead predicts which users are most vulnerable, allowing you to prevent incidents before they happen.
- Gain a complete view of risk by correlating data: Relying only on click rates is insufficient; to accurately prioritize threats, you must analyze signals across user behavior, identity and access, and external threat intelligence.
- Measure what matters by focusing on risk reduction: Move past simple click rates and track KPIs that show genuine progress, like increased report rates. This approach demonstrates a clear reduction in your organization's risk and proves the value of your program.
