
Human Risk Management. Simplified.
Living Security unlocks new value from your existing security investments by integrating and correlating disparate behavioral data & events with identities.
- Identify those most at risk to cyberattacks.
- Protect with nudges, training, and AI orchestrations.
- Report results showing increased workforce vigilance.
Unify employees, managers, and executives to create a positive security culture that identifies risks and protects against them before breaches occur.
Explore Unify HRM PlatformEbook
HRM Maturity Model
Learn how to move from activities-based Security Awareness Training to Human Risk Management
linkWhitepaper
Forrester Wave Security Awareness and Training Solutions Whitepaper
See why Forrester named Living Security a leader in its most recent SAT Wave
linkInsights
Living Security Insights
See the full catalog of risks, behaviors, and integrations offered on the Unify HRM Platform
link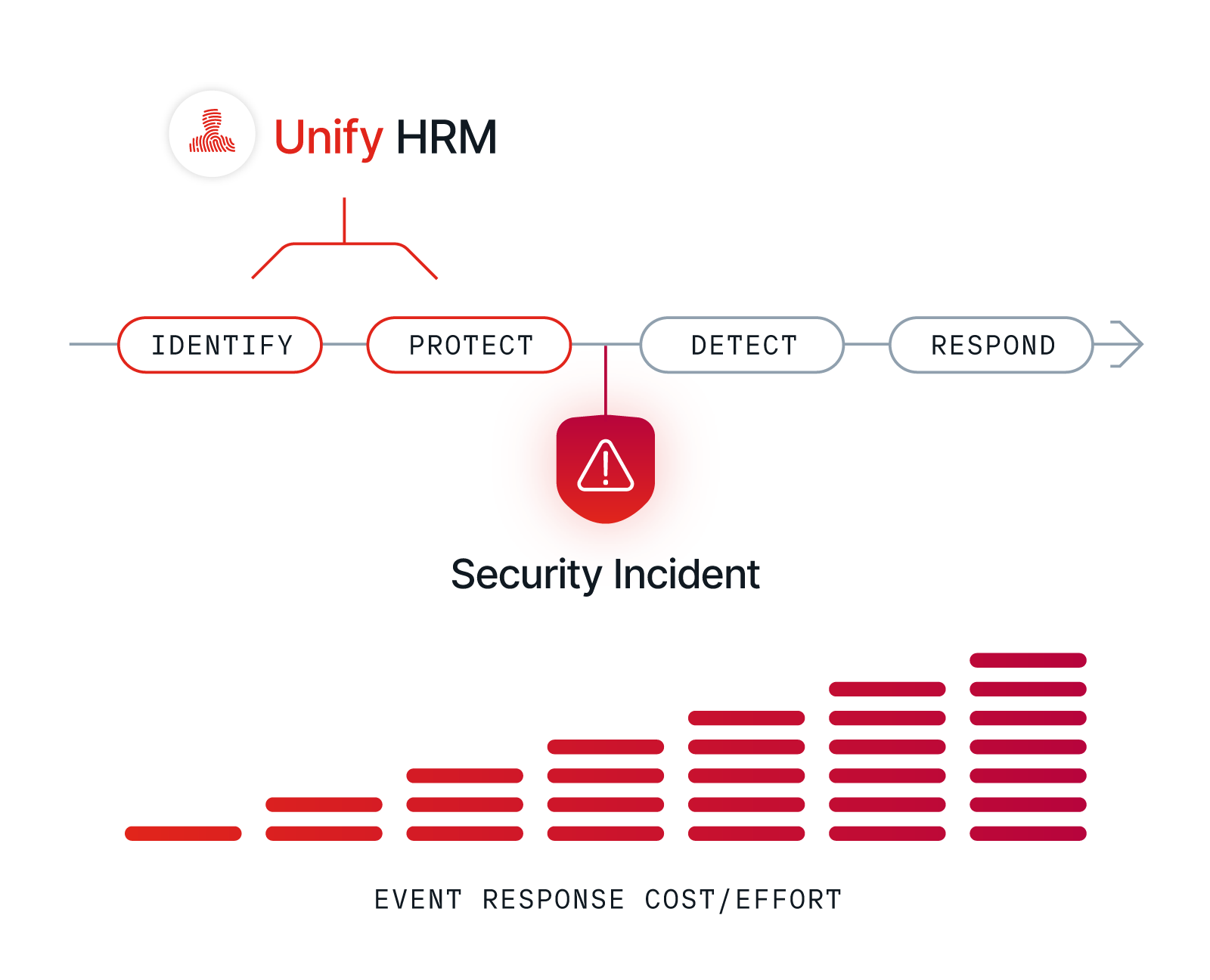
Empower your Workforce. Mitigate Risk. Embrace HRM.
Human Risk Management (HRM) is the process of identifying, assessing, and mitigating risks associated with human behavior in relation to an employee's use of technology.
The modern attack surface expanded with digital transformation and the post- pandemic shift to a remote or hybrid workforce. Today more than 89% of all security incidents involve a human element. Cybersecurity is not a technical challenge. It's a human challenge.
HRM transforms how CISOs, Security Awareness & Training, Governance, Risk & Compliance, and SOC & IR teams work together. With HRM they identify security vulnerabilities and protect from human risks to the “left of boom”, before an incident.
Learn More About HRM

The Unify HRM Platform:
Creating a Virtuous Cycle of Human Risk Management
Unify drives your security programming beyond traditional training, awareness, and phishing campaigns. It actively measures and monitors human behavior, identifying real risk to protect from incidents and policy violations in real time.
Combined with Living Security’s industry-leading training and phishing, Unify goes beyond compliance-based SAT to active risk reduction. With Unify you can easily deploy personalized nudges, training, and policy changes to those who need it and report reductions in risk over time.
Unify empowers employees, managers, and executives with actionable scorecards that foster a positive security culture, boost employee confidence, and drive safer, more vigilant security behaviors.
Explore Unify HRM PlatformLeading Organizations Trust Living Security
Living Security is a leader in the most recent Forrester Wave for Security Awareness and Training, is a pioneer in Human Risk Management, and is trusted by hundreds of organizations worldwide.

Feature
Human Risk Management Conference 2024
Join us for the 3rd Annual Human Risk Management Conference. Registration is now open.
Ready to see it in action?
Fortune 500 companies trust Living Security to deliver human risk management by using existing data to identify risky employees or teams and target immersive training to those who need it most, keeping organizations ahead of breaches and enabling them to track their progress toward a better security posture. This proactive, automated, efficient approach saves resources while keeping employees and data safe.
Schedule a meeting today and let's get started.










