Under the Hood: The Architecture of an AI-Native HRM Platform
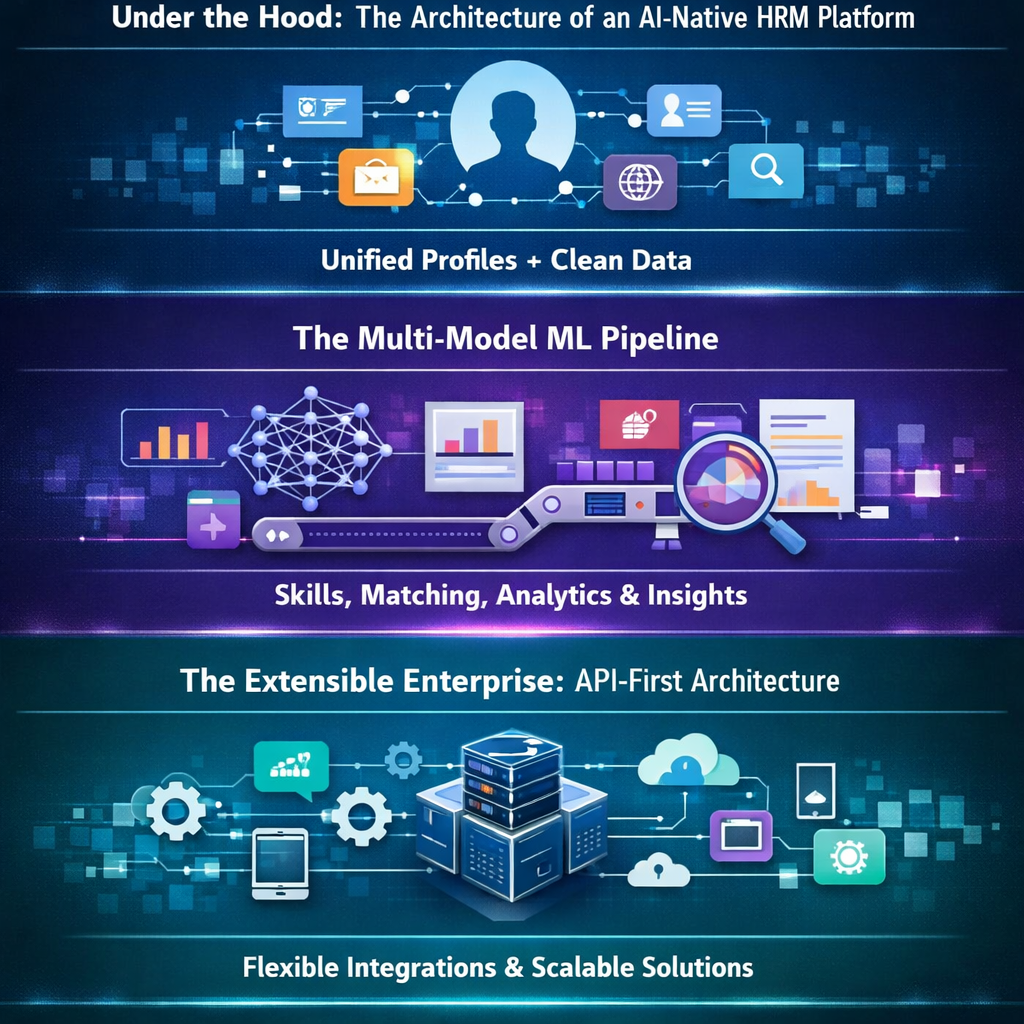
The Data Foundation: Identity and Entity Resolution
Attempting to run machine learning on raw, un-unified event logs is an exercise in futility. The prerequisite for any meaningful behavioral analysis is Identity and Entity Resolution. A robust HRM platform uses a graph-based model to resolve disparate events from hundreds of sources (EDR, IDP, Web Gateway) into a single, persistent user entity. Without this foundation, you are analyzing noisy events, not actual user behavior.
The Multi-Model ML Pipeline
Effective human risk analysis is not the result of a single algorithm. It is a progressive pipeline where the output of one model becomes the input for the next:
- Dynamic Baselining: Continuous recalculation of "normal" behavior for every individual and their specific peer group.
- Supervised Pattern Recognition: Identifying the specific signatures of high-risk activities, such as impending data exfiltration.
- Explainable AI (XAI): Using SHAP (SHapley Additive exPlanations) to deconstruct risk scores. This ensures the output is not just a number, but a transparent, evidence-based explanation (e.g., "Score is 850 due to an unsanctioned app install and a 40% increase in after-hours logins").
The Extensible Enterprise: API-First Architecture
A modern HRM platform must function as the central nervous system for human risk data. This requires an API-first approach built on three pillars:
- Inbound Signal Ingestion: Supporting 10,000+ requests per second to ingest real-time data from the existing security stack.
- Bi-Directional Automation: Triggering automated, cross-platform responses (e.g., an API call to Okta to restrict an account or a webhook to Slack to send a micro-learning "nudge").
- GraphQL Data Enrichment: Allowing security teams to use flexible queries to pull risk data into custom BI tools like Tableau or PowerBI for advanced enterprise visualization.
Securing the New Attack Surface: AI Agent Monitoring
Architecture must evolve to treat AI agents as first-class citizens in the security model. This involves:
- Credential Monitoring: Tracking API key and token usage patterns to detect potential agent compromise.
- Contextual Access Control: Implementing real-time controls that evaluate the risk level of both the human user and the AI agent they are utilizing before granting access to sensitive data repositories.
We're Always Looking for Talent
Whether you’re building a welcome mat for your company or a clean, corporate portfolio, Evolve has your design needs covered.
.svg)