Audio & Video Connectivity Errors for Teams: CyberEscape Online
Connection Test failing for Audio & Video? Here are some tips that can help.
🙇 For Participants
- Please allow access to your camera.
- Please allow access to your microphone.
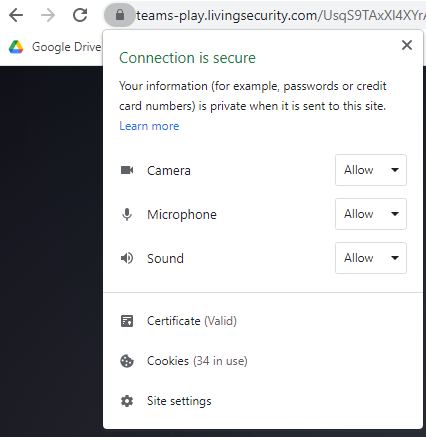
If you're failing these tests, you will need to give your browser access to the camera or microphone to pass. While you are not required to give your camera access to join the experience, your microphone is needed to be able to speak with other participants! To allow access, click the lock in the browser menu:
If the Microphone and Camera have been allowed, but you are still unable to join the session, click on the "Microphone" toggle within the Teams: CyberEscape Online experience to make sure there is an output device selected.
-1.png?width=670&name=image%20(9)-1.png)
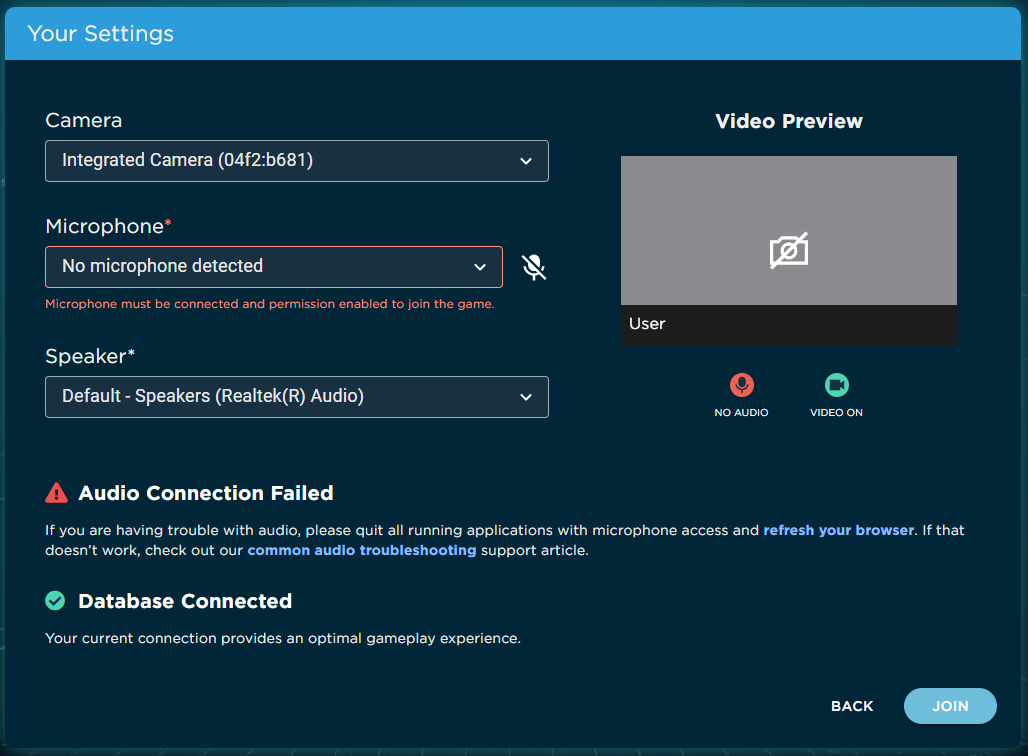
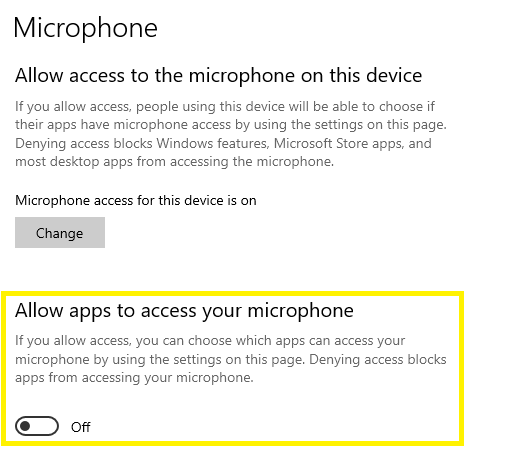
If no microphone is detected, your desktop/laptop Microphone privacy settings may be blocking access for the browser to access your microphone. To check your Microphone Privacy settings, go to your Microphone settings page and make sure the following option is toggled on.
While a speaker is not required since our experiences have video captions, make sure to also enable to hear others talk.
If any of the other tests are failing for you, or if audio issues persist, please contact your IT Team, Network Team, or Security Awareness Team for assistance.
💻 For IT
This section of the test checks your connection to Twilio. Run the compatibility tests here to ensure whitelisting was successful: https://test.livingsecurity.com/
- Twilio connectivity error
- UPD connectivity error
- TCP connectivity error
- Video turn error
🔁 Domains and Ports
If not already done so, the following domain and ports need to be whitelisted. Sometimes this can be done only via the network (especially if using a VPN), but firewalls or other security tools may need to be whitelisted too.
*.twilio.com
Ports used: 10,000 - 60,000 UDP/SRTP/SRTCP or TLS/443 or UDP/3478
Your firewall should allow outgoing TCP and UDP traffic to Twilio’s infrastructure, and allow return traffic in response.
If you prefer to whitelist individual IPs based on geographic location, you can use this article for reference: https://www.twilio.com/docs/video/ip-addresses
📖 Browser Specific Policies
Microsoft Edge and Google Chrome sometimes have browser policies enabled that can cause UDP traffic to be blocked. There is a way to bypass this by modifying the policy to use TCP while still maintaining the intended privacy measures.
- DisableNonProxiedUdp (disable_non_proxied_udp) = Use TCP unless proxy server supports UDP. This doesn’t expose the local IP address
🔒 SSL Bypass
Many security tools like ZScaler, Netskope, and Forcepoint have an optional setting that can make them act as an SSL Proxy. If your network security tool utilizes SSL inspection and you're having trouble getting these tests to pass, adding an SSL bypass rule can help resolve blocking or throttling issues. You can find more detailed information on what this means and how to do this in the following articles:
https://help.zscaler.com/zia/controlling-access-google-consumer-apps
https://help.zscaler.com/zia/about-ssl-inspection
https://help.zscaler.com/zia/configuring-ssl-inspection-policy