

Blogs 
May 16, 2025
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
4 Steps to Proactive AI Security Awareness
Attackers are using AI to supercharge social engineering. They can mimic your CEO's voice, replicate a trusted colleague's writing style, and create phishing campaigns at a scale we've never seen before. Relying on employees to spot these fakes with last year's training is no longer a fair fight. The old rules of awareness simply don't apply. To defend against AI-driven threats, you need a new strategy grounded in predictive intelligence. A modern ai security awareness program moves beyond simple detection. It's about understanding who is most likely to be targeted and why, then intervening before an attack ever succeeds.
Turn Security Awareness into Action: Your 4-Step Guide
Evolve Cybersecurity Awareness Month into a Risk-Reduction Movement
Why 'Awareness' Isn't Enough Anymore
For 21 years, Cybersecurity Awareness Month has been a moment for IT and Security teams to rally their organizations. But the threats have changed. The stakes are higher. And expectations? They've evolved.
We can’t afford to settle for a month of games and posters. It’s time to lead with purpose, backed by data and driven by outcomes.
This isn’t just a guide. It’s a call to action for awareness teams to evolve from engagement-centric to risk-driven—where behavior change and measurable impact take center stage.
The High Cost of Passive Security Awareness
Yes, we’ve made cybersecurity more engaging. We’ve brought it into the spotlight. But after two decades of themed months and poster contests, it’s time to ask:
- What happens if we skip Cybersecurity Awareness Month this October?
- How does this align with our biggest risks?
- Can we prove impact beyond participation stats?
- Are we using our existing tools to support October’s goals?
- What’s the ROI—without vanity metrics?
If you can't confidently answer those questions, it's time to evolve.
Understanding the New Wave of AI-Driven Threats
The security landscape is fundamentally changing, and the old awareness playbook is becoming obsolete. Attackers are now using AI to create threats that are more personalized, convincing, and scalable than ever before. These are not just minor upgrades to old tactics; they represent a new class of risk that targets the most complex part of your defense: your people. Traditional annual training and basic phishing tests are no longer sufficient to prepare your workforce for these sophisticated, AI-driven attacks. To get ahead, security teams must shift from a reactive posture to a predictive one, understanding where and how these new threats will emerge.
AI-Generated Social Engineering Attacks
AI has supercharged social engineering, making it nearly impossible to distinguish real from fake. Attackers can now generate phishing emails that perfectly mimic a trusted colleague's writing style or create deepfake voice calls that sound exactly like your CEO requesting an urgent wire transfer. These attacks bypass technical controls and exploit human trust with terrifying precision. Relying on employees to spot these fakes is an unfair fight. A more effective strategy involves understanding the underlying risk factors. By correlating data across employee behavior, identity and access, and real-world threats, you can predict who is most likely to be targeted and intervene before an attack succeeds, moving beyond simple phishing awareness to proactive risk reduction.
Risks from Unsanctioned and Public AI Tools
The threat is not just external. Your own employees, in an effort to be more productive, may be unintentionally exposing sensitive information to public AI tools. A developer might paste proprietary code into a generative AI platform to find a bug, or a marketing team could upload a confidential customer list to brainstorm campaign ideas. This behavior creates a significant risk of data leakage and intellectual property loss. Blocking access to these tools is often impractical. A better approach is to gain visibility into these actions and understand the context behind them. This is a core challenge of modern Human Risk Management: identifying and mitigating risky behaviors before they lead to a security incident.
A Modern Approach to AI Security Awareness
We’re not ditching the classics—webinars, games, fireside chats—they stay. But now, they’re aligned to outcomes, aimed at high-risk cohorts, and backed by data.
Follow these 4 steps to drive more strategic outcomes from Cybersecurity Awareness Month this year.
Step 1: Align Your Strategy with Business Outcomes
Slow down. Don’t start with calendars and themes. Start with intent. Ask your CISO:
“If we could only drive two meaningful behavior changes this Cybersecurity Awareness Month, what should they be—and why?”
From there, engage Incident Response. Find out what’s driving recurring incidents and use that insight to focus your campaign on the most problematic areas.
Establish Clear AI Usage Policies
Your employees are already using generative AI. The key isn't to restrict access but to provide clear guardrails for safe and productive use. Without guidance, your team might unknowingly expose sensitive information, from customer data to proprietary code, by inputting it into public AI models. This creates a significant risk of data exfiltration and intellectual property loss. The first step is to create and communicate a formal policy that outlines which AI tools are approved for use and, more importantly, what types of data are strictly prohibited from being used with them. This policy should be easy to understand and accessible to everyone in the organization, setting a clear baseline for responsible AI interaction.
Cultivate a Proactive Reporting Culture
Your people are your most valuable line of defense against sophisticated AI-driven attacks. To make them effective, you must build a culture where reporting suspicious activity is encouraged and free from blame. Employees should feel comfortable flagging a potential AI-generated phishing email or a deepfake voice call immediately, knowing that their vigilance is valued. Swift reporting is critical; it can be the difference between a contained event and a widespread breach. By making the reporting process simple and reinforcing that it’s a shared responsibility, you empower your entire workforce to act as an extension of your security team, helping to manage human risk proactively.
Instill Verification as a Core Habit
The days of spotting a phishing attempt by its typos are over. AI-generated attacks are nearly flawless, making verification an essential security habit. Teach your employees to adopt a "trust but verify" mindset for any unusual or high-stakes request, especially those involving financial transactions or credential access. This means using an out-of-band method, like a phone call or a direct message on a separate platform, to confirm the request's legitimacy. This principle also applies to using AI-generated information for work. Always have a human review AI outputs for accuracy and bias before they are used in decision-making, ensuring that AI serves as a tool, not an unchecked authority.
Step 2: Measure What Matters
You already have the data. Now it’s time to use it to answer these critical questions:
- Email Security → Who’s being targeted most often?
- Phishing Simulators → Who’s clicking, reporting, or ignoring?
- IAM → Who has dangerous access or poor credential hygiene?
- Org Metadata → Which roles, departments, and regions show patterns of risky behavior?
Living Security’s Unify platform applies AI-powered analytics to surface the answers to these questions. It identifies the riskiest behaviors in real-time—transforming fragmented data from phishing tools, IAM systems and email security into precise, actionable intelligence. This means you can move faster, target smarter and drive measurable outcomes without the manual effort or guesswork.

And with Living Security’s Human Intelligence Team (HInT), you don’t have to dig through the noise. It automatically identifies your riskiest users and gives you precise recommendations: who to target, what to deliver, and how to measure change.
Move Beyond Click Rates with Behavior-Based Metrics
Phishing click rates are a flawed metric for a simple reason: they only tell you what happened, not why. A truly effective program must measure changes in behavior, not just a single action. Instead of focusing on who clicked, start tracking metrics that reflect proactive security habits. This includes measuring how quickly employees report suspicious messages and how they perform in realistic simulations against sophisticated threats like AI-generated phishing. These are the indicators of a resilient security culture, showing a shift from passive awareness to active defense.
This is where a Human Risk Management platform provides critical intelligence. By correlating phishing data with other key signals, you get a complete picture of risk. The Living Security platform analyzes data across three core pillars: user behavior, like reporting habits; identity and access, such as who has privileged credentials; and real-world threat intelligence, like who is being targeted by active campaigns. This allows you to see not just who clicked, but which individuals represent the most significant potential impact, enabling you to focus your efforts where they matter most.
Track Prevented Incidents and ROI
The ultimate goal of any security initiative is to stop breaches. The most powerful way to demonstrate value is to move beyond participation stats and start tracking prevented incidents. When an employee correctly identifies and reports a real malicious email, that is a measurable win. By quantifying how many actual attacks were stopped by your team and calculating the potential cost of those averted incidents, you can build a powerful business case and demonstrate clear ROI. This transforms the conversation from a cost center to a value-driver for the business.
While tracking reported incidents is a powerful reactive measure, a proactive strategy prevents them entirely. The Living Security platform is designed to predict and prevent incidents before they happen. Our AI-native engine analyzes over 200 real-world signals to identify risk trajectories and predict which users are most likely to cause an incident. This allows you to intervene with targeted micro-training or policy nudges, effectively neutralizing the threat. This shifts the ROI calculation from what was stopped to what was prevented from ever becoming a danger, providing CISOs with the forward-looking, board-ready metrics needed to lead with confidence.
Step 3: Pinpoint Risky Behaviors and Users
Forget org-wide metrics. Zero in on what actually matters and set baselines so you can measure progress. Look at the data to determine:
- Who’s clicking and holds privileged access?
- Who’s a repeat clicker and hasn’t enabled MFA?
Then pinpoint risk-heavy departments:
- Which two business units show the most signs of social engineering or insider threat vulnerability?
With Unify and HInT, you can instantly slice and dice this data, identify behavior clusters, and deploy targeted, behavior-driven content experiences that resonate—and work.
Step 4: Gamify Training to Encourage Secure Habits
You’re not running a campaign—you’re launching a cultural movement. And movements need momentum.
With Living Security’s complete toolkit, you’ll have everything ready:
- Leaderboards based on actual behavior improvement
- Prizes tied to security-positive actions: reporting phish, enabling MFA, rotating passwords
- Ready-to-launch content, promo emails, speakers, and live events
- Engagement assets already mapped to risk-informed goals
Unify makes it easy to track progress in real time—with dashboards that show vigilance rising and risk declining across teams. Let departments compete to be the most secure, and let the data declare the winner.

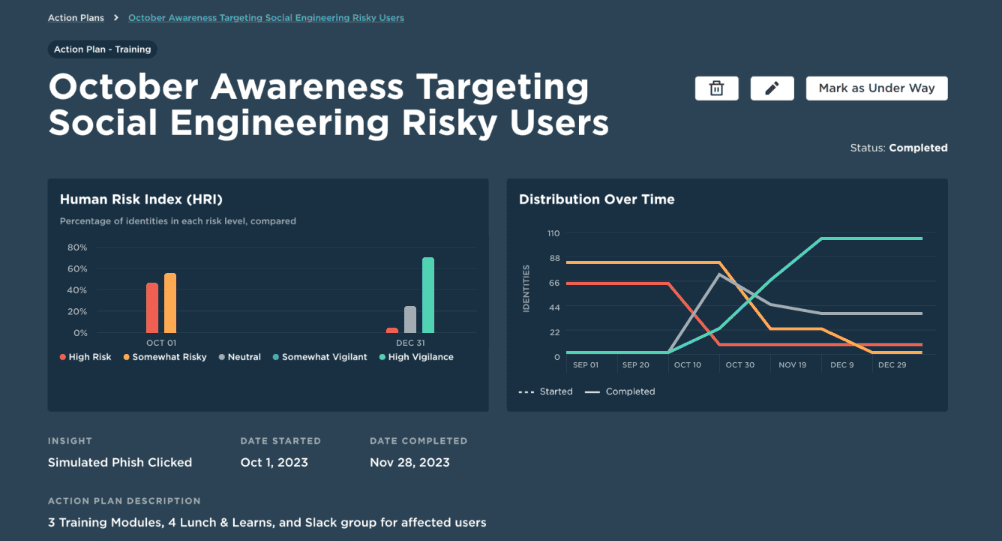
Some of Living Security’s customers saw significant results when identifying risky users and tracking before and after Cybersecurity Awareness Month efforts in October. Results include:
- A 40% drop in click rate among high-risk roles
- A 3x increase in phish reporting
- A measurable bump in password manager usage and MFA enablement
That’s not just awareness, that’s transformation.
This is not aspirational—it’s operational!
You already have:
- The tools
- The data
- The team
Now it's time to drive change.
Deploy Realistic, AI-Powered Simulations
Threat actors are using AI to create highly convincing phishing emails, deepfake videos, and voice scams. Your defense must be just as sophisticated. Standard phishing simulations with obvious red flags are no longer enough to prepare your employees for the attacks they will face. It's time to move beyond generic templates and deploy simulations that accurately reflect the current threat landscape. This means testing your team's resilience against AI-generated attacks that are personalized, context-aware, and designed to bypass traditional defenses. The goal is not just to see who clicks, but to build critical thinking skills that help employees spot and report even the most advanced social engineering attempts. By using AI-powered simulations, you can create realistic scenarios that truly test your organization's human firewall.
Deliver Personalized, Role-Specific Content
A one-size-fits-all approach to security training is inefficient and ineffective. The C-suite faces different threats than your engineering team, and a new hire in marketing has different security responsibilities than a tenured finance manager. To change behavior, training must be relevant. By correlating data across behavior, identity and access, and threat intelligence, you can identify which individuals and departments are most at risk and what specific behaviors need to be addressed. This allows you to deliver targeted, role-specific content that resonates with each employee. Instead of a generic annual training module, imagine delivering a short video on wire transfer fraud exclusively to the finance team. This personalized approach respects employees' time, increases engagement, and drives measurable risk reduction.
Provide Just-in-Time Training Nudges
Secure habits are not formed during a single training event; they are built through consistent reinforcement. The most effective time to correct a risky behavior is in the moment it occurs. Instead of waiting for a quarterly report to flag a problem, you can provide immediate, contextual guidance. This is where just-in-time training nudges become a powerful tool. For example, if an employee attempts to use an unsanctioned application or clicks on a simulated phishing link, the Living Security platform can autonomously deliver a quick, actionable tip or a link to a relevant policy. These micro-interventions are not punitive. They are supportive, guiding employees toward more secure decisions in their daily workflow and turning potential security incidents into valuable learning opportunities.
Your Next Steps Toward Real Behavior Change
Living Security’s Unify equips you with:
- Customized dashboards
- Risk-aligned campaign content
- Strategic planning and peer support
Choose a path that will make the most impact for you and your organization.
| Phase | Toolkit Component | October Basics | October Rewired |
|---|---|---|---|
| Risk Identification | Human Risk Assessment Correlated human risk insights delivered through Living Security’s Unify—powered by your existing phishing and email data—to identify high-risk users. | ● | |
| Expert-Backed Insight Reports Living Security’s HInT experts supercharge your Unify report with human intelligence—delivering clear, expert-backed recommendations to eliminate your organization’s greatest risks. | ● | ||
| Planning | Risk-Based Engagement Content Attention-grabbing materials like puzzles and games, and quick-hit videos tailored to drive awareness exactly where your employees need it most. | ● | ● |
| Execution | Speakers Schedule a sought-after speaker with fascinating topics | ● | ● |
| Campaign in a Box Leverage weekly materials with blog posts, email messaging, chat communications, and more | ● | ● | |
| Promotional Assets & Campaign Guides Easy-to-use templates and campaign plans to boost employee participation and highlight your cybersecurity month success. | ● | ● | |
| CyberEscape Online Interactive risk challenges and simulations specifically crafted to test and reinforce key cybersecurity topics in an engaging storyline. | ● | ● | |
| Interactive Experience Participate in a family-friendly event that brings fun and learning to everyone. | ● | ● | |
| Reporting | Expert-Backed ROI Report Prove ROI, show impact, and make the case for future investment in human risk management—with no fluff, just results. | ● | |
| Expert-Backed Impact Report Actionable insights and success metrics delivered by Living Security’s HInT experts after your Cybersecurity Awareness Month activities, tracking behavior change, measuring risk reduction, and seeing what worked. | ● |
This October, don’t just raise awareness. Raise the bar. Contact a Living Security representative to get started.
Frequently Asked Questions
How is a Human Risk Management (HRM) approach different from traditional security awareness training? Think of it as the difference between a yearly check-up and a continuous health monitoring plan. Traditional security awareness is often a once-a-year, one-size-fits-all event focused on compliance. Human Risk Management is a continuous, data-driven process that identifies your most vulnerable people and riskiest behaviors in real time. It moves beyond simple participation metrics to focus on measurable risk reduction, using targeted interventions to stop threats before they cause harm.
My team is already overwhelmed. How does this data-driven approach save time instead of creating more work? This is a fair question. Manually trying to connect the dots between different security tools is a massive time sink. The goal of a modern HRM platform is to automate that heavy lifting. Instead of your team spending hours sifting through data from your phishing simulator, identity systems, and threat feeds, our platform correlates those signals for you. It pinpoints exactly who to focus on and recommends the most effective action, freeing your team to execute strategic interventions rather than getting lost in analysis.
You mention moving beyond click rates. What are some concrete examples of metrics that show real risk reduction? Click rates only tell part of the story. To demonstrate real impact, we focus on metrics that reflect positive behavior change. This includes tracking the speed and accuracy of phish reporting, measuring a decrease in risky actions among specific high-risk groups, and monitoring the adoption of key security tools like MFA and password managers. When you can show that your most targeted employees are reporting threats faster and your finance team has fully adopted MFA, you’re proving you’ve reduced risk, not just completed a training module.
How can we effectively train employees to spot AI-generated threats when they are so convincing? Relying on employees to spot flawless fakes is no longer a realistic strategy. The focus must shift from simple identification to building core security habits. The most critical habit is verification. We need to cultivate a culture where it is standard practice to confirm unusual or high-stakes requests using a separate communication channel, like a quick phone call or a direct message. This turns security from a memory test into a reliable, repeatable process that works even when an attack is perfectly crafted.
We have policies for AI tools, but how can we know if people are actually following them? Policies are only effective if you have visibility into behavior. Without it, you're essentially hoping for the best. An HRM platform provides this visibility by analyzing data signals that indicate when employees might be using unsanctioned AI or inputting sensitive data into public tools. When the platform identifies this behavior, it can autonomously deliver a just-in-time training nudge, reminding the employee of the policy in their moment of need. This turns a potential data leak into a valuable, real-time coaching opportunity.
Key Takeaways
- Modernize your defense for AI-driven threats: Attackers use AI to create hyper-realistic phishing and deepfake scams, so traditional awareness training is no longer enough. Your strategy must evolve to predict and prevent these sophisticated attacks before they cause damage.
- Focus on risk reduction, not just participation: Shift your success metrics from simple completion rates to measurable changes in behavior. Use data from your existing security tools to identify high-risk individuals and prove your program's value by tracking prevented incidents.
- Personalize training to change behavior: Replace generic, one-size-fits-all training with targeted content. Deliver role-specific simulations and just-in-time nudges based on correlated risk signals to build secure habits that actually stick.