Traditional compliance training treats all employees the same. This playbook provides a data-driven framework to identify high-risk cohorts—from Social Engineering and Account Compromise to Insider Threats—and deploy precise interventions that reduce incident probability by addressing the specific behaviors of your riskiest 10%.

Beyond generic phishing simulations, this play focuses on the intersection of external threats and high-value access. Identify your "heavily targeted" cohort, those receiving 5+ malicious emails monthly, and the privileged users who act as a doorway to your "crown jewels". Move from measuring vanity click rates to driving a 10% increase in reporting within your most vulnerable populations.
Insider risk isn't just about malice; it’s about visibility into unintentional negligence. This play provides a framework to monitor "leaver status" and reorganization signals paired with anomalous file transfers. By building behavioral baselines, you can reduce anomalous data movement in critical roles by 15% and identify the top 10% of employees with elevated risk indicators before a policy violation becomes a breach.
Attackers using valid credentials bypass traditional detection; this play treats identity as a human-layer challenge. Specifically target the "value + exposure" convergence: employees with elevated access who lack MFA or exhibit anomalous login patterns. Use this play to increase MFA coverage in privileged populations from 85% to 98% and slash remediation time from 10 days to under 48 hours.
Data leakage is often driven by productivity shortcuts rather than bad intent. This play identifies employees who consistently bypass controls by using unsanctioned apps (Shadow IT) or sharing sensitive files to personal domains. Shift from reactive DLP blocking to a proactive strategy that reduces unauthorized external sharing by 20% and shadow IT usage by 30%.
Malware is a human risk vector that succeeds when employees bypass browser warnings or run unverified executables. This play moves beyond volume-based antivirus alerts to identify the specific employees responsible for repeat infections. Implement targeted interventions to reduce executable downloads from unknown sources by 30% and decrease repeat malware-triggering behavior by 50% within 90 days.




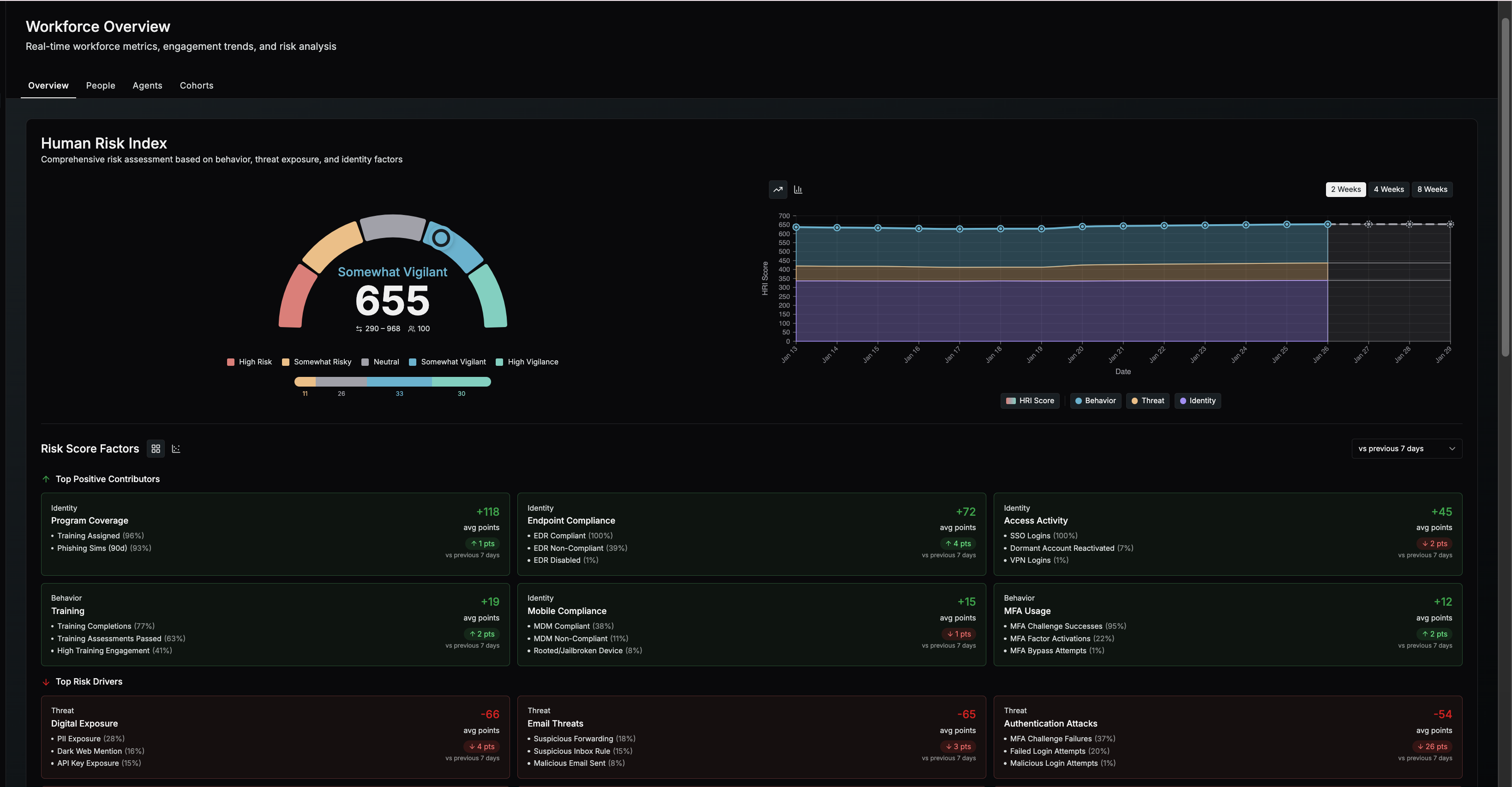
Phishing simulations and training completions show activity, not outcomes. They do not explain where human risk is actually increasing or how exposed the business really is. Living Security correlates behavior, threat, and access data into a single view so you can see risk clearly and act faster without manual reporting.
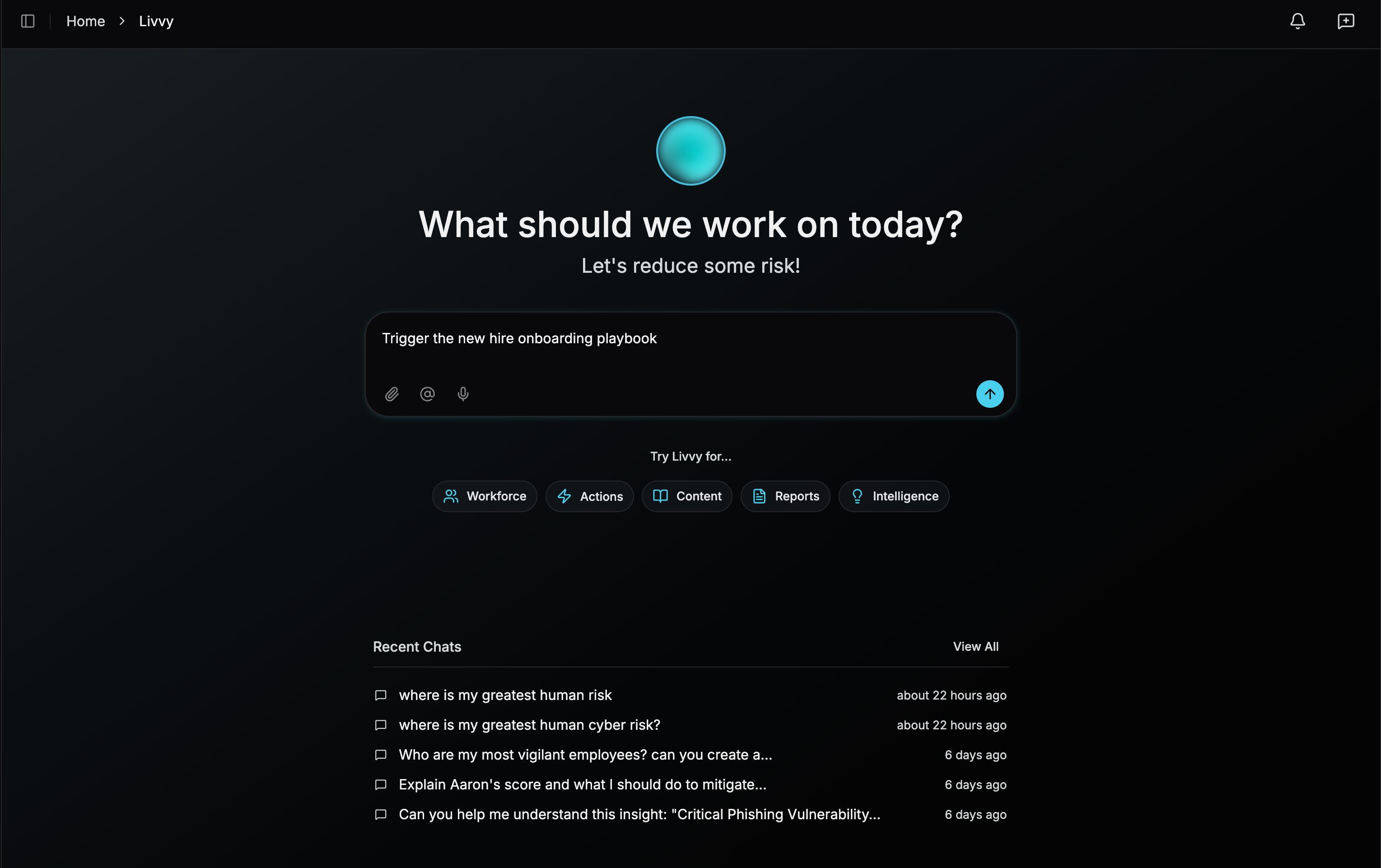
Seeing risk is only valuable if you can act on it quickly. Living Security makes it easy to move from insight to action in minutes. With Livvy, you can ask questions in plain language, instantly see where human cyber risk lives and why it is changing, and trigger the right actions without leaving the platform.
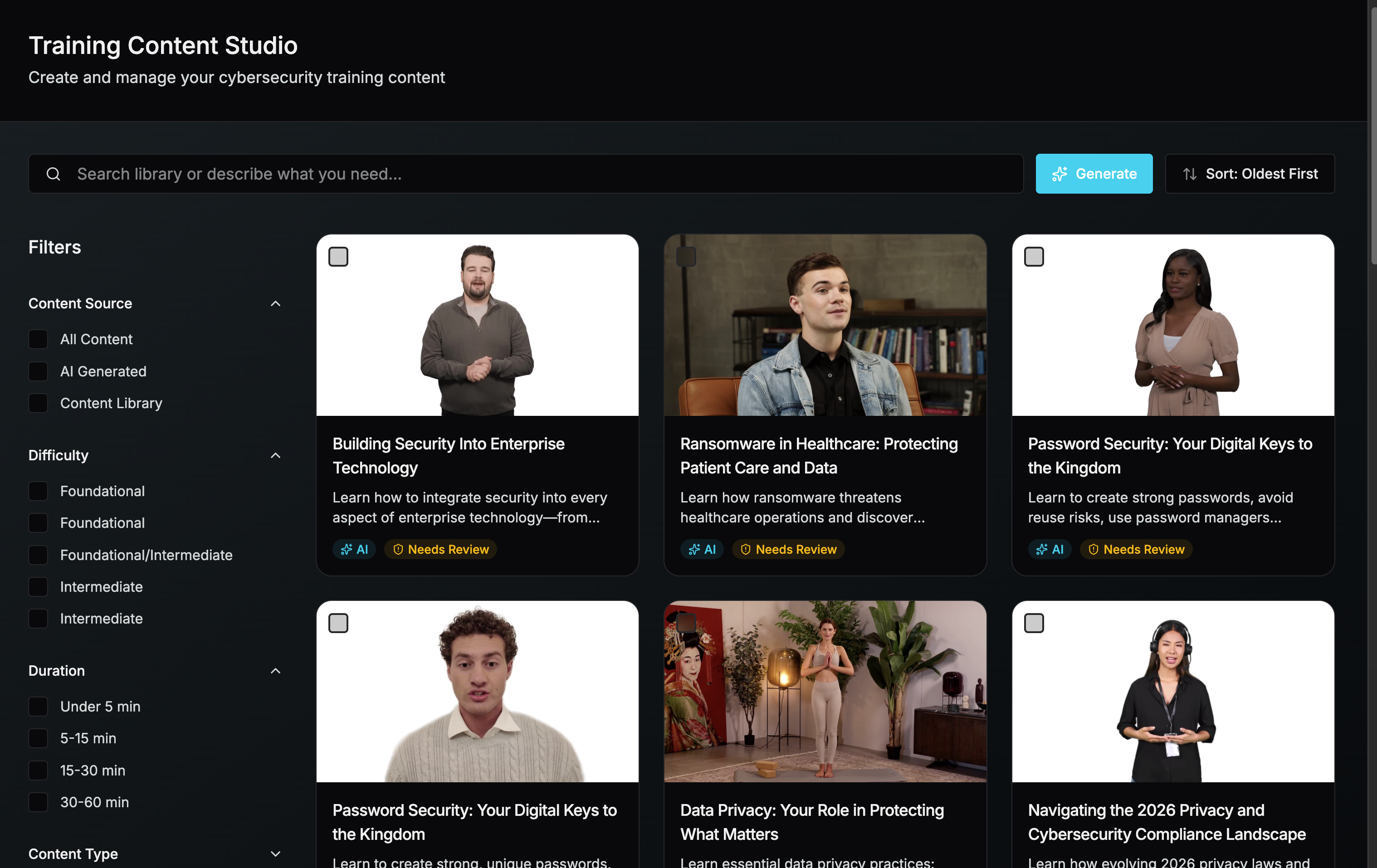
Broad training and phishing happen when teams lack visibility and control. Living Security enables targeted mitigation across the enterprise. Using cohort-level risk insights, you can deliver customized phishing and training by role, region, and risk level. AI-generated content enables scalable personalization, allowing every user to receive the right intervention without manual effort.
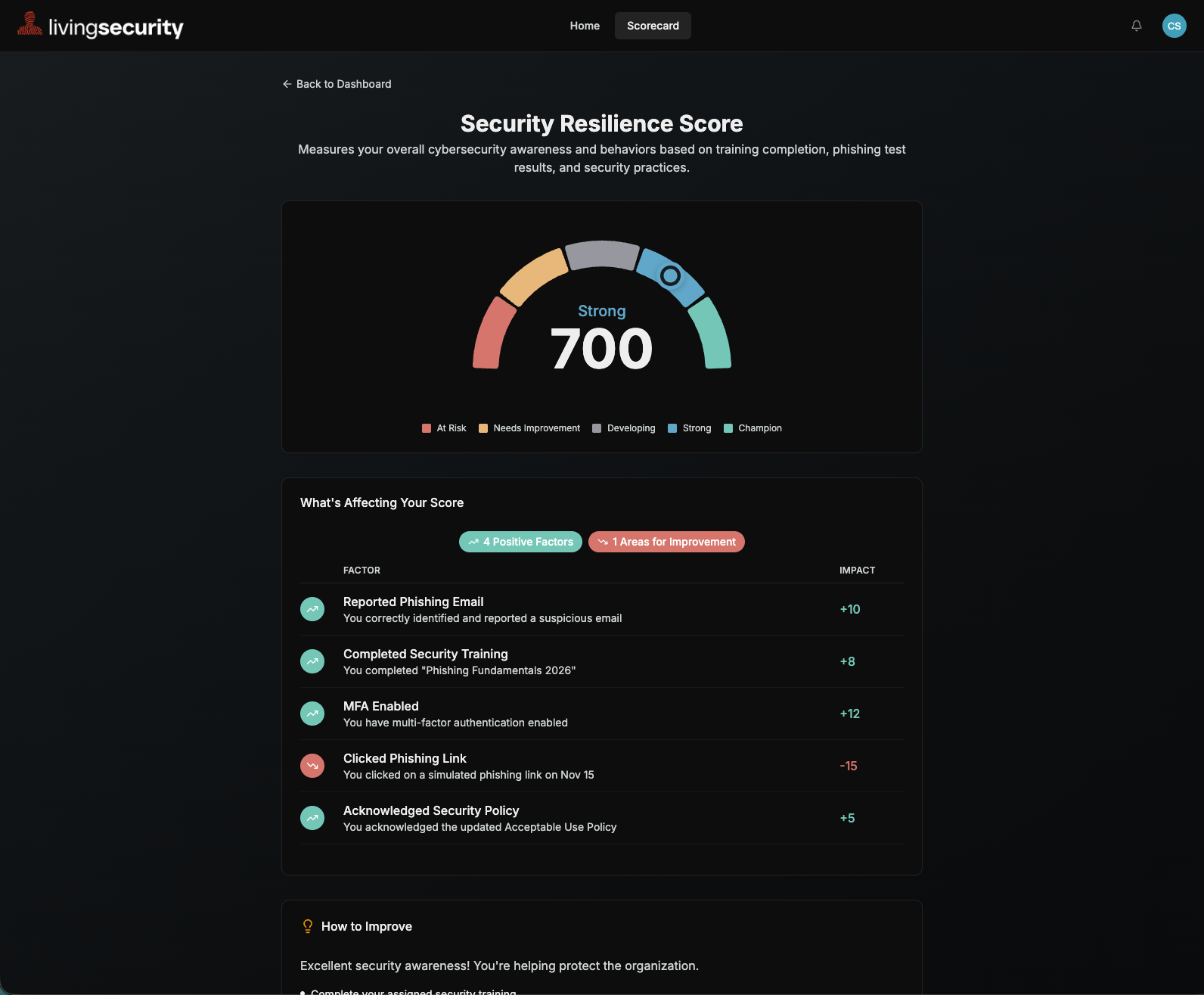
A strong security culture is built through clarity, ownership, and reinforcement. When people can see how their actions impact risk, accountability follows, and behavior improves.
Living Security’s employee and manager scorecards make human risk visible at every level of the organization. Gamified scoring and progress tracking motivate participation and improvement. Employees know where they stand and how to get better. Managers can coach with confidence and reinforce the right behaviors. The result is a shared, performance-driven security culture that scales across the enterprise.
AI-native prediction, guided decisions, and automated action—all in one platform.
