

Blogs 
May 20, 2024
By Crystal Turnbull
Director of Marketing at Living Security · LinkedIn
Advance Your Career in Management: A Security Pro's Guide
The definition of leadership is changing. Today’s workforce values mentorship, clear communication, and a positive culture over a top-down management style. For security professionals, this presents a massive opportunity. Your technical expertise is the foundation, but your ability to understand people, influence behavior, and build a resilient security culture is what makes you a true leader. Excelling in this area requires moving beyond intuition and using data to understand human risk. By leveraging a Human Risk Management framework, you can gain deep insights into your organization's behavioral dynamics, allowing you to build a stronger program and demonstrate the sophisticated skills needed to advance career in management.
Leveraging Human Risk Management for your Career Advancement
Securing a promotion in any professional field requires strategic planning, consistent effort, and effective communication of accomplishments. As someone leading Security Awareness and Training, understanding how Human Risk Management (HRM) can aid in this progression is pivotal.
There is a great article published by Ruchi Sinha, PhD, Associate Professor of Organizational Behavior at the University of South Australia Business School, featured in the Harvard Business Review, where she creates a roadmap for earning a promotion in various roles.
In this instance we have tailored these insights to focus on the domain of Security Awareness and Training. Read a summary below of the key steps you can take.
Or for an in-depth look, download the full white paper here.
Understanding the Modern Management Landscape
To move up the ladder, you first need to understand its changing shape. The traditional path to leadership is evolving, driven by new expectations from the workforce. For security professionals, this shift presents a unique opportunity. Excelling in your career is no longer just about technical expertise; it’s about understanding people, motivations, and the very nature of human risk. By grasping these modern dynamics, you can position yourself not just as a security expert, but as a strategic business leader who understands how to protect the organization’s most valuable asset: its people.
This new landscape requires a proactive approach to career development. Instead of waiting for opportunities, you can create them by demonstrating a deep understanding of the cultural and behavioral trends shaping today’s companies. Recognizing how leadership is being redefined allows you to align your skills and contributions with what the organization truly values. This means focusing on how your work in security awareness directly impacts business outcomes, employee satisfaction, and overall organizational resilience, making you an indispensable part of the company’s future.
Shifting Perspectives on Leadership
The concept of leadership is undergoing a significant transformation. Younger generations in the workforce are not just looking for a paycheck; they are seeking a "trifecta of meaningful work, good pay, and personal well-being," according to research from Stanton Chase. This means the old command-and-control style of management is losing its effectiveness. Aspiring leaders, especially in a critical field like security, must now also be mentors, communicators, and advocates for their teams. Understanding this shift is the first step toward cultivating a leadership style that attracts and retains top talent while building a robust security culture.
Why Younger Generations Are Redefining Success
It’s not that younger professionals lack ambition; they simply define success differently. The corner office and executive title are less appealing if they come at the cost of burnout and a lack of purpose. For security awareness professionals, this is a critical insight. To lead effectively, you must show how your program contributes to a positive and secure work environment, one that respects employee well-being. By framing security not as a set of restrictive rules but as a shared responsibility that enables the business to thrive, you align your goals with the values of the modern workforce, making your leadership more impactful.
The Growing Importance of Soft Skills
In this new era, soft skills have become paramount. The same Stanton Chase report found that over 85% of millennials and Gen Z believe skills like communication, leadership, and empathy are vital for career growth. As a security professional, your ability to influence behavior and foster a security-conscious mindset depends heavily on these abilities. Technical knowledge can identify a threat, but empathy and clear communication are what convince an employee to change their behavior. Mastering these skills is essential for managing human risk and demonstrating your readiness for a larger leadership role.
Strategic Career Planning for Security Professionals
Advancing your career requires more than just doing your job well; it demands a strategic plan. For those in security awareness and training, this means translating your efforts into a clear narrative of value and risk reduction for the organization. You need to think like a business leader, identifying where you can make the most significant impact and ensuring that impact is visible to decision-makers. This involves understanding the internal structures of your company, actively seeking out environments that foster growth, and being open to diverse career paths that build on your unique skill set.
A key part of this strategy is leveraging data to tell your story. Instead of simply reporting on training completion rates, you can demonstrate a measurable reduction in risky behaviors. By correlating data across human behavior, identity and access, and threat intelligence, you can pinpoint specific areas of risk and show how your initiatives have strengthened the organization’s security posture. This data-driven approach transforms your role from a compliance function to a strategic one, providing the concrete evidence needed to justify your advancement.
Understanding Corporate Structures and Job Levels
Every organization has a system for classifying roles, often based on factors like scope, responsibility, and required skills. According to Deel, this "job level classification" creates a framework for career progression. To move to the next level, you must demonstrate that you are already operating with the skills and impact required for that role. For a security awareness professional, this could mean expanding your influence from a single department to the entire enterprise, or shifting from executing campaigns to designing a comprehensive human risk management strategy that aligns with executive goals.
Choosing the Right Environment for Growth
Your environment plays a massive role in your career trajectory. As one Reddit user wisely advised, you should actively seek out companies known for internal growth and be prepared to move on if those opportunities don't exist where you are. Look for organizations that invest in a proactive security culture and provide their teams with modern tools to predict and prevent incidents. A company that embraces a forward-thinking approach to Human Risk Management is more likely to recognize and reward individuals who can effectively reduce that risk and contribute to the business's strategic objectives.
Exploring Alternative Career Trajectories
The path to leadership isn't always a straight line. Sometimes, the best way to advance is to broaden your expertise. For instance, pursuing an MBA can equip you with the business and financial language needed to communicate with the C-suite. This allows you to frame security initiatives not as costs, but as investments that protect revenue and brand reputation. By combining your deep knowledge of human risk with a strong understanding of business operations, you position yourself as a versatile leader capable of tackling complex organizational challenges far beyond traditional security awareness.
Step 1: Build Your Case for a Management Role
Promotions rarely occur spontaneously; they require careful preparation and evidence-based advocacy. Starting a dialogue with your manager six to nine months prior to seeking a promotion is best as everyone will need time to plan. This conversation should revolve around:
Clearly articulating the requirements for advancing to the next career level during routine one-on-one meetings.
Identifying key performance indicators (KPIs) crucial for the role.
Aligning your metrics with organizational objectives and presenting proactive strategies understood by the C-suite and Board
Implementing success metrics that reflect your contribution to fostering a culture of security consciousness and reducing organizational risk, backed by insightful data analysis.
Documenting achievements meticulously in a brag folder to substantiate your case during promotion discussions.
Define Your Path to a Leadership Position
At Living Security, we speak to hundreds of Security & Awareness Leaders on a monthly basis. We consistently hear that reporting (Board/C-suite and across the business) is very important, but the metrics they look for are narrowly focused and often revolve around:
Phishing: Open Rates, Click Rates, Report Rates, Credentials Harvested
Training: Completion Percentages, Engagement Rates, Blog Subscribers
- Culture: Cyber Champions Program Enrollment
Although these metrics are very important, they are not the metrics and focus areas to move the business forward. To make the next jump, you need to enhance the program and that starts by measuring outcomes and not activities.
Develop Essential Management and Leadership Skills
Shifting your program from activity-based metrics to outcome-focused results is a critical first step. The next is developing the leadership qualities to match that strategic mindset. Transitioning from an individual contributor to a manager requires a new focus on strategy, communication, and team development. It’s a significant change, and it’s understandable why some professionals hesitate. Many have seen their own managers struggle with burnout, which makes them reluctant to pursue leadership roles. To succeed and avoid those same pitfalls, you must intentionally build your management capabilities through structured learning and professional development that prepares you to lead with confidence.
Formal Education for Advancement
One of the most effective ways to build a foundation for leadership is through formal education. Pursuing a degree in management or a Master of Business Administration (MBA) equips you with the business acumen and strategic language that resonates with executives. These programs teach you to think about budgets, resource allocation, and organizational goals in a way that extends far beyond daily security tasks. This education enables you to translate your team's security contributions into measurable business impact, strengthening your case for resources and clearly demonstrating your value. This formal training is often a key differentiator that can help you advance your career and stand out among your peers.
Key Professional Certifications in Security
If a full degree program isn't the right path for you, professional certifications offer a targeted way to validate your expertise and readiness for management. While general project management credentials are useful, security-specific certifications carry significant weight with leadership. Certifications like the Certified Information Systems Security Professional (CISSP) are often considered a baseline for senior roles. For aspiring managers, the Certified Information Security Manager (CISM) is even more relevant, as it specifically covers governance, risk management, and program development. Earning these credentials demonstrates a deep commitment to the field and provides a recognized framework for leading security initiatives, making you a more credible and compelling candidate for promotion.
Quantify Your Impact with Human Risk Metrics
HRM programs and platforms enable SAT leaders to extend the measurement and reporting of key metrics beyond phishing, training, and culture. Risk can also be quantified by:
Access Level: which groups or employees have elevated access to sensitive information
Departments: which teams, departments, or office locations are at elevated risk
Security Risks: which groups are at heightened risk of data, identity, malware, and/or social engineering threats
Key Human Risk Metrics to Start Tracking Now
If the business is concerned about their Cyber Insurance Coverage, show them how your last campaign jumped MFA adoption by 37%, decreasing the likelihood of an incident. Show them how you have built a culture of ownership and accountability, e.g. increasing your report rate by 27%, because you communicate with your audience regularly and through a variety of channels (email, Slack, Teams, etc.). When you can tie back your value to the business objectives, you are viewed differently.
Step 2: Track Your Wins in a Brag Folder
Now that you have a focus on larger organizational goals, the big first step is complete. Once you have achieved a major goal (defined by you and your manager), and have the data to back it up, it is time to start this conversation. To do this, you need to be able to show quantitative HRM metrics backing your value and growth within the organization.
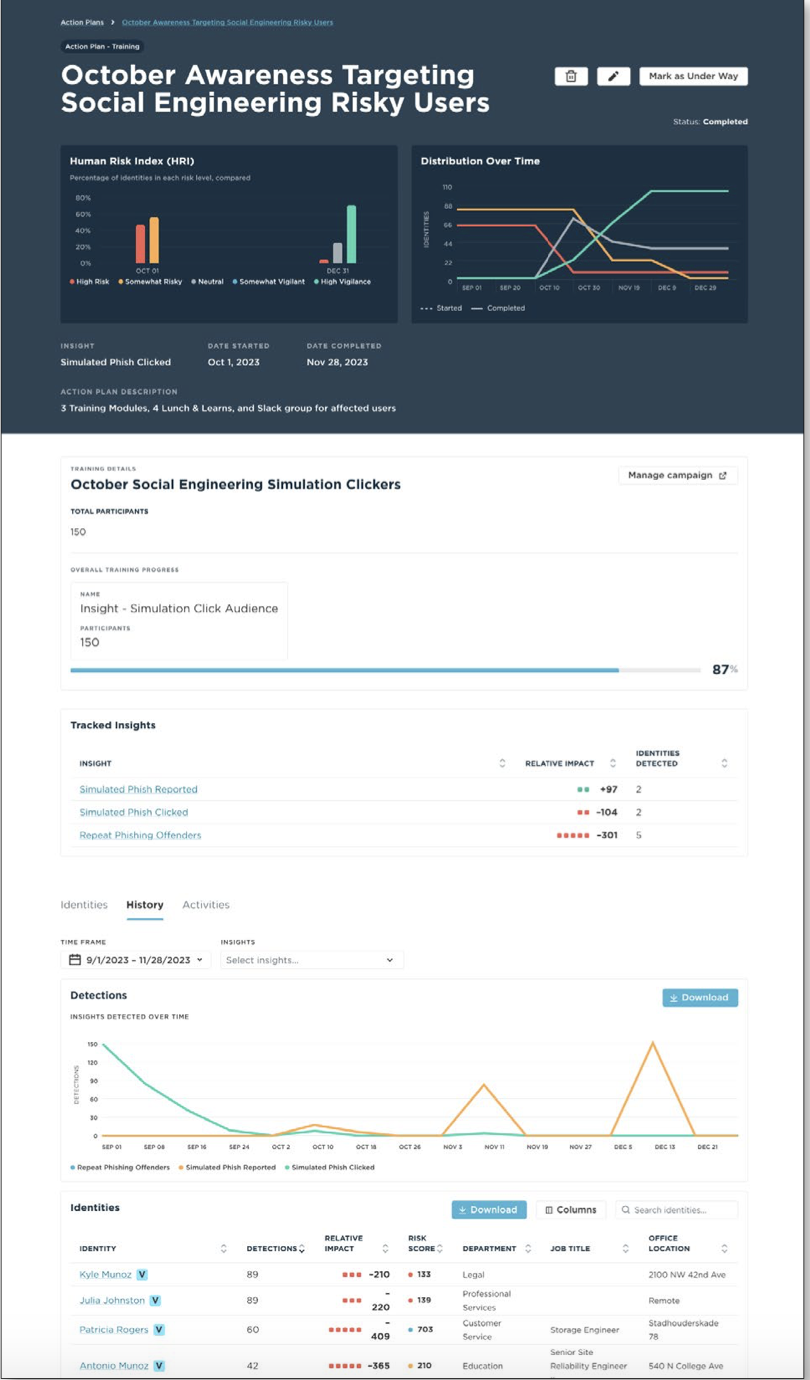
Here is an actual example from one of our customers. The client ran enterprise-wide phishing simulations in the summer months and came to the conclusion, with their CISO, that they need to focus their program efforts on a specific risk group based on three data points:
• Privileged users (IAM tool data)...
• Who have clicked on a simulated or real phish (Phishing data), and... • Who been heavily targeted (Email Security data)
The Director of Training and Awareness came up with a proposed campaign for October with a focus on the risk cohort they identified. The program would consist of:
A Slack Message, notifying the group of an upcoming training they will be enrolled in
A Slack invite to one of four lunch and learn sessions that will cover two major areas:
• The responsibility that comes with having elevated access
• Not just how to spot a phish but the importance to the security team and company of reporting the phish.
Enrollment into three micro learning videos, each one minute, on the topics covering privileged access and spear-phishing.
Turning Your Action Plan into Measurable Results
Here is the outcome of that work targeting 150 High Risk Users who fit their risk profile and the results that went straight into the “brag folder.”

By November 28, they only had one user of the 150 repeat click
All 150 users completed at least one of the two actions: lunch and learn or video modules
All 150 users over the next two months REPORTED at least one suspicious email (real or simulated) - moving high risk users into the vigilant category.
The data above does two things:
• Shows that a focused training program can shift behavior
• Demonstrates a resilient culture, not based on surveys, but based on users understanding their risk, their willingness to learn in short stints, and adopting their learning into their day to day work.
Our client found a problem the CISO deeply cared about. They created a plan to drive this risk down. Then they had the metrics to prove that the efforts worked and now they have a compelling action plan to run again when new users fit this same profile in the future!
Proactively Navigating Your Workplace
Finding Mentors in Senior Roles
To move into leadership, it helps to learn from those who have already made the journey. Seeking out mentors in senior roles provides a direct line to the insights you need to advance. A good mentor can offer more than just career advice; they can help you understand the unwritten rules of your organization and the specific challenges of leadership within the security field. They can show you how to translate your team's tactical wins into strategic business outcomes that resonate with the C-suite. This guidance is invaluable for learning how to frame your contributions, like reducing human risk, in a way that demonstrates clear value and readiness for a management position.
How to Advance with an Unsupportive Manager
A manager who doesn't support your growth can feel like a roadblock, but it doesn't have to halt your progress. Your career trajectory is ultimately in your hands. If your direct leader isn't advocating for you, you must become your own best advocate. Start by seeking out cross-functional projects that give you visibility with other leaders. More importantly, let data tell your story. Use a Human Risk Management platform to gather objective, quantifiable metrics that prove your program's effectiveness. When you can show a measurable reduction in risky behaviors by correlating data across identity, behavior, and threat intelligence, your impact becomes undeniable, with or without your manager's endorsement.
Recognizing the Signs of Career Stagnation
Feeling stuck is a common professional hurdle. You might notice the signs slowly: you’ve been in the same role for years, conversations about growth are consistently vague, and your daily tasks feel routine. When your job starts to feel like it’s on autopilot, it’s a clear signal that you're no longer being challenged. In a dynamic field like cybersecurity, stagnation isn't just boring; it's a risk to your professional relevance. Recognizing these signs is the first step toward taking action. It’s an opportunity to re-engage with your career plan, build a data-backed case for your advancement, and proactively seek the new challenges that will lead to growth.
Step 3: Make the Ask
Approaching your manager for a promotion requires confidence, supported by a compelling narrative of your accomplishments aligned with organizational objectives.
Emphasize:
Tangible outcomes of your initiatives, such as increased MFA adoption or decreased instances of sharing sensitive information.
Your proactive approach to identifying and addressing security risks, as evidenced by higher report rates of suspicious emails post-training.
Expressing readiness to assume greater responsibility and contribute meaningfully to organizational goals.
Sample Dialogue:
“I believe I’ve consistently met our shared expectations and contributed positively to our objectives. I am eager to take on more challenges and advance in my career. I welcome your guidance on how I can further contribute to our team and the organization as a whole.”
In essence, leveraging HRM practices entails strategic alignment of your achievements with organizational goals, effective communication of value propositions, and proactive engagement in career advancement discussions. By adopting this approach, security professionals can navigate their career pathways with confidence and competence.
Exploring High-Growth Management Opportunities
Once you begin building your case and tracking your wins, it's helpful to understand the broader landscape of available management opportunities. The technology and security sectors are not just growing; they are creating leadership roles that demand a new set of strategic skills. Knowing what these roles are and what the market looks like can help you better position your career trajectory and align your personal goals with the needs of the industry. This context is crucial for framing your ambitions and making a compelling case for why you are the right person to lead.
High-Paying Management Roles in Tech and Security
It’s no secret that management roles in technology and security are some of the most financially rewarding positions available. For instance, one report on high-paying management jobs highlights that top executive roles command significant salaries, reflecting the immense value organizations place on strategic leadership. Reaching these senior positions isn't just about years of experience; it's about demonstrating a deep understanding of business impact. Security leaders who can move beyond technical expertise and show how they proactively reduce organizational risk are the ones who ascend to these roles. This requires a combination of advanced skills, business acumen, and the ability to translate security initiatives into clear, measurable business outcomes.
Job Market Outlook for Management Positions
The demand for skilled managers is on a strong upward trajectory, and this growth is particularly pronounced in the security field. As organizations grapple with complex threats, specialized roles like Cybersecurity Manager are becoming increasingly critical. This expanding job market presents a significant opportunity for security awareness professionals who are ready to advance their careers. Companies are actively seeking leaders who can do more than just run training programs; they need strategists who can build resilient security cultures and manage human risk effectively. Demonstrating these capabilities is key to securing one of the many emerging leadership positions and proving your value to the organization.
Frequently Asked Questions
How do I shift from reporting on activities, like training completion, to showing real business impact? Start by connecting your work to a specific business objective, such as reducing the risk of a data breach. Instead of just reporting that 90% of people completed phishing training, show how that training led to a 27% increase in employees reporting suspicious emails. This demonstrates a change in behavior, not just a completed task. Correlating data points, for instance which employees have high access levels and are also being targeted by threats, allows you to create focused campaigns and show a measurable reduction in risk for the company's most vulnerable areas.
What's the first step I should take if I want a promotion in the next year? The best first step is to have a direct conversation with your manager about your ambitions. Schedule this talk six to nine months before you hope to be promoted. In this meeting, work together to define what success looks like for the next level. You should clearly outline the key performance indicators you need to hit and agree on the specific, outcome-focused metrics that will demonstrate your readiness for a management role. This creates a clear roadmap and ensures you are both aligned on the expectations from the start.
My manager doesn't seem to support my career goals. How can I advance anyway? If your direct manager isn't your advocate, you have to become your own. The most powerful way to do this is by letting data speak for you. Use metrics to build an undeniable case for your program's success, focusing on how you've reduced organizational risk. Seek out opportunities to work on projects with other teams and leaders to increase your visibility. When you can present objective, quantifiable results that show your impact on the business's security posture, your contributions become difficult to ignore, regardless of your manager's support.
What are the most important skills I need to develop to become a security leader? Technical expertise is your foundation, but leadership requires a different skill set. Focus on developing strong communication and empathy. You need to be able to influence behavior and explain complex security concepts in a way that resonates with everyone, from a new hire to the C-suite. Beyond that, cultivate your strategic thinking. Learn to connect your security initiatives to broader business goals, framing them as investments that protect the company's bottom line and reputation, not just as operational costs.
How can I quantify the value of my program without a dedicated HRM platform? While a dedicated platform simplifies the process, you can start by manually correlating data you likely already have access to. For example, you can work with your IT or identity teams to identify users with privileged access. Then, you can compare that list against data from your email security tools to see who is being heavily targeted by threats. This allows you to identify a high-risk group and measure the impact of a targeted training campaign on their behavior, providing a powerful, data-backed story for leadership.
Key Takeaways
- Lead with a Human-Centric Approach: Advance your career by moving beyond technical skills to focus on understanding and influencing human behavior. Modern security leadership requires empathy and strong communication to build a resilient culture, which is the foundation of effective Human Risk Management.
- Translate Security Efforts into Business Value: Shift your reporting from activity-based metrics, like training completion rates, to outcome-focused results that executives understand. Use data to show how your programs reduce specific risks, for example, by increasing MFA adoption by 37% or decreasing phishing clicks within a high-risk group.
- Strategically Plan and Document Your Wins: Proactively manage your career path by creating a data-backed narrative of your accomplishments. Use quantifiable HRM metrics to track your impact, align your goals with organizational objectives, and build a compelling case for your promotion.