Cyber Guide Collection
Cyber Guide
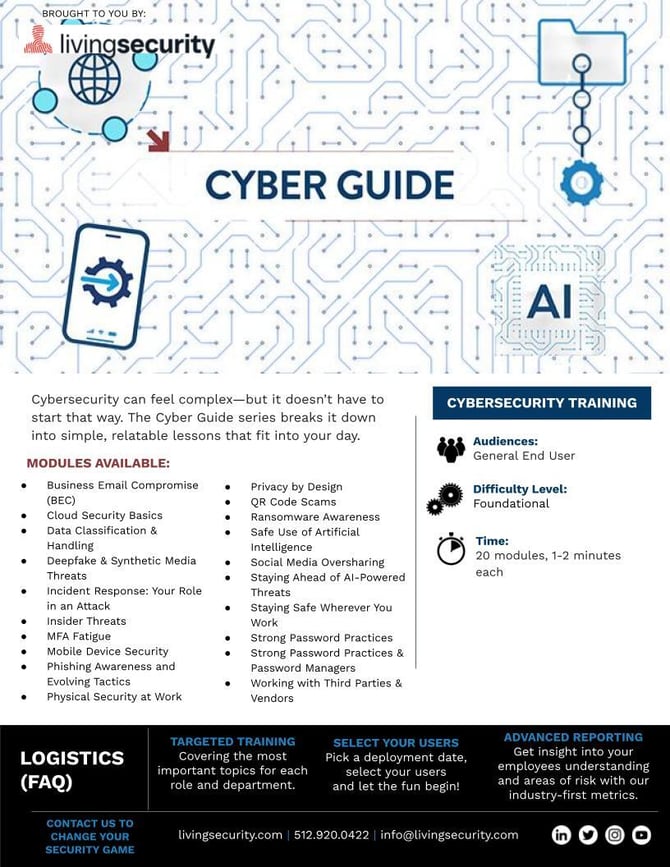
Audience: General End User (All)
Difficulty Level: Foundational
Time: 20 modules, ≈1-2 minutes each
Availability: Available on Training as Independent Modules. Do not need to be assigned or watched together, designed to stand independently.
Modules:
-
Business Email Compromise (BEC) (2:15 Video)
-
Cloud Security Basics (2:00 Video)
-
Data Classification & Handling (2:08 Video)
-
Deepfake & Synthetic Media Threats (1:52 Video)
-
Incident Response: Your Role in an Attack (1:40 Video)
-
Insider Threats (2:08 Video)
-
MFA Fatigue Attacks (1:43 Video)
-
Mobile Device Security (1:34 Video)
-
Phishing Awareness and Evolving Tactics (1:55 Video)
-
Physical Security at Work (1:45 Video)
-
Privacy by Design (1:47 Video)
-
QR Code Scams (1:44 Video)
-
Ransomewhere Awareness (2:10 Video)
-
Safe Use of AI (1:53 Video)
-
Social Media Oversharing (1:57 Video)
-
Staying Ahead of AI-Powered Threats (2:01 Video)
-
Staying Safe Wherever You Work (1:45 Video)
-
Strong Password Practices (1:53 Video)
-
Strong Password Practices & Password Managers (2:10 Video)
-
Working with Third Parties & Vendors (2:11 Video)
Trailer
Marketing Materials: Cyber Guide Marketing Kit
Major Themes: These quick, digestible awareness modules will introduce your end users to the basics of key cybersecurity concepts.
-
Business Email Compromise (BEC)
- Alternative Forms of Phishing, BEC, Executives, Sensitive Information
-
Cloud Security Basics
- The Cloud, Sensitive Information, MFA, Phishing, Strong Passwords & Passphrases, Incident Response
-
Data Classification & Handling
- Clean Desk, Compliance, Data Classification, Incident Response, Proper Document Disposal, Sensitive Information
-
Deepfake & Synthetic Media Threats
- Alternative Forms of Phishing, BEC, Identity Theft, Incident Response, Sensitive Information
-
Incident Response: Your Role in an Attack
- Compliance, Incident Response, Malware, Phishing, Sensitive Information
-
Insider Threats
- Compliance, Data Classification, Incident Response, Insider Threat, Phishing, Sensitive Information
-
MFA Fatigue Attacks
- Alternative Forms of Phishing, Incident Response, MFA
-
Mobile Device Security
- Incident Response, Malware, Mobile, Phishing, Sensitive Information, Updates
-
Phishing Awareness and Evolving Tactics
- Alternative Forms of Phishing (includes vishing and smishing), Phishing, Spear Phishing, Social Engineering
-
Physical Security at Work
- Tailgating, ID Badges, Clean Desk, Sensitive Information, Incident Response, Physical Document
-
Privacy by Design
- Sensitive Information, Privacy, Compliance, Data Classification, Encryption, Incident Response
-
QR Code Scams
- Alternative Forms of Phishing, Incident Response, Mobile, Sensitive Information
-
Ransomewhere Awareness
- Backup, Incident Response, Malware, Phishing, Ransomware, Sensitive Information
-
Safe Use of AI
- AI, Compliance, Data Classification, Incident Response, Sensitive Information
-
Social Media Oversharing
- Compliance, Secure Devices, Safe Surfing, Participation, Highly Visible Employee
-
Staying Ahead of AI-Powered Threats
- AI, Alternative Forms of Phishing, BEC, Identity Theft – Deep Fakes, Incident Response, Sensitive Information
-
Staying Safe Wherever You Work
- Incident Response, Mobile, Personal Devices, Sensitive Information
-
Strong Password Practices
- MFA, Sensitive Information, Strong Passwords & Passphrases
-
Strong Password Practices & Password Managers
- MFA, Password Managers, Sensitive Information, Strong Passwords & Passphrases
-
Working with Third Parties & Vendors
-
Alternative Forms of Phishing, Compliance, Incident Response, Sensitive Information, Vendor / Supply Chain
-
🔍 View Cyber Guide in your Living Security platform catalog here!