

Blogs 
May 19, 2020
Verizon DBIR 2020: What It Means for Human Risk

The annual Verizon Data Breach Investigations Report (DBIR) is here. It's the one report security leaders clear their calendars for. CISOs and SOC analysts dissect every chart, searching for an edge against attackers. The Verizon DBIR 2020 confirms a critical truth: adversaries are methodical, financially driven, and exploit people over systems. Instead of just reacting to these findings, we can use the insights from the 2020 DBIR to anticipate threats and act first. Let's break down the key figures and build a proactive defense.
I know what you came here for, so I'll give you what you want: there are some RICH insights here for security awareness. And no, I don't want to just treat you to a special edition of awareness-flavored confirmation bias. I want us both to have a pinky's-up, 5-course meal in security awareness, where we don't just chew the meat and spit out the bone. Get your bibs out, team, and prepare to feast...
What Does the Verizon DBIR 2020 Reveal?
- Security "awareness" was called out 14 times.
- 12 of those 14 call-outs were recommending that organizations "implement a security awareness and training program," like... yesterday. (RE:Center for Internet Security's CSC #17).
- Security "awareness" was listed as a top control for 80% of industries listed. Meaning, the vast majority of all industries got an explicit call-out in a TOP-FOUR recommendation for security awareness. The only industries that didn't get an explicit call-out were Accommodation & Food services, Construction & Retail...
- 67% of breaches were caused by credential theft, errors and social attacks... a.k.a. facilitated by the human. We all know how to read between the lines, here, and it requires commitment and consistency to train the human operating system. As we'll see soon, there are some good things happening that are directly related to security awareness efforts.
Faster Detection, Slower Response
Let's celebrate a win from the report. The time it takes to find a breach has improved dramatically. Where 56% of breaches once took months to find, the 2020 report shows that 81% were found in days or less. This is a huge step forward, showing that investments in detection technologies are paying off. Our digital alarm systems are getting more sensitive and effective, which is exactly what security teams have been working toward. It’s a clear signal that we are getting better at identifying when something is wrong within our environments, and we should absolutely acknowledge that progress.
But here’s the catch. While our alarms are getting louder and faster, we’re still slow to get to the fire. The data also reveals that only 10% of organizations can investigate a cyber intrusion within the target time of ten minutes. This gap between detection and response is where risk thrives. It’s the window of opportunity for threats like ransomware to take hold. This forces us to ask a different question. Instead of just trying to react faster, how can we get ahead of the incident entirely? True human risk management involves moving from a reactive posture to a predictive one, using correlated data across behavior, identity, and threats to anticipate and prevent incidents before they happen.
Proven Tactics to Prevent Data Breaches
- Phish click rates are "as low as they ever have been" (3.4%), and phish reporting rates are "rising, albeit slowly." This is HUGE, team. Phish reporting numbers are now hovering around ~40%, up from 20% in 2016. That is AMAZING and all thanks to YOU.
- Misuse ("intentional actions undertaken by internal employees that result in some form of security incident") is trending down as a percentage of incidents. (*Verizon notes that could be attributed to lower granularity data this year and may rise back to previous levels in 2021. On the other hand, breaches are showing a legitimate drop, which appears to be associated with less misuse of databases to access and compromise data).
- "No relationship" between credential leaks and credential stuffing, the week following a breach. Apparently, cyber criminals merely gobble up the new breaches whenever they update their credential stuffing dictionaries.
Surprising Statistics from the 2020 DBIR
- 86% of breaches in 2019 were financially motivated... Cyber criminality, it seems, is not just for the 'lulz'
- 30% of breaches involved internal actors (almost 1 in every 3 breaches)... while, 70% involved outsiders (* as you might expect, because there are more people outside than inside an organization). Still, with some estimates that only 1 in 10 insiders get caught, there may be a significant 'dark number' here that is not yet reported. Obviously, the DBIR is a trailing indicator and cannot account for things yet unreported, so take it with a grain of salt.
- ~60% of breaches were perpetrated by organized crime groups (the rest a smattering of nation-state, end users and sys admins). This is a big revelation for some, because sometimes attribution is a proxy for risk. Meaning if you know WHO you're dealing with, you often know HOW to fight back against their known capabilities.
- >80% of breaches (within "hacking" incidents) involve Brute force or the Use of lost or stolen credentials. Again, this has a mega human factor, in that people are on the hook to protect their credentials and report suspected compromise. The good news is that people can be trained!
A Sharp Rise in Breach Volume
The report makes one thing clear: cybercrime is a business. A staggering 86% of breaches are financially motivated, meaning attackers are strategic and focused on their return on investment. This isn't about random acts of digital chaos; it's a calculated effort to exploit vulnerabilities for profit. This financial incentive is precisely why social engineering and credential theft remain top attack vectors. They are low-cost, high-reward tactics that prey on human behavior. For security leaders, this reinforces the need to move beyond reactive measures. Instead of just responding to incidents, the goal is to predict and prevent them by understanding the human risk factors that attackers are so adept at exploiting. A proactive Human Risk Management strategy is essential to disrupt the business model of cybercriminals.
The Challenge of Network Complexity
As organizations grow, so does their digital footprint and complexity. The report finds that half of all companies use seven or more networks, creating significant security challenges and blind spots where mistakes can go unnoticed. This environment magnifies the impact of human error, proving that technology alone isn't enough to secure a complicated network. To truly reduce risk, you need visibility that connects the dots between your technology, your data, and your people. By correlating signals across user behavior, identity and access, and known threats, you can identify where your most critical risks lie and take targeted action before a simple mistake becomes a costly breach.
What Are the Primary Causes of Data Breaches?
- Phishing remains top threat "action" among threat actors. A good reminder to reinforce our phish education programs and keep up the friendly phishing through 2020!
- Threat actors went after email addresses, credentials and changed user behavior in that order. Verizon considers these the "top compromised attributes" across industries. If we're doing defense-in-depth, lets start with these prized assets and work our way outward!
- Human exploit attempts (known as "social actions" in DBIR) arrived via email 96% of the time, while 3% arrived through a website. A little over 1% were associated with Phone or SMS, which is lower than expected. A good reminder to not pivot too hard to smishing topics, but hang on to tried-and-true phishing education.
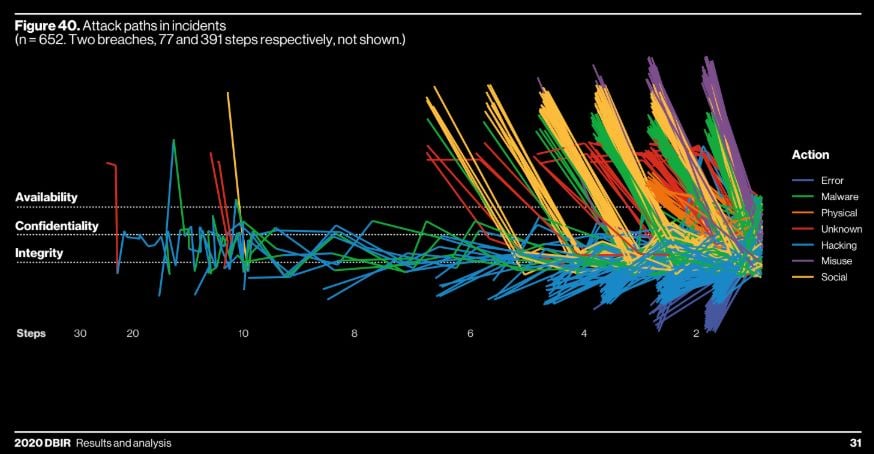
- Attackers prefer "short paths and rarely attempt long paths." Below, Figure 40 is basically just a pretty illustration of the trend of cyber criminals finding the quickest and easiest route to their victims. Read it left-to-right, and see how few attack journeys start at left. This means threat actors are LAZY and that they STILL take the path of least resistance. Don't give them more low-hanging fruit!! Add an obstacle. If there ever was a case for 2FA...
Web Applications as a Top Attack Vector
The report highlights a significant shift in the threat landscape: web applications are now the number one source of cloud breaches, responsible for over 40% of incidents. This tells us that attackers are increasingly targeting the platforms where we work and collaborate every day. While it’s easy to think of this as a purely technical problem, the human element is central. Misconfigurations, weak or reused credentials, and a lack of awareness about secure application use create the perfect entry points for threat actors. To get ahead of this, security teams need a clearer picture of risk that connects user behavior with their access to these critical applications. A proactive Human Risk Management strategy can predict which users pose the greatest threat based on a combination of their behaviors, their identity and access privileges, and the threats targeting them.
The Continued Threat of Ransomware
Ransomware continues to be a major disruptor, and the DBIR shows it hits the public sector especially hard. A staggering 60% of malware attacks against public organizations involved ransomware, a figure more than double the average across all other industries. This isn't just bad luck; it's a targeted strategy that preys on human vulnerability. The initial access for a ransomware attack often comes from a social engineering tactic, like a phishing email that tricks an employee into giving up credentials or running malicious code. Instead of waiting for the inevitable incident report, security leaders can shift their focus to prevention. By analyzing signals across your workforce, you can identify the individuals most likely to engage in risky behavior and intervene with targeted training or policy adjustments before an attack is successful.
Unpatched Systems and Misconfigurations
Technical vulnerabilities remain a classic and effective entry point for attackers. The report reminds us that many ransomware attacks succeed simply because of unpatched software. This is often less of a technology problem and more of a human process failure. The challenge is compounded by the fact that only 10% of organizations can effectively investigate an intrusion within ten minutes, leaving them constantly on the back foot. A truly proactive security posture means understanding risk in context. An unpatched system is a problem, but an unpatched system managed by a user with a history of risky behavior and privileged access is a critical threat. The Living Security platform helps you connect these dots, correlating data across behavior, identity, and threat to predict where your most significant risks lie and guide you to prevent incidents before they happen.
Key Findings by Industry
Public Sector Under Siege by Ransomware
The public sector is facing a significant challenge from ransomware. It's not just another threat; it's the dominant one. A staggering 60% of malware attacks on public organizations are ransomware, making it clear where attackers are focusing their efforts. These groups, often organized crime syndicates, know that disrupting public services creates immense pressure to pay. The report also highlights that 70% of these breaches are caused by external attackers, frequently exploiting web applications to gain initial access. This underscores the importance of not only securing technical perimeters but also addressing the human element that attackers so often exploit to get their foot in the door. Proactively identifying and mitigating human risk is critical to breaking the ransomware attack chain before it even begins.
Most Targeted Industries
While the public sector is a prime target, ransomware’s reach extends across all industries. It stands as the third most common type of malware leading to data breaches, a clear indicator of its effectiveness and profitability for cybercriminals. The data shows that organized crime groups are behind approximately 60% of breaches, operating with a level of sophistication that requires a more advanced defense. These groups are methodical, using social engineering and credential theft to exploit employees. This is where a modern approach to security becomes essential. Instead of relying solely on reactive training, organizations can predict and prevent these incidents by correlating data across employee behavior, identity and access, and known threats. This provides the intelligence needed to act before a targeted employee clicks a link and an incident unfolds.
Where Are Defenses Failing?
- The only action type that is consistently increasing year- to-year in frequency is Error. People make mistakes, but this is one to watch out for! (*"The fact that we now see Error becoming more apparent in other industries could mean we are getting better at admitting our mistakes rather than trying to simply sweep them under the rug.")
- Financially motivated social engineering (FMSE) is on the rise. In Appendix C of the DBIR, two members of the US Secret Service, Michael D'Ambrosio (assistant director) and Jonah Force Hill (Sr. cyber policy advisor) take a stab at analyzing the overwhelming number of hacking incidents that are financially motivated, and end with a plea to "work together" to protect and defend networks and create choke-points for criminals to be caught, arrested and prosecuted. (*In 2019, the Secret Service prevented $7.1 billion of cybercrime losses and returned over $31 million in stolen assets to victims of fraud.")
Mmm. I needed that. High-calorie feast on security awareness facts that gives us sustenance for the task ahead: move the needle on behavior change, culture change and helping organizations win!
Implement a Robust Patch Management Program
The DBIR consistently highlights that attackers love the path of least resistance, and unpatched software is a wide-open door. As the report notes, “Many ransomware attacks happen because of unpatched software.” This isn’t a new revelation, but it’s a persistent one. A robust patch management program is non-negotiable. It’s about more than just pushing updates; it’s a systematic process of identifying, testing, and deploying patches to all systems and applications across your organization. This closes known vulnerabilities before threat actors can exploit them, effectively removing the low-hanging fruit that attackers rely on. Think of it as fundamental digital hygiene that hardens your defenses against a huge swath of common attacks.
Maintain and Test Offsite Backups
When a ransomware attack succeeds, your recovery plan is your last line of defense. The DBIR is clear on this point, stating that regularly backing up important files and storing them separately “is the most effective way to recover from a ransomware attack.” The key words here are “separately” and, just as importantly, “tested.” An untested backup is just a hope. Your backups must be stored offsite or in a segmented cloud environment so they aren’t encrypted along with your primary systems. Regularly testing your restore process ensures that when you need your data back, you can actually get it. This simple discipline can be the difference between a manageable incident and a catastrophic business disruption.
Leverage Intrusion Detection Systems (IDS)
While prevention is the goal, rapid detection is critical for minimizing the impact of an attack that gets through. An Intrusion Detection System acts as a vigilant watchdog for your network. As the DBIR points out, “An IDS helps find malicious activity quickly so you can respond fast.” These systems monitor network traffic for suspicious patterns and known threat signatures, alerting your security team to potential incidents in near real-time. This early warning allows your SOC and IR teams to investigate and contain a threat before it can escalate, spread laterally, or lead to a major data breach. It’s a foundational tool for moving from a purely reactive posture to one of active defense.
Shift to Proactive Human Risk Management
The DBIR confirms a truth we all know: the human element is central to enterprise risk. With 67% of breaches caused by credential theft, errors, and social attacks, it’s clear that focusing only on technology is a losing battle. Phishing remains the top threat action, proving that reactive training alone isn’t enough to change behavior. It’s time to shift from awareness to action. A proactive Human Risk Management strategy moves beyond simple compliance. By correlating data across human behavior, identity and access, and real-time threat intelligence, you can predict where your next incident is likely to come from. This allows you to prevent breaches by applying targeted interventions to your riskiest individuals and AI agents before they make a costly mistake.
Frequently Asked Questions
This report is from 2020. Are these findings still relevant? Absolutely. While specific tools and malware strains evolve, the core principles of cybercrime highlighted in the report are timeless. Attackers are still financially motivated and they still target people as the path of least resistance. The trends identified, like the rise of social engineering and the exploitation of human error, have only accelerated. Think of this report not as a snapshot in time, but as a foundational analysis of attacker strategy that makes the case for a proactive security posture even stronger today.
Phishing click rates are down. Does this mean our security awareness training is enough? Lower click rates are a fantastic achievement and show that awareness efforts are having a positive effect. However, it doesn't mean the problem is solved. Attackers are strategic; they only need one person to click to succeed. The real question is not just if people click, but who is clicking and what access they have. Human Risk Management goes a step further by identifying individuals who are not only susceptible but also have privileged access or are being actively targeted, allowing you to focus interventions where they will have the greatest impact.
The report highlights a gap between fast detection and slow response. How does Human Risk Management help? Traditional security focuses on shortening the time between an alarm and the response. Human Risk Management changes the goal entirely. Instead of just reacting faster, the aim is to prevent the alarm from ever going off. By correlating data across user behavior, identity, and known threats, an HRM platform can predict where an incident is likely to occur. This allows you to act first with a targeted nudge or policy adjustment, preventing the breach before a response is ever needed.
How does a focus on human risk fit with technical controls like patch management and intrusion detection systems? Technical controls and Human Risk Management are two sides of the same coin; they make each other more effective. An intrusion detection system can tell you about a suspicious event, and a vulnerability scanner can identify an unpatched server. HRM provides the critical context. It helps you understand the human and AI agent risk associated with those technical alerts. This allows you to prioritize, for instance, an unpatched system managed by a user with a history of risky behavior, turning a long list of alerts into a clear, actionable security plan.
What is the main difference between traditional security awareness and Human Risk Management? Security awareness is primarily about education. Its goal is to inform employees about threats, and success is often measured by training completion or quiz scores. Human Risk Management is a data-driven security strategy. It moves beyond education to measure, predict, and mitigate risk. It quantifies the specific threats posed by individuals and AI agents and uses that intelligence to drive targeted actions that demonstrably reduce the likelihood of a breach.
Key Takeaways
- Prioritize Human Risk as a Business Imperative: Attackers target people with social engineering and credential theft because it's efficient and profitable, causing 67% of breaches. Your security strategy must evolve beyond basic awareness to actively manage the risk your people and AI agents introduce.
- Shift from Reactive Detection to Proactive Prevention: The growing gap between fast breach detection and slow incident response is a major vulnerability. A modern defense uses correlated data across behavior, identity, and threats to predict where your next incident will likely occur and prevent it from happening.
- Disrupt the Attacker's Playbook with Security Fundamentals: Since 86% of breaches are financially motivated, attackers consistently exploit the path of least resistance. Mastering security hygiene, such as disciplined patch management and maintaining tested backups, removes the low-hanging fruit they depend on.
